Join devRant
Do all the things like
++ or -- rants, post your own rants, comment on others' rants and build your customized dev avatar
Sign Up
Pipeless API

From the creators of devRant, Pipeless lets you power real-time personalized recommendations and activity feeds using a simple API
Learn More
Search - "sensitive"
-
*client calls in*
Me: good morning, how can I help you?
Client: my ip is blocked, could you unblock it for me?
Me: certainly! What's your ip address? Then I'll have a look.
Client: I'm not giving you my ip?! That's too privacy sensitive.
Me: 😶
Me: 😶
Me: 😶
Me: sir, I'm very keen on my privacy myself but without that information I can't do much for you 😬
Client: ah so you're refusing to help me?
Me: not like that, it's just very hard to lift an ip block for me when I don't know the ip address.
Client: you just don't want to help, fine.
*click*
😶32 -
Meeting with asshole partner company CEO at restaurant.
Me: "I'm a bit worried about the bugs in your API. There are some ways to retrieve privacy sensitive info from public endpoints"
CEO: "Well, we're a rapidly growing startup!"
Me: "Uh... so?"
CEO: "So... Move Fast and Break Things! Priority is to improve our API further, and we'll fix bugs as they show up"
Me: "Maybe you should stop trying to emulate Zuckerberg in your management style. You know that even Facebook themselves admitted that their slogan was a retarded mistake"
Waiter shows up at table. CEO orders some overly expensive fish salad.
CEO: "Well, they have done something right... they're worth billions"
Waiter asks me: "And you sir, have you made your choice?"
Me: "Do you serve popcorn?"
CEO: "Popcorn for lunch?"
Me: "No, for your congressional hearing"16 -
PM: You know that screen that pops up at the start of the app asking for permission to access health data?
Me: Yeah the iOS HealthKit permission screen. What about it?
PM: Can you take that out. I don't think people are going to agree to it. I want people to use the app.
Me: Well we can't do that, apple says if we want to use HealthKit we have to ask for permission. We shouldn't be touching that data without permission anyway.
PM: Oh no permission is fine I get that, but is it not implied by downloading the app, its clearly a health app. I really don't want people to download it and then uninstall it because they don't like this.
Me: Not really, not everyone will know what data is needed, some of it might be sensitive to them.
PM: Nah I don't buy into that. I asked 5 of my friends on the golf course at the weekend and 3 of them said they wouldn't agree to it, thats 60% of our user base, we can't have that.
Me: ... ok, well I don't agree that your 5 friends is a fair sample to judge the whole world by, either way we have no choice.
Pm: No this isn't going to fly, can we not build our own HealthKit that doesn't have this kind of permission screen? Maybe we could start our own, and invite our partners to use it?
Me: ... no
Pm: why not? We'll have legal draw up something we put in the terms and conditions.
Me: ... it will take months to build for all the different types of devices we have, if they even let us get access to them, and then we will have a different standard to everyone else.
Pm: ... no your not seeing the big picture, i'll run the idea up the ladder.
**It was approved up the ladder, and subsequently cancelled when they realised the scale of the work involved which is both a "thank god" and a "wtf" moment**7 -
(sensitive parts censored)
Friend: Hey, can you hack my (some website) account?
Me: Depends... What's your username?
Friend: (tells username)
Me: (clicks forgot password?)
Friend: I will give $10 if you do it. There is 2 factor authentication enabled.
Me: (silence) Ok.
Website: Please type the class number you were in in 4th grade.
Me: Hey, did you graduated BLAH elementary school?
Friend: Yeah.
Me: Ahh, I remember. You moved to BLAH elementary school in what grade?
Friend: 4
Me: Hmmm, I don't remember seeing you. What class were you in?
Friend: 5
Me: Well, I now remember. Stupid me. (smirks)
Friend: Haha. (continues to play games beside me)
Me: (Types in 8)
Website: We sent you a password to blah@example.com
Me: (uhh, heads to example.com and clicks forget password?)
Email: Please type the class number you were in in 4th grade.
Me: (wtf is this, types 8)
Email: Please type the teacher's name when you were in in 4th grade.
Me: What was the teacher's name?
Friend: Huh?
Me: When you were in 4th grade.
Friend: Ahh! John Smith.
Me: Ahh, he was strict, right?
Friend: Yeah (continues to play games again)
Me: (Types in John Smith)
Email: Set a new password.
Me: (Types "youaresostupid")
Email: Done!
Me: (copies PLAIN TEXT password from email, logs in to website)
Me: Da-da!
Friend: (gasps)
Me: Money plz~
Friend: Nope.
Me: (wtf, then remembers i changed his email password) Fine then.
=====================
1. There is 2 factor authentication enabled. : Got it?
2. The website sent plaintext password.
3. He is just pure idiot.
4. I didn't got the money.
5. I am now a h4x0r11 -
My mom got audited for storing sensitive client information in her gmail account without using a vpn or any other real security.
I had been telling her this was an issue for literally the last three years and shes brushed me off every time.
I got yelled at for not telling her I was serious.35 -
A couple of years ago, I was working in a computer shop as a "technician", I was 15, first job I ever had.
One day an elderly lady came into the shop, probably 50'ish, she and her whole family "suffered" from electromagnetic radiation, and the mother had the worst suffering. She complained about her TV box that just had died.
I accept the tuner and see it's wrapped with 10 layers of aluminium foil, with a tiny hole for the IR receiver.
The whole box smells like burnt electronics, and the foil gets darker for each layer I unwrap. I try explain to her that the box gets warm and overheated by wrapping it like this, and she's lucky that it didn't catch fire.
I further explain to her that she will not get a new box, because the warranty does not cover _this_. The mother tells me she has to wrap it like this, because she gets headaches when she's watching the news.
She then proceeds to go into a rage mode and gets her whole family into the shop, where all of them starts yelling at me, the younger kids start throwing stuff down from the shelves and touching the TVs with sticky fingers (literally, sticky, like yuck!).
Unsure what to do, boss is in a meeting, and my colleague is busy in the back.
So I calmly tell them that in this building there's 4 wireless networks, 3 wireless phones, high voltage cables run in the wall behind me, there's factory tracks 20 meters behind the building, next door business is an electrician, you're standing in front of wall with 30-40 TVs, 5 HDMI splitters, 3 TV boxes and a Blu-ray player. And they've all been standing in front of them for the last 10 minutes.
They all suddenly feel really sick and run out of the store, never to be seen again. From that day, I decided I'll never work in a shop again, and pursued my dreams to become a developer.
TL;DR: Family is "sensitive" to electromagnetic radiation, almost put burnt down their house because of stupidity, yelled at me. I decided to pursue my dream as a developer.16 -
My mentor/guider at my last internship.
He was great at guiding, only 1-2 years older than me, brought criticism in a constructive way (only had a very tiny thing once in half a year though) and although they were forced to use windows in a few production environments, when it came to handling very sensitive data and they asked me for an opinion before him and I answered that closed source software wasn't a good idea and they'd all go against me, this guy quit his nice-guy mode and went straight to dead-serious backing me up.
I remember a specific occurrence:
Programmers in room (under him technically): so linuxxx, why not just use windows servers for this data storage?
Me: because it's closed source, you know why I'd say that that's bad for handling sensitive data
Programmers: oh come on not that again...
Me: no but really look at it from my si.....
Programmers: no stop it. You're only an intern, don't act like you know a lot about thi....
Mentor: no you shut the fuck up. We. Are. Not. Using. Proprietary. Bullshit. For. Storing. Sensitive. Data.
Linuxxx seems to know a lot more about security and privacy than you guys so you fucking listen to what he has to say.
Windows is out of the fucking question here, am I clear?
Yeah that felt awesome.
Also that time when a mysql db in prod went bad and they didn't really know what to do. Didn't have much experience but knew how to run a repair.
He called me in and asked me to have a look.
Me: *fixed it in a few minutes* so how many visitors does this thing get, few hundred a day?
Him: few million.
Me: 😵 I'm only an intern! Why did you let me access this?!
Him: because you're the one with the most Linux knowledge here and I trust you to fix it or give a shout when you simply can't.
Lastly he asked me to help out with iptables rules. I wasn't of much help but it was fun to sit there debugging iptables shit with two seniors 😊
He always gave good feedback, knew my qualities and put them to good use and kept my motivation high.
Awesome guy!4 -
Story time:
I was once working on a project that dealt with incredibly sensitive financial data.
We needed a client’s database to do a migration.
They wouldn’t send it over the internet because it was too big and they didn’t think it would be secure.
They opt to send it in the post on an encrypted usb drive.
(Fair enough thinks I)
USB drive arrives.
Is indeed encrypted.
MFW there’s a post it note in the envelope with the password on.
MFW this is a billion dollar multinational petrochem company.
MFW this same company’s ‘sysadmin’ and ‘dba’ once complained because a SQL script I sent them didn’t work - they’d pasted it twice and couldn’t work this out from the fucking “table already created” error message management studio was throwing at them.3 -
Our current designer is convinced that 00FF44 bright green fits well with the rest of our soft purple/blue color scheme.
I am not a designer, but have worked in a color laboratory, so I've tried time and time again to explain CIE LAB color space, and how at least HCL is a good way to pick & group colors into palettes by using 2-3 luminances for equidistant hues while keeping chroma constant.
I've tried to tell him that the bright green almost physically makes my eyes bleed, because humans are quite sensitive to greens.
He just keeps using the phrase "but it makes the buttons pop nicely".
I just want to pop his skull open with my keyboard. 😫12 -
Dear Microsoft,
Thanks for not completely fucking up Github. At least you didn't integrate Office365, allow only Azure deployments, or force downloading repos through OneDrive or something.
But like most developers, I don't deal well with changes to familiar interfaces.
So please.... STOP FUCKING TWEAKING THE BUTTON PLACEMENTS AND TEXTS ALL OVER THE WEBSITE.
(or at least send me a bottle of cognac and a box of chocolates before every UI experiment, so I can deal with it emotionally. I'm a very sensitive boy, you know).23 -
Fuck open office spaces.
A few months ago I landed a super sweet job as a senior full stack developer, mainly going to work with their Python microarchitecture. The company pays well, has a sweet balance between freedom and responsibility, 30 days vacation etc.
During the recruiting process they walked me around the office that was super cozy with 14 devs in on large room and 10 people from marketing in another. They also mentioned that they would move and merge office with operations and customer service (around 100 more people) in a few months.
Life was good in the old office, I thought that this is the company where I will work for a looooong time.
Now we are in the new office and its fucking shit. No walls or FUCKING CEILINGS between departments. Right above my head there is balcony with customer service talking loud as fuck 24/7. Everyone that is not a developer is just so fucking loud.
I have to use earplugs AND earmuffs to get silence, or blast my ears with way to loud music. Every day around lunch I'm completely done mentally.
I know I'm extra sensitive to noise because of my ADHD, but seriously who the fuck thought this was a good idea?
All the devs have told our boss what needs to be done. If they listen i don't know. In the meantime I will start looking for a new job....18 -
My biggest dev blunder. I haven't told a single soul about this, until now.
👻👻👻👻👻👻
So, I was working as a full stack dev at a small consulting company. By this time I had about 3 years of experience and started to get pretty comfortable with my tools and the systems I worked with.
I was the person in charge of a system dealing with interactions between people in different roles. Some of this data could be sensitive in nature and users had a legal right to have data permanently removed from our system. In this case it meant remoting into the production database server and manually issuing DELETE statements against the db. Ugh.
As soon as my brain finishes processing the request to venture into that binary minefield and perform rocket surgery on that cursed database my sympathetic nervous system goes into high alert, palms sweaty. Mom's spaghetti.
Alright. Let's do this the safe way. I write the statements needed and do a test run on my machine. Works like a charm 😎
Time to get this over with. I remote into the server. I paste the code into Microsoft SQL Server Management Studio. I read through the code again and again and again. It's solid. I hit run.
....
Wait. I ran it?
....
With the IDs from my local run?
...
I stare at the confirmation message: "Nice job dude, you just deleted some stuff. Cool. See ya. - Your old pal SQL Server".
What did I just delete? What ramifications will this have? Am I sweating? My life is over. Fuck! Think, think, think.
You're a professional. Handle it like one, goddammit.
I think about doing a rollback but the server dudes are even more incompetent than me and we'd lose all the transactions that occurred after my little slip. No, that won't fly.
I do the only sensible thing: I run the statements again with the correct IDs, disconnect my remote session, and BOTTLE THAT SHIT UP FOREVER.
I tell no one. The next few days I await some kind of bug report or maybe a SWAT team. Days pass. Nothing. My anxiety slowly dissipates. That fateful day fades into oblivion and I feel confident my secret will die with me. Cool ¯\_(ツ)_/¯12 -
At my previous job we had the rule to lock your PC when you leave. Makes sense of course.
We were not programmers but application engineers, still, we worked with sensitive data.
One colleague always claimed to be the most intelligent and always demanded the "senior" - title. Which he obviously did not deserve.
multiple times a day forgot to lock his workstation and we had to do it for him.
My last week working there, I've had it. He forgot it again... So I made a screenshot of his current environment. Closed everything. Set his new background with the screen shot and killed explorer (windows). Then finally I locked his PC.
When he came back he panicked that his PC froze. He couldn't do shit anymore. Not knowing what to do... 😂
Which makes him a senior of course.
But seriously, first thing I would do is open the task manager and notice that explorer wasn't running... Thus my background with the taskbar isn't real.... My colleagues must be pranking me!
Nope... The "senior" knew little10 -
Story time.
Not sure it counts as data loss, more temporary corruption (and in my own brain).
> be me.
> be clinically depressed
> be recently out of an awful breakup
> recently nearly committed suicide by train
> be bored and lonely one night
> take lsd
> feel fine
> go to McDonald’s
> feel fine
> while eating question the nature of reality
> become convinced I’m an observer of a cosmic story and cannot die
> go outside in only jeans
> run in traffic at 1AM to prove my point
> don’t die
> run around the streets more sure of my new reality than I’d ever been of anything
> feel free and no longer sad
> walk around observing the world
> sit on wall and wonder why the story had the structure I was observing
> fall off wall into grass and mud
> follow cute guy into apartment building
> follow into lift
> ask what everything means
> spend better part of couple hours in lift pressing emergency button asking for help
> get no response
> scare poor Russian lady that gets into lift and finds an overweight topless man on the floor babbling incoherently
> ride to top floor
> get out
> sit on leather chair in corridor
> feelsnice.tiff
> decide I’m actualising my desires and reality
> don’t realise this is just the trip wearing off and consciousness exerting more control
> walk into random apartment (door is unlocked because why wouldn’t it be for the god that I believe I am at this point)
> explore
> gorgeous apartment
> realise it’s a family apartment from clothes in hallway and items
> find bathroom
> decide I want a bubble bath
> run bubble bath
> can’t work out how to drain water. Bath now full of twigs and mud #sorry
> decide that I’d like to go home, or onto my next adventure. Hopefully the seaside as I’m now realising I have more control.
> open bathroom door
> not the seaside. Ah well. Try to walk home
> walk home wrapped in fluffy towel from nice family’s apartment
> get home
> realise what had happened
> throw remaining drugs away
> sit and rock in utter paranoia and guilt for hours until flatmate wakes up.
MFW first bad trip ever.
MFW I wonder whether that family knew I was there and were scared / discovered the mess in the bathroom the next morning and not knowing which is worse.
MFW I still have the towel because it’s fluffy AF.
The moral of the story kids, is that when it comes to the OS rattling around in your brain, installing a virus that is sensitive to what apps you have running is a bad idea when those apps make the virus go to fucking town.
Terrible analogy I know, but fuck it.29 -
Motherfucker. It's two thousand fucking seventeen. You can get a free ssl certificate for any website.
Then WHY are there still some fucking websites which contain login portals, sensitive information or anything that SHOULD be protected in transit WITHOUT FUCKING SSL?!
I hope that the people who manage those sites and are AWARE that they can get a free cert but don't do that die in agonising pain.
This really fucking pisses me off.
On another note, EVERY site should have SSL, it's free anyways and protects your visitors from a range of threats.-24 -
Not so much screaming as staring in disbelief, mumbling profanity in his direction...
When my department lead said "I don't think this unit testing hype or code reviews make much sense, it's more efficient to just make a checklist and test the application yourself"
This was the QA department of an aerospace company, we wrote NDT software to do image recognition on xrays of alloy welds and micrometer laser measurements on fuel tank surfaces. Software which is quite mission critical, a single misrecognized welding fault could literally cost up to half a billion dollars — not to mention that it's a very sabotage & espionage sensitive industry.
After raising some hell he was replaced though.3 -
Before anyone starts going batshit crazy, this is NOT a windows hate post. Just a funny experience imo.
So I was tasked with installing ProxMox on a dedicated server at my last internship. The windows admin was my guider (he could also do debian). (he was a really nice/chill guy)
So we were discussing what VM's we wanted and the boss (really cool dude by the way) said he wanted a VPS for storing some company stuff as well. Fair enough, what would we use? I suggested debian and centos. Then we started discussing what we'd do if the systems would fuck up etc (at installation or whatever).
So I didn't wanna look like a Linux Nazi so I suggested windows. Then the happy/positive guider/windows admin suddenly became dead serious (I was actually like 'woah' for a second) and said this:
No. We're not going to fucking use windows for this. For general servers etc sometimes, fair enough but we're talking about sensitive company data here. I don't want that data to be stored on a proprietary/closed source system, hell what if there's some kinda fucking backdoor build in, who can fucking verify that? We're using Linux, end of discussion.
😓
I was pretty flabbergasted as he's a nice guy and actually really likes windows!
Linux it became.5 -
SO GUESS WHAT
IF YOUR SHITTY WIFI CRAPS OUT DURING A VISUAL STUDIO UPDATE, VISUAL STUDIO FUCKING COMMITS SUICIDE
MICROSOFT CAN SUCK A BIG, VEINY COCK. IM SO DONE WITH THEIR SENSITIVE, CONVOLUTED, SLOW IDE.21 -
Humans!
The amount of sensitive, private, and secure information you can get just by asking someone for it is truly astounding.5 -
"We don't need to invest in security - noone is going to hack us anyway" == "We don't need a fire department in our city - fire is not going to start here anyway"
We don't need to invest in security - everything is public anyway" == "We don't need a fire department in our city - our buildings are made out of straws anyway"
-- my thoughts after seing a line in client's spec: "sensitive data is transferred via a secure tcp channel (https) and all the public data is transferred via an unencrypted tcp (http) channel"3 -
Sometimes I wish I was allowed to just strangle my colleagues...
Example from the 'code base':
try:
do_something()
except Exception as e:
log(e)
do_something()
When I asked why they would redo the same call right after it failed I was told that 'It works the second time because it takes time to raise the Exception '.
Bitch, you've got a race condition in your sensitive banking software. You know it's there. Do you really want to trust the time needed to raise your exception will always be enough to synch that dumpster fire you call code?
Show some fucking respect for your craft and fix that shit. But of course they won't, because it will work flawlessly until it suddenly stops working. Taking down who knows what in this damn, undocumenred monolith with it....
Sometimes I'm honestly afraid to trust banks with my money.7 -
Devs: We need access to PROD DB in order to provide support you're asking us for.
Mgmt: No, we cannot trust you with PROD DB accesses. That DB contains live data and is too sensitive for you to fuck things up
Mgmt: We'll only grant PROD DB access to DBAs and app support guys
Mgmt: <hire newbies to app support>
App_supp: `update USER set invoice_directory = 54376; commit;`
----------------
I have nothing left to say....7 -
I remember that time my class (first year of software development) wrote a huge project for a real company as practice for irl stuff.
I was the only Linux user and it would be deployed on a Linux server.
Spent 10 weeks of development and then the moment of deployment on a Linux server began!
.
.
.
.
.
Nothing was case sensitive, everything was programmed for a windows architecture (backward slashes etc) and mssql was used while we would host it on a MySQL server.
The tree core guys spent three days or so to make the entire fucker compatible 😂
It was enjoyable to see them (literally) sweat 😊 (it had been known from the very beginning)7 -
Had a follow up meeting today to resolve the issue of Product ignoring our comments about possible issues, better ways to do it etc.
New rules:
- We are allowed to suggest to Product that they might be doing something wrong
- We are not allowed to tell product they are doing something wrong
- If Product don’t listen, that’s fine, we will document our comments to protect us later.
Conclusion:
Product are too sensitive to have a conversation with. We are now going to let them fuck everything up, make some notes and say “I told you so” at a later date.
Maturity at its finest ladies and gentlemen.5 -
Root rents an office.
Among very few other things, the company I'm renting an office from (Regus) provides wifi, but it isn't even bloody secured. There's a captive portal with a lovely (not.) privacy policy saying they're free to monitor your traffic, but they didn't even bother using WEP, which ofc means everyone else out to the fucking parking lot four floors down can monitor my traffic, too.
Good thing I don't work for a company that handles sensitive data! /s But at least I don't have access to it, or any creds that matter.
So, I've been running my phone's connection through a tor vpn and sharing that with my lappy. It works, provides a little bit of security, but it's slow as crap. GET YOUR SHIT TOGETHER, REGUS.
AND WHILE YOU'RE AT IT, CLEAN THE SHIT OUT OF THE FUCKING BATHROOM FFS.
Ugh. $12/day to work in a freaking wind tunnel (thanks, a/c; you're loud as fuck and barely work), hear other people's phone conversations through two freaking walls, pee in a bathroom that perpetually smells like diarrhea, and allow anyone and everyone within a 50+ meter radius to listen to everything my computer says.
Oh, they also 'forgot' to furnish my office, like they promised. Three freaking times. At least I have a table and chair. 🙄
Desk? What desk?
Fucking hell.20 -
Worst legacy experience...
Called in by a client who had had a pen test on their website and it showed up many, many security holes. I was tasked with coming in and implementing the required fixes.
Site turned out to be Classic ASP built on an MS Access database. Due to the nature of the client, everything had to be done on their premises (kind of ironic but there you go). So I'm on-site trying to get access to code and server. My contact was *never* at her desk to approve anything. IT staff "worked" 11am to 3pm on a long day. The code itself was shite beyond belief.
The site was full of forms with no input validation, origin validation and no SQL injection checks. Sensitive data stored in plain text in cookies. Technical errors displayed on certain pages revealing site structure and even DB table names. Server configured to allow directory listing in file stores so that the public could see/access whatever they liked without any permission or authentication checks. I swear this was written by the child of some staff member. No company would have had the balls to charge for this.
Took me about 8 weeks to make and deploy the changes to client's satisfaction. Could have done it in 2 with some support from the actual people I was suppose to be helping!! But it was their money (well, my money as they were government funded!).1 -
My first testing job in the industry. Quite the rollercoaster.
I had found this neat little online service with a community. I signed up an account and participated. I sent in a lot of bug reports. One of the community supervisors sent me a message that most things in FogBugz had my username all over it.
After a year, I got cocky and decided to try SQL injection. In a production environment. What can I say. I was young, not bright, and overly curious. Never malicious, never damaged data or exposed sensitive data or bork services.
I reported it.
Not long after, I got phone calls. I was pretty sure I was getting charged with something.
I was offered a job.
Three months into the job, they asked if I wanted to do Python and work with the automators. I said I don't know what that is but sure.
They hired me a private instructor for a week to learn the basics, then flew me to the other side of the world for two weeks to work directly with the automation team to learn how they do it.
It was a pretty exciting era in my life and my dream job.4 -
This is the GREAT ROLLING website that I ranted recently. I couldn't share more than this as other parts of the page contains sensitive information that is not out in the internet yet. The whole friggin page is like this. EVERYTHING ROLLS
 25
25 -
It's not that I hate PHP, I just hate the lack of consistency in standard function naming and parameter order, nonsensical attribute access, nearly-meaningless comparison operators, reference handling, case (in)sensitivities, and more!
I mean, look at these functions:
strtoupper(...)
bin2hex(...)
strtolower(...)
And look at THESE FUNCTIONS:
array_search($needle, $haystack)
strpos($haystack, $needle)
array_filter($array, $callable)
array_map($callback, $array)
array_walk($array, $callable)
And let me jUST USE SOME ATTRIBUTES:
$object->attr = "No dollar sign...";
Class::$attr = "GOD WHY";
HOW ABOUT SOME COMPARISONS:
(NULL == 0) // true
(NULL < -1) // ALSO true
Functions AREN'T CASE SENSITIVE (at least variables are).
Wanna dereference? TOO BAD, YOU'LL HAVE TO GET OUT THE TNT.
Alright, yeah, I hate PHP.19 -
Following a conversation with a fellow devRanter this came to my mind ago, happened a year or two ago I think.
Was searching for an online note taking app which also provided open source end to end encryption.
After searching for a while I found something that looked alright (do not remember the URL/site too badly). They used pretty good open source JS crypto libraries so it seemed very good!
Then I noticed that the site itself did NOT ran SSL (putting the https:// in front of the site name resulted in site not found or something similar).
Went to the Q/A section because that's really weird.
Saw the answer to that question:
"Since the notes are end to end encrypted client side anyways, we don't see the point in adding SSL. It's secure enough this way".
😵
I emailed them right away explaing that any party inbetween their server(s) and the browser could do anything with the request (includingt the cryptographic JS code) so they should start going onto SSL very very fast.
Too badly I never received a reply.
People, if you ever work with client side crypto, ALWAYS use SSL. Also with valid certs!
The NSA for example has this thing known as the 'Quantum Insert' attack which they can deploy worldwide which basically is an attack where they detect requests being made to servers and reply quickly with their own version of that code which is very probably backdoored.
This attack cannot be performed if you use SSL! (of course only if they don't have your private keys but lets assume that for now)
Luckily Fox-IT (formerly Dutch cyber security company) wrote a Snort (Intrustion Detection System) module for detecting this attack.
Anyways, Always use SSL if you do anything at all with crypto/sensitive data! Actually, always use it but at the very LEAST really do it when you process the mentioned above!31 -
HR: Hey you really need to be more sensitive with what you say
Dev: What makes you bring this up?
HR: Well we had a concerned employee overhear you telling one of the interns that the Russian word for “approved” is “blyat”.
Dev: Ah.20 -
Me: "Ugh. Soo insensitive.." *angry muttering*
Curious cousin: "Whom? What? Why?"
Me: "My stupid Mac is not case sensitive so I have to mount a Unix partition and reference it from somewhere else. Why wouldn't they just make a case sensitive filesystem like a proper Unix based OS?"
Clearly uninterested cousin: "seriously?! You called your laptop insensitive? I thought you were talking about a guy" ..
Filthy casuals.6 -
Woohoo! 32k achieved!!! Finally I can post some new rant without risking some sudden overshoot 😁
So putting celebrations aside for a minute, a while ago I've noticed a tingle when I stroke my finger across metal areas of my tablet, or the sides of my phone (which probably has metal near it too) while it's charging. And it's been bugging me ever since.
Now, some things to note are that it only happens when my feet are touching the ground though slippers, and that the frequency is so low that I can actually feel the tingle when I slide my finger across the material. This to me at least seems like electricity flows through me into ground, and touching the ground directly provides a path so easy for the electrons to run away that I don't feel it at all. But if I lift my feet off the ground entirely, I just get charged up and after that, nothing else happens.
So those are my ideas. The answers on the subject on the other hand.. absolute cancer. Unsurprisingly, most of them came from Apple users. Here's some of them.
https://discussions.apple.com/threa...
- I've not noticed it, but if you're concerned bring the phone to Apple for evaluation.
- Me too facing same problem.. did u visit apple care?
And one good answer at least...
- google emf sensitivity, its real. You are right, there is a small current flowing through your body, try to limit your usage. The problem with this issue is those who aren't affected (lucky ones for now) will tell you these products are 100% safe. To a degree they are, i used my ipod touch for about 2 years straight vwith virtually no symptoms. then the tingling started and it gets worse.You will get more sensitive to progressively less powerful things. I dont want to scare you but just limit your usage like i didnt do 🙂
Overall that discussion was pretty good actually, aside from "bring it to the Genius Bar, they'll know for sure and not just sell you another unit". But then there's Reddit.
https://reddit.com/r/iphone/...
- Ok, real reason is probably that the extension cord and/or outlet is probably not grounded correctly. Either that or you are using a cheap knockoff charger.
Either use a surge protector and/or use the authentic Apple Charger.
- It's not the volts that hurt you, it's the amps
- I think you are in deep love with your phone. That tingling sensation is usually referred to as "love" in human language.
- Do less acid, I would advise.
Okay, so that's the real cancer. Grounding issue sounds reasonable despite it being wrong. Grounding is actually not needed when your charging appliance doesn't have any exposed metal parts. And isolation from high voltage to low voltage side actually happens through things like routering holes into the PCB, creating spark gaps, and using galvanic isolation through things like optocouplers. As for a surge protector? I'm using them to protect my PC and my servers, but the only purpose they serve is to protect from.. you guessed it.. voltage surges, like lightning bolts hitting the grid. They don't do shit for grounding or reducing this tingle! What a fucking tool.
It's not the volts that kill, it's the amps.. yeah I'm sure that the debunking of that is easy to find. Not gonna explain that here. And the rest of it.. yeah it's just fucking cancer.
Now what's the real issue with this tingle? It's actually a Class-Y rated (i.e. kV rated) capacitor that's on the transformer of any switch-mode power supply, including phone chargers. If memory serves me right, it helps with decoupling the switching noise and so on. But as it's connected to the primary side of the transformer, if the cap is sufficiently large and you are sufficiently sensitive, it can actually cause that tingle by passing a fraction of the mains electricity into your body. It's totally safe though, as the power that these caps pass is very small. But to some, it's noticeable.
Hope you found this interesting! And thanks a lot for bringing me to 2^15. I really appreciate it ♥️ 15
15 -
The gift that keeps on giving... the Custom CMS Of Doom™
I've finally seen enough evidence why PHP has such a bad reputation to the point where even recruiters recommended me to remove my years of PHP experience from the CV.
The completely custom CMS written by company <redacted>'s CEO and his slaves features the following:
- Open for SQL injection attacks
- Remote shell command execution through URL query params
- Page-specific strings in most core PHP files
- Constructors containing hundreds of lines of code (mostly used to initialize the hundreds of properties
- Class methods containing more than 1000 lines of code
- Completely free of namespaces or package managers (uber elite programmers use only the root namespace)
- Random includes in any place imaginable
- Methods containing 1 line: the include of the file which contains the method body
- SQL queries in literally every source file
- The entrypoint script is in the webroot folder where all the code resides
- Access to sensitive folders is "restricted" by robots.txt 🤣🤣🤣🤣
- The CMS has its own crawler which runs by CRONjob and requests ALL HTML links (yes, full content, including videos!) to fill a database of keywords (I found out because the server traffic was >500 GB/month for this small website)
- Hundreds of config settings are literally defined by "define(...)"
- LESS is transpiled into CSS by PHP on requests
- .......
I could go on, but yes, I've seen it all now.12 -
Just wow. I am amazed by what just happened.
A year ago my parents decided to switch from desktop to laptop for convenience. Knowing their needs, i bought them one without an OS and installed Ubuntu 16.04 on it. The thing is that if you do a regular maintenance of the laptop once a year at their partner company, you get additional 4 years of warranty (this offer is amazing).
So today was the day I brought the laptop for this maintenance for the first time. They make you a profile on their support website where you can track shit regarding your device, super convenient. First thing I notice that the login page was not https. Awkward, but there is no sensitive data here so i let it pass. Naturally i forgot my password, so I requested a new one and guess what? I recieved it in plaintext via mail. A tech repair oriented company does this, my god.
I went there, gave them the laptop in question and got a piece of paper, where they wrote that the laptop is in their hands now, and the current physical state of the laptop, and blabla.
I got home and I read what the guy wrote among other things: THE OPERATING SYSTEM IS NOT LEGAL.
How the fuck is Ubuntu not legal??? What the fuck is this shit? I sure as hell didn't torrent it or bought a booteged copy on the streets.11 -
!dev
Me *downloading some weird linux distro to test in VirtualBox - I only do this once a month for like 1 hour*
my brother: Oh my god! Are you downloading something again? Moooom he is downloading something non-stop
every day:
my brother *watching some series/YouTube videos/playing ping-sensitive multiplayer games - all the fucking time, everything he does all day is this + eating and sleeping*
me *retrying multiple times to load anything, including devRant* 😒😠9 -
Had a discussion with a developer about security. His software transfers all user data (password and files) unencrypted, so anyone can grab them with wireshark. I told him that this is a severe issue. He said no its no problem because if you get hacked its your own fault, because you probably used an insecure network. NO ! YOU FUCKING MALADJUSTED SHEEP-MOLESTING OBJECT OF EXECRATION, YOU SHOULD ALWAYS ENCRYPT SENSITIVE USERDATA NO MATTER WHAT NETWORK YOU USE. FUCKING KILL ME ALREADY.
Not implementing encryption is one thing but then acting like its no problem is a fucking nother one. Why do people not understand that security of userdata is important???11 -
5 years ago, in my first week of starting this particular job, the CTO casually mentioned they'd been struggling with a bug for years. Basically, in the last few days of the year, it seemed that records were jumping a year ahead, with no rhyme nor reason why. Happened every year, and wasn't linked with them deploying new code. (Their code was a mess with no sane way to unit test it, but that was a separate issue.)
I happened to know immediately what might be causing it - so I ran a case-sensitive search in the codebase for "YYYY", pointed out the issue, explained it, then committed a fix all in about 2 minutes.
I was told I'd officially passed my probation.
(Search for "week year vs year" if you're curious & the above doesn't ring any bells.)6 -
So... an Italian government website published sensitive data of thousand of citizens, because they thought that it was enough to turn white the text color in order to anonymize the sensitive content of the files. Italy, 2019.
Source (in Italian):
https://wired.it/internet/regole/...7 -
Christmas lights were blinking randomly IN SECTIONS without any sort of "control brick", just with a plain wall plug and TWO wires coming out of it.
In this house we obey the laws of physics, I immediately called magic on this and started digging. I found out that was like five chains of lights wired in parallel, and every chain contained one special lamp that had a thin plate of some thermal-sensitive material inside. It heats up which makes it go straight, thus breaking its chain until it cools down enough to curl again and make the contacts touch.
Brilliant and really cheap way of making randomly blinking Christmas lights without any kind of controller, with just two wires and some physics. That's what I call "nocode". 11
11 -
I was told that I am too sensitive and afterwards a liability because I couldn’t concentrate in a working space where interns were constantly screaming, running around, hitting and farting each other, throwing shit around and playing games (instead of working)...
I was told by the HR person that “boys will be boys”...10 -
A Month ago...
Me: when are you going to complete the report
Friend: we can do it in minutes
Me: you can't Ctrl + c and Ctrl +v as there is plagiarism check
Friend: we have spin bot
Me: you do that now itself . if something happens? You can join me .
Friend: just chill
Now ...
Me: done with report
Friend: feeding it to spin bot!
Feeds text related to database security....
Spin bot:
Garbage collector == city worker
SQL statements == SQL explanation
SQL queries == SQL interrogation
SQL injection == SQL infusion
Attack == assault
Malicious == noxious
Data integrity == information uprightness
Sensitive == touchy
.....
Me: told you so...
**spin not == article rewriter3 -
So Tesla employees with access to recordings from customer vehicles have been sharing clips internally whenever something "funny" happened. Including nudity, intimacy, stuff inside garages, and crashes. And some even got promoted for doing this.
If there are any Tesla owners here, grab you cock and start waving at your car so they have to watch it. Or if you don't have a cock, borrow your neighbour's one.
Makes you wonder if other companies handling customer footage for labeling or otherwise are much or any better.
https://reuters.com/technology/...30 -
The frequency in which I see women-hating comments in certain tech FB groups is alarmingly high lately. Even posts about ordering food are somehow twisted into really awful discussions (raping women, locking them at home, stoning cheating wives...).
Maybe I'm just a sensitive "female", but I honestly wouldn't want to work with a person who has this mindset.59 -
I found this on Quora and It's awesome.
Have I have fallen in love with Python because she is beautiful?
Answer
Vaibhav Mallya, Proud Parseltongue. Passionate about the language, fairly experienced (since ...
Written Nov 23, 2010 · Upvoted by Timothy Johnson, PhD student, Computer Science
There's nothing wrong with falling in love with a programming language for her looks. I mean, let's face it - Python does have a rockin' body of modules, and a damn good set of utilities and interpreters on various platforms. Her whitespace-sensitive syntax is easy on the eyes, and it's a beautiful sight to wake up to in the morning after a long night of debugging. The way she sways those releases on a consistent cycle - she knows how to treat you right, you know?
But let's face it - a lot of other languages see the attention she's getting, and they get jealous. Really jealous. They try and make her feel bad by pointing out the GIL, and they try and convince her that she's not "good enough" for parallel programming or enterprise-level applications. They say that her lack of static typing gives her programmers headaches, and that as an interpreted language, she's not fast enough for performance-critical applications.
She hears what those other, older languages like Java and C++ say, and she thinks she's not stable or mature enough. She hears what those shallow, beauty-obsessed languages like Ruby say, and she thinks she's not pretty enough. But she's trying really hard, you know? She hits the gym every day, trying to come up with new and better ways of JIT'ing and optimizing. She's experimenting with new platforms and compilation techniques all the time. She wants you to love her more, because she cares.
But then you hear about how bad she feels, and how hard she's trying, and you just look into her eyes, sighing. You take Python out for a walk - holding her hand - and tell her that she's the most beautiful language in the world, but that's not the only reason you love her.
You tell her she was raised right - Guido gave her core functionality and a deep philosophy she's never forgotten. You tell her you appreciate her consistent releases and her detailed and descriptive documentation. You tell her that she has a great set of friends who are supportive and understanding - friends like Google, Quora, and Facebook. And finally, with tears in your eyes, you tell her that with her broad community support, ease of development, and well-supported frameworks, you know she's a language you want to be with for a long, long time.
After saying all this, you look around and notice that the two of you are alone. Letting go of Python's hand, you start to get down on one knee. Her eyes get wide as you try and say the words - but she just puts her finger on your lips and whispers, "Yes".
The moon is bright. You know things are going to be okay now.
https://quora.com/Have-I-have-falle...#4 -
TL;DR
A "friend" is a tech fraud. Faking his resume as a software engineer! Only interested on the salary. This is unfair to all of us putting the hours of effort/practice just to improve our craft! 😠😤
I have a "friend" who is faking his resume, putting fake experiences and putting jargons not even related to tech just to make himself smart. He's using his customer service rep experience to talk confidently. His resume fcking long, 3 pages of fakery. I can't help, but to laugh when he sent it to me.
He has a tech degree, but worked in a BPO industry for 4 years, then recently, he quit. He got jealous with the lucrative software development industry and he wants to relearn coding, as a friend and I like sharing my knowledge, I agreed to guide him in the process.
After 3 moths, he got his first job, but unfortunately he got fired after two weeks because he commited sensitive data to the remote repo.
Then after a month, he got his second job and worked there for 6 months, he still don't know what his doing and always ask me solutions when he is stuck.
He got his 3rd job, remote work with high compensation. Fast forward after 3 months, he only got 1 month of salary, the other 2 wasn't given for unknown reason, my best guess is the company noticed his experience on paper does not match on real life.
Currently, he's working on another remote work with same compensation as before, and he still asks me super simple questions from time to time.
This is so unfair to all the devs who truly deserves the opportunity.20 -
!rant
Our lead dev in the company seems to be a smart guy who's sensitive about code quality and best practices. The current project I'm working on (I'm an intern) has really bad code quality but it's too big an application with a very important client so there's no scope of completely changing it. Today, he asked me to optimize some parts of the code and I happily sat down to do it. After a few hours of searching, profiling and debugging, I asked him about a particular recurring database query that seemed to be uneccesarilly strewn across the code.
Me: "I think it's copy pasted code from somewhere else. It's not very well done".
Lead Dev: "Yeah, the code may not the be really beautiful. It was done hurriedly by this certain inexperienced intern we had a few years back".
Me: "Oh, haha. That's bad".
Lead Dev: "Yeah, you know him. Have you heard of this guy called *mentions his own name with a grin*?"
Me: ...
Lead Dev: "Yeah, I didn't know much then. The code's bad. Optimize it however you like. Just test it properly"
Me: respect++;2 -
The deeper I go down the infosec rabbit hole, the more I worry about my doctors still using Windows XP. Why would you save sensitive patient info in those....shoe boxes?
 4
4 -
I've found and fixed any kind of "bad bug" I can think of over my career from allowing negative financial transfers to weird platform specific behaviour, here are a few of the more interesting ones that come to mind...
#1 - Most expensive lesson learned
Almost 10 years ago (while learning to code) I wrote a loyalty card system that ended up going national. Fast forward 2 years and by some miracle the system still worked and had services running on 500+ POS servers in large retail stores uploading thousands of transactions each second - due to this increased traffic to stay ahead of any trouble we decided to add a loadbalancer to our backend.
This was simply a matter of re-assigning the IP and would cause 10-15 minutes of downtime (for the first time ever), we made the switch and everything seemed perfect. Too perfect...
After 10 minutes every phone in the office started going beserk - calls where coming in about store servers irreparably crashing all over the country taking all the tills offline and forcing them to close doors midday. It was bad and we couldn't conceive how it could possibly be us or our software to blame.
Turns out we made the local service write any web service errors to a log file upon failure for debugging purposes before retrying - a perfectly sensible thing to do if I hadn't forgotten to check the size of or clear the log file. In about 15 minutes of downtime each stores error log proceeded to grow and consume every available byte of HD space before crashing windows.
#2 - Hardest to find
This was a true "Nessie" bug.. We had a single codebase powering a few hundred sites. Every now and then at some point the web server would spontaneously die and vommit a bunch of sql statements and sensitive data back to the user causing huge concern but I could never remotely replicate the behaviour - until 4 years later it happened to one of our support staff and I could pull out their network & session info.
Turns out years back when the server was first setup each domain was added as an individual "Site" on IIS but shared the same root directory and hence the same session path. It would have remained unnoticed if we had not grown but as our traffic increased ever so often 2 users of different sites would end up sharing a session id causing the server to promptly implode on itself.
#3 - Most elegant fix
Same bastard IIS server as #2. Codebase was the most unsecure unstable travesty I've ever worked with - sql injection vuns in EVERY URL, sql statements stored in COOKIES... this thing was irreparably fucked up but had to stay online until it could be replaced. Basically every other day it got hit by bots ended up sending bluepill spam or mining shitcoin and I would simply delete the instance and recreate it in a semi un-compromised state which was an acceptable solution for the business for uptime... until we we're DDOS'ed for 5 days straight.
My hands were tied and there was no way to mitigate it except for stopping individual sites as they came under attack and starting them after it subsided... (for some reason they seemed to be targeting by domain instead of ip). After 3 days of doing this manually I was given the go ahead to use any resources necessary to make it stop and especially since it was IIS6 I had no fucking clue where to start.
So I stuck to what I knew and deployed a $5 vm running an Nginx reverse proxy with heavy caching and rate limiting linked to a custom fail2ban plugin in in front of the insecure server. The attacks died instantly, the server sped up 10x and was never compromised by bots again (presumably since they got back a linux user agent). To this day I marvel at this miracle $5 fix.1 -
So my boss booked me a spot at a conference about "the future of online payments" and I received an email with auto created account (there was no sign up) with a clear text password.
I'm feeling pretty confident that I can trust them to guide and advise me on best practices when it comes to handling sensitive information. 8
8 -
I didn't scream.. just told him to jump off of terrace..
What ticked me?! He was a support guy..slowest mofo ever..
I was in the middle of fixing major fuckup on prod, when our VPN to client disconnected. I rushed over to support to ask if it is 'just' an expired session (which he was in charge of renewing but constantly fucked up) or if there is some other problem, so I know how to proceed..do I need to contact our sysadmins, client's support guys etc..
He
started
to
slooooooooowly
explain
I
am
not
the
only
one
with
VPN
problems
...
Was that what I asked you?! // he had an annoying habit of slooooowly talking and explaining unrelated things & personal stuff that bothered him & most of the times he chose the most time sensitive period to drone off..
So I cut him of saying, that others were probably not 'tinkering' with production and that I need this back ASAP, so if he could tell me when the session will be renewed or if there is something else problematic..
He said he will check..I didn't move.. he looked at me insurprise, you want me to check *NOW*?! Yeah, it's urgent.. He proceeded very very veeeery slooooowly, taking the support phone../* he was even eating sandwich during that, so only one hand free, typing one letter at a min */
I was finaly notified that the session expired and that he will fix it soon (meaning in 15-20mins o.O which should not take him more than 5).. and was like 'can I do sth else for you'?! Yeah, do the backflip.. you know the rest..3 -
Old story, and yeah, it's all true, I shit you not!
So here I am at about age 11 (more or less). At the time, I had an almost brand new 333MHz beast, with 8 MB RAM, 2 (!!!) MB video card and (I think) about 300 MB of storage (yeah, I'm old :)) ).
Connected to this monster was sitting a 14" CRT monitor, mechanical keyboard and a 2 button, ball "powered" mouse.
There was no optical tracking tech at the time.
One evening, I notice my mouse starts lagging. Test it to see if Win95 is stuck. Nope, just mouse problems...
Fiddle with it a little, and at some point it stops working at all.
My room was dark now, so I got up to turn on the lights, sat down in front of the PC, and moved the mouse by instinct.
Surprise! It's working again!
My brother comes in and turnes off the lights. Mouse non responsive.
I tell him to turn them on again, mouse works again.
At this point, we were both scratching our heads at this mystery...
I decided to confirm it again using a desc light.
Conclusion: my 2 button, ball tracking, non light sensitive mouse was working only if light was shining directly oh it AND on my 14" crt monitor at the same time!!!
To this day I have no ideea why.
I kept them both for posterity, and they are still there in my parent's attic.
Fin.7 -
Help.
I'm a hardware guy. If I do software, it's bare-metal (almost always). I need to fully understand my build system and tweak it exactly to my needs. I'm the sorta guy that needs memory alignment and bitwise operations on a daily basis. I'm always cautious about processor cycles, memory allocation, and power consumption. I think twice if I really need to use a float there and I consider exactly what cost the abstraction layers I build come at.
I had done some web design and development, but that was back in the day when you knew all the workarounds for IE 5-7 by heart and when people were disappointed there wasn't going to be a XHTML 2.0. I didn't build anything large until recently.
Since that time, a lot has happened. Web development has evolved in a way I didn't really fancy, to say the least. Client-side rendering for everything the server could easily do? Of course. Wasting precious energy on mobile devices because it works well enough? Naturally. Solving the simplest problems with a gigantic mess of dependencies you don't even bother to inspect? Well, how else are you going to handle all your sensitive data?
I was going to compare this to the Arduino culture of using modules you don't understand in code you don't understand. But then again, you don't see consumer products or customer-specific electronics powered by an Arduino (at least not that I'm aware of).
I'm just not fit for that shooting-drills-at-walls methodology for getting holes. I'm not against neither easy nor pretty-to-look-at solutions, but it just comes across as wasteful for me nowadays.
So, after my hiatus from web development, I've now been in a sort of internet platform project for a few months. I'm now directly confronted with all that you guys love and hate, frontend frameworks and Node for the backend and whatever. I deliberately didn't voice my opinion when the stack was chosen, because I didn't want to interfere with the modern ways and instead get some experience out of it (and I am).
And now, I'm slowly starting to feel like it was OKAY to work like this.10 -
PM: Can we have it so the usernames are case-sensitive?
Me: uhh, sure I guess.. But thats like really pointless and adds no real usefulness.. In fact makes the whole logging in thing a tad more complicated for no reason..
PM: Well this one other product we have uses "Admin" for the login versus yours that used "admin" so it needs to be implemented.
(note that mine accepted "Admin" anyways...) *implemented it*
PM: So there's a problem with the username sort, it sorts by capitals then lowercase.. eg:
alpha
beta
Alpha
Me: Yeah, you asked for case-sensitive usernames..
PM: Well can you fix it?
Me: I could create a second field within the user data that is the username in all lowercase and sort by that. But that negates like all of the whole case-sensitive usernames thing.. OR I could drop all this actually important work I'm doing and do a whole bunch of work on a custom sort for this useless fucking feature you wanted me to put in..
*it's been 2 weeks and still no reply...* -
All the cunts with their strong cologne mixed with cigarettes smell should have cut off their noses like Voldemort.7
-
Oh man. Mine are the REASON why people dislike PHP.
Biggest Concern: Intranet application for 3 staff members that allows them to set the admin data for an application that our userbase utilizes. Everything was fucking horrible, 300+ php files of spaghetti that did not escape user input, did not handle proper redirects, bad algo big O shit and then some. My pain point? I was testing some functionality when upon clicking 3 random check boxes you would get an error message that reads something like this "hi <SENSITIVE USERNAME DATA> you are attempting to use <SERVER IP ADDRESS> using <PASSWORD> but something went wrong! Call <OLD DEVELOPER's PHONE NUMBER> to provide him this <ERROR CODE>"
I panicked, closed that shit and rewrote it in an afternoon, that fucking retard had a tendency to use over 400 files of php for the simplest of fucking things.
Another one, that still baffles me and the other dev (an employee that has been there since the dawn of time) we have this massive application that we just can't rewrite due to time constraints. there is one file with (shit you not) a php include function that when you reach the file it is including it is just......a php closing tag. Removing it breaks down the application. This one is over 6000 files (I know) and we cannot understand what in the love of Lerdorf and baby Torvalds is happening.
From a previous job we had this massive in-house Javascript "framework" for ajax shit that for whatever reason unknown to me had a bunch of function and object names prefixed with "hotDog<rest of the function name>", this was used by two applications. One still in classic ASP and the other in php version 4.something
Legacy apps written in Apache Velocity, which in itself is not that bad, but I, even as a PHP developer, do not EVER mix views with logic. I like my shit separated AF thank you very much.
A large mobile application that interfaced with fucking everything via webviews. Shit was absolutley fucking disgusting, and I felt we were cheating our users.
A rails app with 1000 controller methods.
An express app with 1000 router methods with callbacks instead of async await even though async await was already a thing.
ultraFuckingLarge Delphi project with really no consideration for best practices. I, to this day enjoy Object Pascal, but the way in which people do delphi can scare me.
ASP.NET Application in wich there seemed to be a large portion of bolted in self made ioc framework from the lead dev, absolute shitfest, homie refused to use an actual ioc framework for it, they did pay the price after I left.
My own projects when I have to maintain them.9 -
My university has impeccable data management. I needed to ssh into their Linux server for an assignment but it refused to accept my login. Which was weird because I could login to the same account on one of our websites just fine. I typed my password into a text file and then copy and pasted it into both logins. The Linux one failed but the website succeeded. After some experimentation it turns out that the Linux server only recognized my username if I typed it in all lowercase, even though when I created the account it had uppercase characters as well.
So let me walk you through the sloppiness that had to have occurred for this to happen. When I first created the account it must have ignored what I entered and just saved the username in all lowercase without communicating that to me. Then the websites that use this account must either ignore case for usernames or lowercase the user input before querying the database. Finally, the Linux server, despite knowing that all the usernames are lowercase, is case sensitive and won't recognize the username as I originally typed it in.
Can you guess what department manages the account, website and Linux server? The Department of Computer and Information Science. Incredible.2 -
// Rant
I can understand that people accidentally commit something sensitive to GitHub, I did it too once, but ...
WHY THE FUCK DO YOU MAKE YOUR MISTAKE WORSE BY MAKING IT SEARCHABLE VIA THE GLORIOUS COMMIT MESSAGE OF "REMOVING PASSWORD"
... seriously just google "git remove password" and there is a step by step guides on how to remove sensitive data from git.
Reference (320,006 free passwords):
https://github.com/search/...9 -
When I started university, I was getting out of some really awful situations-- emotionally abusive parents, a boyfriend who was blackmailing me, a truly bizarre rape, etc. My life had been a little rough, and I was dealing with some PTSD.
My first computer science course was great. The professor was clear, patient, everything a sensitive student needed. I was able to concentrate on the curriculum without any problems.
The second 'intermediate' course, though? Not so much. The professor shouted his lectures during the entire class period in a relatively small classroom. Occasionally, he would clasp his hands and move around pretty unpredictably (like jumping out at the class), which spooked me a few times. He also always seemed like he was just hovering on the edge of madness, like he was just barely keeping it together, but he never broke.
I sat in the front row and was absolutely terrified during his lectures because it seemed like he was mad at me. I was half expecting him to start attacking me at any moment. Because, you know, PTSD.
I was also only getting a comp sci minor, so the other students looked at me like I wasn't supposed to be there, which also made me feel pretty uncomfortable, but such is life.
After most classes with him, I would need to take about an hour or two afterwards to calm down, stop shaking, and recompose myself. I looked forward to test days because he wouldn't yell. It was rough.
Later on, I learned that he used to be a gym teacher, which explains the jumping and yelling. Also, his wife, daughter, and dog all died within six months of each other the year prior, which might explain why he always seemed so on edge.3 -
Getting ready for GDPR at work. I had to explain to my bosses what it meant, especially regarding one of our project where we store a lot of user data. Then I heard it: "this crap doesn't regard us. we have no sensitive data. we only save out users' name and generalities.". I have no words.3
-
Well... I feel insanely stupid because I've been using windows for years an just realised that the file system isn't case sensitive... Mother fuckers...
(Yes judge me, I am a twat)7 -
Finally fixed a major bug.....
FUCK YOU C# AND YOUR FUCKING CASE SENSITIVE BULLSHIT.
DAYS
THAT TOOK FUCKING DAYS AND AT NO POINT DUD VISUAL STUDIO BOTHER TO MENTION THAT FUCKING ERROR.
1 CHARACTER, ON ONE LINE, EFFECTIVELY BROKE THOUSANDS OF LINES OF CODE
fuck this, I quit. See you next time you contact the Microsoft live support chat!13 -
I can't believe people are willing to scan their faces, fingerprints, and retinas on their phones.
Such data is very sensitive as it can't be changed easily.
CCTV is now everywhere and everyone has his own scanner providing data for tracking people.
Am I too paranoid?6 -
Watch out for these fucking bug bounty idiots.
Some time back I got an email from one shortly after making a website live. Didn't find anything major and just ran a simple tool that can suggest security improvements simply loading the landing page for the site.
Might be useful for some people but not so much for me.
It's the same kind of security tool you can search for, run it and it mostly just checks things like HTTP headers. A harmless surface test. Was nice, polite and didn't demand anything but linked to their profile where you can give them some rep on a system that gamifies security bug hunting.
It's rendering services without being asked like when someone washes your windscreen while stopped at traffic but no demands and no real harm done. Spammed.
I had another one recently though that was a total disgrace.
"I'm a web security Analyst. My Job is to do penetration testing in websites to make them secure."
"While testing your site I found some critical vulnerabilities (bugs) in your site which need to be mitigated."
"If you have a bug bounty program, kindly let me know where I should report those issues."
"Waiting for response."
It immediately stands out that this person is asking for pay before disclosing vulnerabilities but this ends up being stupid on so many other levels.
The second thing that stands out is that he says he's doing a penetration test. This is illegal in most major countries. Even attempting to penetrate a system without consent is illegal.
In many cases if it's trivial or safe no harm no foul but in this case I take a look at what he's sending and he's really trying to hack the site. Sending all kinds of junk data and sending things to try to inject that if they did get through could cause damage or provide sensitive data such as trying SQL injects to get user data.
It doesn't matter the intent it's breaking criminal law and when there's the potential for damages that's serious.
It cannot be understated how unprofessional this is. Irrespective of intent, being a self proclaimed "whitehat" or "ethical hacker" if they test this on a site and some of the commands they sent my way had worked then that would have been a data breach.
These weren't commands to see if something was possible, they were commands to extract data. If some random person from Pakistan extracts sensitive data then that's a breach that has to be reported and disclosed to users with the potential for fines and other consequences.
The sad thing is looking at the logs he's doing it all manually. Copying and pasting extremely specific snippets into all the input boxes of hacked with nothing to do with the stack in use. He can't get that many hits that way.4 -
Jesus Christ Reddit really is full of some sensitive ass basement dwelling retards. God forbid someone doesn't contribute to the circle jerk mentality that literally every fucking subreddit has.
I bet SO users spend their free time there.11 -
So you want to collect and save sensitive data from psychologists sessions and use Wordpress. What can go wrong.2
-
WELL GEE, IF I KNEW WHAT MY ACCOUNT USERNAME WAS, I WOULD JUST SIGN IN YOU ASSHOLE. -.-
On top of that, they use these fucking anchent capchas that are fucking case sensitive and annoying as hell..
In their defence, I was trying to automate their website (one of those get paid to click sites) in an atempt to get some money, but still! 6
6 -
Inappropriate experience at work: One of our project managers got arrested one day for fraud. Apparently an employee had been in the middle of an online purchase and walked away from their desk. He happened to see the unmasked entry of the CC info (this was before websites cared about masking sensitive form inputs). I guess the temptation was too great…and he was too stupid to realize he’d get caught…and he jotted it all down. He made thousands of dollars in purchases which, naturally, eventually led back to him.
The same guy, before he got arrested, had made a joke when someone in an office team email said “Feel free to have some cake in the break room.” He replied “No need to do anything to me for the cake.” His first name was “Free”.5 -
Am i the only one who is so sensitive about indentation? It really pisses me off when i see code with bad levels of indentation because it completely overtakes my years of programming experience and i understand nothing. Also indentation level should be 4, not 2. Who the hell uses 2 level indentation, you don't deserve a keyboard.9
-
The company that I currently work for has a strict clean-desk policy. So strict, there's even have a little booklet that they have about 1000 copies of lying around the office everywhere. In the booklet is a playful description (with cartoons!) of what can go wrong when sensitive information is lying around, or shared with outsiders through careless talk, etcetera. Employees are encouraged to take a copy of the booklet home.
Also in the booklet is a description of the importance of having a good password. It mentions the required minimum (x) and maximum (x+1) length of passwords, mandatory character classes, and how often the passwords have to be changed.6 -
A colleague of mine had to debug performance problems in a foreign, proprietary application that is ancient.
To be crystal clear: Only reason that thing exists is because some old geezers fear change.
Asked me for help cause it's an _ancient_ MS SQL server that is luckily running on hardware owned by us.
Finding the credentials was already a funny task.
We had to access the vault (not joking here, we have a physical vault for storing sensitive data and critical backups), grab a folder and find the necessary data cause no one ever dares to touch that thing.
The application is btw for a sort of ERP / inventory system that is used in some ancient shops not yet migrated...
Yeah. Story speaks for itself.
Anyway, after dusting off ourselves, we were able to connect.
Was a bit ... Interesting. Everything's in german. The worst kind of german.
After looking at the first tables, I started giggling.
My colleague knew immediately that this was a sign of danger (insert Simpson meme here), raised his eyebrows and asked "How bad is it....".
Me, still giggling, "lemme take a further look, this is gold".
*long sigh from the colleague*
Well... It ended with me putting my hands in front of my eyes, turning around and saying: "I cannot look at it anymore, it hurts too much...."
To summarize:
- German table names
- When a table exceeded 300 plus columns, they added another table with the same plus suffix "_ddd"… where ddd is an zero filled integer sequence like 001
- To join this mess, they created views... Named "generator" - Sequence Number ... Some had the beginning of table names appended, which doesn't make it less confusing.
- the process list was listing queries running longer than 5 mins.
Which isn't at all surprising when generating carrtesian products of N tables with left join.
I've seen shit.... I've seen a lot of shit.
But that shit scared me.1 -
Trying to explain functions to my coworker and why they should be used even if powershell scrips don't 'need' functions
I've explained it 5 different ways across multiple meetings when they've gotten stuck on something.
At this point I've decided 1. I don't have the patience or brains to be a teacher..., 2. I'm going to have to review every script they ever fucking write, 3. I'm never letting them work on anything critical or time sensitive for big clients. (Small clients ehhh) I'll fight my boss to avoid that headache lol7 -
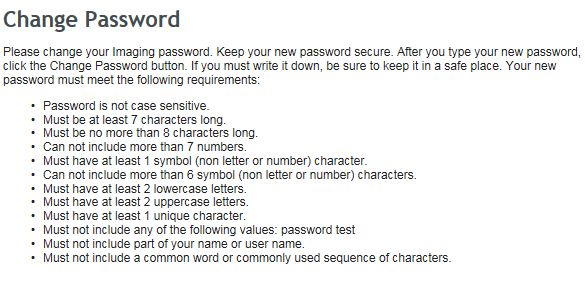
So, among the ridiculously long list of password requirements, password is not case sensitive BUT it has to contain uppercase and lowercase letters?
 14
14 -
WTF!!!!! I officially have someone trying to extort me just had this in my email box this morning!
--------
Hello,
My name is [name removed], I'm an IT security expert and I found a security issue on your website.
This email is personal and in no way related to any of my employers.
I was able to access to a lot of files which contains sensitive data.
I attached a screenshot of the files I found to this email.
I would be happy to give you the method I used to access these files in order to let you fix it.
Would be a monetary compensation possible?
Please forward this email to the right person, if your are not responsible for the security of the website.
Best Regards,
[name removed]
---
He can basically see the contents of my wp-config.php. How has he managed this?71 -
Apparently USPS tracking numbers are case sensitive... I missed a delivery today so went online to check the status.
The code was RAxxxxxxxxxxxxxxxxxxxTR
x=numbers
I first typed the letters in lowercase and it said package not found...
Really???!!!!!! Don't you think all those numbers are already too long...3 -
<supervisor>,
I would like to raise a concern of mine to your attention. I would urge you to inform <CIO> because I think he should know as well. In our recorded meeting this afternoon <bad_vendor> exposed another company’s credentials after failing to access our system, and proceeded to demo access into someone else’s system while exposing their client's sensitive data. Others noticed this as well. This is an alarming situation because not only did <bad_vendor> expose someones data to <us>, but to one of our vendors. While it is unlikely that <us> or <helpful_vendor> would abuse this situation, it could have easily been <us>’s data that was exposed to another company and their vendors had the situation been reversed. I understand we are all under tight deadlines and under a lot of stress — by no means am I trying to make waves — but nonetheless I felt compelled make light of this situation and felt in was echoed by <helpful_vendor> during the meeting as well.
Thank you8 -
What in the unholy fuck is going on with the world!!
I get how our personal lives and data are bloody good at being used against us and tracking our behaviours but fuck Facebook won't let "good enough" alone and are coming back out with a new way to pay for our most sensitive data. Everything on your phone!
What more could they possibly want from knowing what,where,who,why,when, and probably even how we are shitting in a back ally besides controlling the masses
- no I'm not a privacy nut, just a concerned citizen -
https://theverge.com/2019/6/...3 -
Using pokemon exeption handling on some very important and sensitive back end stuff to meet a deadline.7
-
How I met python
[long read but worth]
There's nothing wrong with falling in love with a programming language for her looks. I mean, let's face it - Python does have a rockin' body of modules, and a damn good set of utilities and interpreters on various platforms. Her whitespace-sensitive syntax is easy on the eyes, and it's a beautiful sight to wake up to in the morning after a long night of debugging. The way she sways those releases on a consistent cycle - she knows how to treat you right, you know?
But let's face it - a lot of other languages see the attention she's getting, and they get jealous. Really jealous. They try and make her feel bad by pointing out the GIL, and they try and convince her that she's not "good enough" for parallel programming or enterprise-level applications. They say that her lack of static typing gives her programmers headaches, and that as an interpreted language, she's not fast enough for performance-critical applications.
She hears what those other, older languages like Java and C++ say, and she thinks she's not stable or mature enough. She hears what those shallow, beauty-obsessed languages like Ruby say, and she thinks she's not pretty enough. But she's trying really hard, you know? She hits the gym every day, trying to come up with new and better ways of JIT'ing and optimizing. She's experimenting with new platforms and compilation techniques all the time. She wants you to love her more, because she cares.
But then you hear about how bad she feels, and how hard she's trying, and you just look into her eyes, sighing. You take Python out for a walk - holding her hand - and tell her that she's the most beautiful language in the world, but that's not the only reason you love her.
You tell her she was raised right - Guido gave her core functionality and a deep philosophy she's never forgotten. You tell her you appreciate her consistent releases and her detailed and descriptive documentation. You tell her that she has a great set of friends who are supportive and understanding - friends like Google, Quora, and Facebook. And finally, with tears in your eyes, you tell her that with her broad community support, ease of development, and well-supported frameworks, you know she's a language you want to be with for a long, long time.
After saying all this, you look around and notice that the two of you are alone. Letting go of Python's hand, you start to get down on one knee. Her eyes get wide as you try and say the words - but she just puts her finger on your lips and whispers, "Yes".
The moon is bright. You know things are going to be okay now.10 -
Did you hear that GitHub is planning to rename racially sensitive terms like "master"?
My two cents: rename master to daddy. xD10 -
So we have an API that my team is supposed send messages to in a fire and forget kind of style.
We are dependent on it. If it fails there is some annoying manual labor involved to clean that mess up. (If it even can be cleaned up, as sometimes it is also time-sensitive.)
Yet once in a while, that endpoint just crashes by letting the request vanish. No response, no error, nothing, it is just gone.
Digging through the log files of that API nothing pops up. Yet then I realize the size of the log files. About ~30GB on good old plain text log files.
It turns out that that API has taken the LOG EVERYTHING approach so much too heart that it logs to the point of its own death.
Is circular logging such a bleeding edge technology? It's not like there are external solutions for it like loggly or kibana. But oh, one might have to pay for them. Just dump it to the disk :/
This is again a combination of developers thinking "I don't need to care about space! It's cheap!" and managers thinking "100 GB should be enough for that server cluster. Let's restrict its HDD to 100GB, save some money!"
And then, here I stand trying to keep my sanity :/1 -
We live in a world where WEAKNESS has become a virtue.
- I'm oppressed!
- My mental health!
- I need a helper!
- I'm sensitive!
- You're fatphobic!
- <INSERT SJW's IDENTITY term>
In today's world, you score more social points for describing yourself as weak & blaming 'oppressors' for your miserable life12 -
I am so mentally drained from having to deal with the intern who I have to literally spoon-feed every single thing. My previous posts illustrate the situation...
The language and cultural barriers are too much, and I am too afraid to open my mouth because of the sensitive nature of my country's history and I'll get labelled as some horrible person.
I told my manager today that I'll stick it out until end of January (thankfully I am on vacation for most of December and January), but I cannot work with her. She was supposed to move to the data team end of December, but my manager told me if she can't even properly grasp this HTML and CSS stuff, then she will not be able to do the other tasks they have for her.
This was a disaster of an experiment and I'm somewhat traumatised ( I am sure the intern is too) and I never want another intern again, nor do I want to manage people. I never said I want to be a people manager, I just want to quietly code at my desk.
This company sells MBTI psychometric assessments and they damn well know my preference, so I'm seriously annoyed that they threw this horrendous surprise on me and kept ignoring my requests for revisiting this intern's role, because I noticed a long time ago that she was struggling with basic concepts and all they did was make her do Udemy courses.
I told them multiple times that she seriously needs computer literacy training because she will not survive in this industry if she still struggles to understand how files and folders work. Other employers would have fired her a long time ago.
She's just too slow for this job. I feel sorry for her, but I do not have the capacity to do this anymore. I'm tired, it's been a long year.6 -
Hi
I'm an active user here so I know most of you.
I created a throwaway because I consider this a sensitive subject to me, and don't want people here to think I'm crazy.
I have some form of ocd but I don't know exactly which subtype it is.
It's not really something that makes my life impossible, but it makes me feel awful from time to time.
the way it works is that I imagine accidents happening to me or people I love, and I get triggered more if they are potentially caused by a mistake from me and they feel very vivid in my mind.
It's awful and terrifying.
Being close to anything that could cause harm is a trigger:
heights without any type of fall protection, knives, elevators, escalators, being on a plane
Being close to/in said objects/situations can start a clip in my mind as if I was watching a final destination movie.
This is a stronger obsession if it happens because of my fault, like tripping with my kid in my arms, or fumbling a knife while I cook.
Sometimes I react by curling and doing a painful expression and twitching a bit, even in public.
it's terribly painful.
i look like a crazy person, although considering what I'm writing, i probably am. It's just that I feel very scared of strangers in public noticing what I'm doing and finding out I'm crazy.
sometimes I get scared of the possibility of me being an actual psycho like the ones you see on crime shows.
as far as i know i think im normal in terms of compassion, empathy to others and never had any interest in harming others.
it's just part of the ocd, being hypervigilant of me, obsessing over me causing harm either accidentally or deliberately.
I'm also very scared of puking in public, or even worse, in front of friends.
Specially true if you're eating but you're seated in a spot where there's no way out except if everybody gets up.
I start by becoming self conscious of the possibility of puking, and sometimes I twitch a bit too, while trying to not look too crazy and joping that the next bite doesn't cause me to projectile vomit over people.
I hate this shit.15 -
"Unix filenames are case-sensitive?! Hur hur, that must be really confusing!"
Well, no, if you're not a fucking mouth-breathing cretin it isn't.2 -
mangodb's rant reminded me of smth.. Folks from my country might remember this story.
So we have a national e-health system. Millions have been invested, half of the money have never reached the project [disappeared smwhr in between] and its quality is not shiny. It works, sometimes even fast enough. But boy does it have bugs... Let's not get into that. It's politics.
So some time ago one IT guy spotted a bug that allowed him to get sensitive info of other patients. He informed e-health folks and waited for a fix. He waited for a few weeks but the fix had never been released. So he published his findings in soc media [yepp.. Stupid move]. That caused a national scandal. Not to mention he had been pressed with charges.
That guy and our health minister were invited in one of the tv debates. The guy was asked to explained how he found all this sensitive data. And he explained that he hit f12 in his browser, opened a network tab, issued a network request by clicking smth in the webpage analysed received data in the dev tools.
The minister looked somewhat happy, maybe a lil proud of himself - a person who has a "gotcha!" moment has that very glow he had. And he said: "what you did there was obvious hacking. I reckon you should know that true developers do not do those things you have just explained to us" [he was talking about dev tools].
I died inside a little bit.3 -
My first interview ever for an internship. The interviewer asked me to rate myself in this language from 1 to 10 as if I'm applying for a lead engineer position at Google. I replied with a number that I thought was appropriate at the time (but now I know it wasn't accurate). The interviewer didn't say anything and moved to the next question. Later, I found out he ranted about my answer on his Twitter, again as if it's expected from an applicant intern at a low tier company to know. Still leaves a bitter taste in my mouth 7 years later.8
-
DXB (airport)'s WiFi doesn't let you call through whatsapp or telegram or even discord. It also does not let you send a whatsapp voice message, which has me very puzzled.
And all I wanted to do was to call my mom. ☹️
(I might also be running a slight fever, which makes me very emotional and sensitive)12 -
Whoever at Zoom decided that this button needed to be at this location on the Touch Bar ought to be fired.
Out of a cannon.
Into the sun.
Or at the very least doomed to have their desktop or webcam shared at random times during sensitive meetings. It is for the grace of God that the client didn’t catch me straining to hear the awful acoustics in their conference room. 7
7 -
I really enjoy my old Kindle Touch rather than reading long pdf's on a tablet or desktop. The Kindle is much easier on my eyes plus some of my pdf's are critical documents needed to recover business processes and systems. During a power outage a tablet might only last a couple of days even with backup power supplies, whereas my Kindle is good for at least 2 weeks of strong use.
Ok, to get a pdf on a Kindle is simple - just email the document to your Kindle email address listed in your Amazon –Settings – Digital Content – Devices - Email. It will be <<something>>@kindle.com.
But there is a major usability problem reading pdf's on a Kindle. The font size is super tiny and you do not have font control as you do with a .MOBI (Kindle) file. You can enlarge the document but the formatting will be off the small Kindle screen. Many people just advise to not read pdf's on a Kindle. devRanters never give up and fortunately there are some really cool solutions to make pdf's verrrrry readable and enjoyable on a Kindle
There are a few cloud pdf- to-.MOBI conversion solutions but I had no intention of using a third party site my security sensitive business content. Also, in my testing of sample pdf's the formatting of the .MOBI file was good but certainly not great.
So here are a couple option I discovered that I find useful:
Solution 1) Very easy. Simply email the pdf file to your Kindle and put 'convert' in the subject line. Amazon will convert the pdf to .MOBI and queue it up to synch the next time you are on wireless. The final e-book .MOBI version of the pdf is readable and has all of the .MOBI options available to you including the ability for you to resize fonts and maintain document flow to properly fit the Kindle screen. Unfortunately, for my requirements it did not measure-up to Solution 2 below which I found much more powerful.
Solution 2) Very Powerful. This solution takes under a minute to convert a pdf to .MOBI and the small effort provides incredible benefits to fine tune the final .MOBI book. You can even brand it with your company information and add custom search tags. In addition, it can be used for many additional input and output files including ePub which is used by many other e-reader devices including The Nook.
The free product I use is Calibre. Lots of options and fine control over documents. I download it from calibre-ebook.com. Nice UI. Very easy to import various types of documents and output to many other types of formats such as .MOBI, ePub, DocX, RTF, Zip and many more. It is a very powerful program. I played with various Calibre options and emailed the formatted .MOBI files to my Kindle. The new files automatically synched to the Kindle when I was wireless in seconds. Calibre did a great job!!
The formatting was 99.5% perfect for the great majority of pdf’s I converted and now happily read on my Kindle. Calibre even has a built-in heuristic option you can try that enables it to figure out how to improve the formatting of the raw pdf. By default it is not enabled. A few of the wider tables in my business continuity plans I have to scroll on the limited Kindle screen but I was able to minimize that by sizing the fonts and controlling the source document parameters.
Now any pdf or other types of documents can be enjoyed on a light, cheap, super power efficient e-reader. Let me know if this info helped you in any way. 4
4 -
I dropped my kid off at preschool and went my way home.
She's 2 so I transport her on a stroller.
While coming back, I came across an old lady sweeping the sidewalk of her house, and it got narrow to pass through because there was a tree next to her.
I carefully slowed down as to not collide with her, and while going through, we noticed each other.
I did a tiny smile as a way of saying "hi" like I usually do to people on the street.
To which she gave back the most innocent and sweet smile I've ever seen a stranger give on the street.
I could honestly feel my heart crack as it happened.
I guess the stroller must have caused her sympathy thus that reaction.
(which is why I like going around with the stroller, because people tend to treat you nicely which feels nice, like butterflies)
I know it might seem like an ordinary story without a punchline, but let me explain that I walk this city everyday.
And even though the people here is very nice compared to other cities I've lived in, it is very rare to get smiled at with such joy.
You might still think that is not a good story. But I can explain its relevance.
As some of you know, I post triggering content on this account, closeted parts of me that I normally hide,
Such as sexual stuff, some people think I'm a degenerate but I like to think I just have normal sexual thoughts that don't affect others in real life AT ALL.
And I'm also very argumentative, again, some people might see it as troll behaviour. On my side though, I just don't like bullshit and call it out when I see it.
But with this post, I'm not trying to be more likable or negate all the weird shit I said. This post is just another closeted part of me, being emotional.
And the reason I hide that is because it is not generally well accepted when a man is sensitive, at least where I'm from.
For example, if a female friend at work had a nice haircut, sometimes I feel the urge to be like "omg girl you look so prettyyyy!!!!".
But if I did that I know what will happen based on DIRECT experience: people will assume I'm gay or weak, and will make fun of that.
Or the actual friend will think I'm hitting on her.
No, fucking thank you, not having that shit.
But even if people accepted that, they just can't conceive I'm also very direct and honest, so when they do get to know me better, they get shocked.
So what do I do? I just hide that. That might change in the future, but I don't have the energy right now to deal with some people's simplemindedness.
I'm not making any sort of political statement, like "people should be treat me correctly or else get fired because of offending my gender".
But I'm not gonna lie, it would feel very nice if I was around more progressive people. I wished I had just just standard male behaviour and thoughts.
I guess some people in progressive cities are more accepting of the whole gender fluid thing, so I wished I lived in one (let me clarify though, I'm not a mindless gender fanatic).
I'm also not perfect and sometimes the line between "I love your haircut" and "I'm into you" blurs the fuck out, so that's on me... I don't know if it's something I can change though...
Hopefully all this shit I'm saying doesn't make me look like a lunatic. Veeeery hopefully.
Though, If you think for real I'm a lunatic or bad person, you can suck donkey dick.14 -
This is from the 70s. It can easily be updated to the present day, but it has a certain charm just the way it is:
Three women sat discussing their husbands and their sex lives.
"My husband's a wrestler," said the first. "He's really strong and aggressive in bed."
"My husband's an artist," said the second. "He's really gentle and sensitive."
"My husband's an IBM salesman," said the third. "He sits on the edge of the bed and tells me how good it's going to be when I finally get it." -
Update: https://devrant.com/rants/5445368/...
My previous bosses were real awesome people. However, the current one is an intentional asshole.
He wants to review every piece of work. He thinks I am a retard who knows shit. He has no sense of feedback vs. humiliating criticism.
Fucker questions every single word.
For example, consider the following statement, "They are taking the Hobbits to Isengard."
He'd critical question every word like,
What do you mean by 'they'?
Why have you mentioned it?
Why does 'They' exists in English vocabulary?
Why cannot you try 'Your'?
What data points you have?
And after endless questioning, he'd repeat the same with next word. Making sure to break my spirit of working for him.
And let me add that his communication is saturated with heavy jargons which are difficult to understand. At times, I slow down to understand and absorb and he has a problem with that as well.
My past experience says that I learned a lot from strict managers.
But this fucker intentional criticises every aspect with zero to negative appreciation. All in the name of feedback.
I have gotten tons of compliments and good ratings in the past based on my communication and thought process. However, this fucker feels that my thought process is shit and I don't know how to communicate. Furthermore, he feels that I lack sense of ownership.
I really don't know what he saw in my resume or me to even hire me in the first place.
Given how he treats me and others, no wonder people are leaving. And if he fires me, good luck to him finding a sensible replacement who matches his expectations or puts up with his crap.3 -
I have a few of these so I'll do a series.
(1 of 3) Public privates
We had a content manager that created a content type called "news item" on a Drupal site. There where two file fields on there. One called "attachments" and the other called "private attachments". The "private attachments" are only for members to see and may contain sensitive data. It was set to go trough Drupals security (instead of being directly hosted by the webserver) but because the permissions on the news items type where completely public everybody had access. So basically it was a slow public file field.
This might be attibuted to ow well Drupal is confusing. Howerver weeks earlier that same CM created a "private article". This actually had permissions on the content type correctly but had a file field that was set to public. So when a member posted the URL to a sensitive file trough unsafe means it got indexed by google and for all to read. When that happend I explained in detail how the system worked and documented it. It was even a website checklist item.
We had two very embarrassing data leaks :-(1 -
Our company is changing the default branch on our main repo from master to main.
We're literally on the verge of global genocide and a holocaust, and people are worried about over-sensitive people's feelings. I'm sure a branch change will end racism.6 -
Paranoia. Programming affected my life by making me paranoid. Creating a new account on any website that even needs rudimentary information about me has to go quite some vulnerability testing since I've seen enough hack jobs that throw around sensitive data because they're too incompetent to follow simple must dos.3
-
"Let‘s make a service where the users can enter all of their secrets and sensitive data so that we can warn them if that data has been leaked elsewhere"
What could possibly go wrong?2 -
One of my customers' laptop background (removed sensitive information and desktop icons).
Coworker: When you really love Chrome, but don't know what hi-res is! 8
8 -
Had a conference call and one of the guys said something along the lines of "I can handle the load (ticket load)" didn't even thought about it my mouth instinctively reacted with "that's what she said".
A couple of guys laughed but the other few just "wooooow"ed like if I had thrown a 9/11 joke.
This is not a rant perse, just a reminder that if I ever launch my own startup I shall look to hire "joke sensitive" people to make my scrum meetings as awkward as possible.4 -
Fuck you Intel.
Fucking admit that you're Hardware has a problem!
"Intel and other technology companies have been made aware of new security research describing software analysis methods that, when used for malicious purposes, have the potential to improperly gather sensitive data from computing devices that are operating as designed. Intel believes these exploits do not have the potential to corrupt, modify or delete data"
With Meltdown one process can fucking read everything that is in memory. Every password and every other sensible bit. Of course you can't change sensible data directly. You have to use the sensible data you gathered... Big fucking difference you dumb shits.
Meltown occurs because of hardware implemented speculative execution.
The solution is to fucking separate kernel- and user-adress space.
And you're saying that your hardware works how it should.
Shame on you.
I'm not saying that I don't tolerate mistakes like this. Shit happens.
But not having the balls to admit that it is because of the hardware makes me fucking angry.5 -
Client: MY PASSWORD DOESN'T WORK
Me: our passwords are case-sensitive
Client: YES I USED CAPS LOCK1 -
PyTorch.
2018: uh, what happens when someone uses a same name attack? - No big deal. https://github.com/pypa/pip/...
2020: I think that's a security issue. - Nanana, it's not. https://github.com/pypa/pip/...
2022: malicious package extracts sensitive user data on nightly. https://bleepingcomputer.com/news/...
You had years to react, you clowns.6 -
I don't want to put anyone to shame here, but this has been the most hilarious password reset in my life.
P.S.
It's an early service with no sensitive data, so I'm not concerned so much, but still, a system for automatic password reset, with the ability to change the temporary one, should be one of the first things in place before you go public. lol 4
4 -
I came around the corner in the corridor where a senior PM talked with an engineer.
PM: ... and that's why a good team is so important and we also need sensitive people.
Me: do we have some here?
PM: oh yes, I'm highly sensitive.
Me: one learns something new every day. :-)1 -
As usual a rather clickbait title, because only the chrome extensions (as always) seem to be vulnerable:
"Warning – 3 Popular VPN Services Are Leaking Your IP Address"
"Researchers found critical vulnerabilities in three popular VPN services that could leak users' real IP addresses and other sensitive data."
"VPN Mentor revealed that three popular VPN service providers—HotSpot Shield, PureVPN, and Zenmate"
"PureVPN is the same company who lied to have a 'no log' policy, but a few months ago helped the FBI with logs that lead to the arrest of a Massachusetts man in a cyberstalking case."
"Hijack all traffic (CVE-2018-7879) "
"DNS leak (CVE-2018-7878)"
"Real IP Address leak (CVE-2018-7880)" 7
7 -
Dont become a dev if you:
- Cant sit in the office for 8-10 hours a day
- Dont know how to google information/ errors, instead you interrupt your teammates with stupid questions every 5 minutes
- Are a perfectionist and don't like constant change.
- Are neurotic and give up easily. If you get triggered about broken or messy things to the point where it ruins your day to you and everyone else around you. You need to separate your work from your life.
- Don't have good communication skills. Worst I saw was a guy who speaks with a stutter(nobody understands him) and also writes very poorly (nobody understands his emails). Also he gets very angry when you ask additional questions to clarify what he said. How can you work with someone like that?
- Are very sensitive to critique. I prefer someone telling me that my code is shit and telling me why, instead of feeding me delusions and false validation.
- Dont know how to balance working in team and working solo. Nobody likes lone wolfs who are arrogant and not in sync with the team. But also nobody likes to drag teammates who cant think for themselves and even after years of spent in the field are required constant spoonfeeding because they are unable to google and teach themselves with trial and error.14 -
Renting a flat above a kindergarten.
I hate Christmas songs and I am very sensitive to high pitched noises.
It's a bad time in the year to be working from home...3 -
Your guide to passive-aggressive false apologies:
- I’m sorry you’re so sensitive
- I’m sorry that you think I did something wrong
- I’m sorry if you’re mad
- I’m sorry that you made me do it
- I’m sorry you feel that way
And, my most favorite:
- I’m sorry that you’re making such a big deal out of this.12 -
pushing sensitive data to GitHub repo...not realising for days...and then going through the painful process of removing it again 😑4
-
Interesting. A few hours ago I had a nice domestic conversation with my coleague about robot vacuum cleaners. He was talking about iRobot Roomba and I was talking about Xiaomi. Here's the result!
Interesting thing is that we talked in a *voice* conversation. Over Slack. Over Chrome. Over corporate VPN (openconnect).
Where's the spying link? Slack or Chrome?
My bet's on Chrome.
What does that tell you about the privacy of your sensitive conversations? :)
Hide behind VPNs all you like. If you have proprietary software (or hardware in the case of Huawei) - you're being watched and listened to.
EDIT: I'm on Linux, he's on MacOS 9
9 -
Does anybody here know of some sort of blackout glasses? (which cover the entire eyes, not sunglasses which do exist in high filters, but leak sunlight at the bottom, top and sides)
My recent lifestyle has lead me to absolutely dying at the morning when I go sleep, because of the extreme sunlight, peaking through all cracks.
I am just fine during the day when I do my walks or drive to the store etc, but after a long night I just get very light and sound sensitive.
I think a decent amount of years ago, I saw somebody use some sort of small scale welding goggles for something similar, but I can't find any that are dark enough or aren't costing like buying a beach house in malibu.
Also "photophobia glasses", which actually seem to be for that purpose, cost like two malibu beach houses and a helicopter to top it off, because they abuse and cash on the fact that it has remote help to people that suffer from it.
I did also try just using blackout curtains for that purpose, but as said, there's always that one small crack where it leaks through and absolutely flashbangs me.
So it would be nice to have some glasses that filter pretty much 99% of light, but still allow me to navigate through my appartment, without having to break a leg or crack my neck (which would solve the problem atleast)22 -
I'm a TA myself and just yesterday wanted to defend my fellow TAs and CS/IT teachers from some of the rants here. Of course not all of the rants are but I found a few quite unfair towards us and I can fully understand a TA getting confused and tired after 5-7 hours of helping and wrapping your head around some of the harder problems the students run into.
However, I'm also a student myself and right now I'm fucking fed up with the shit my supervisor gives me regularly .. So let the rant flow!
(disclaimer: the following text uses “you” to address the rant recipient. So, dear reader, don't feel offended)
First of, why do you fucking care when and especially where I'm working on your project when you know I'm only working part time since I'm usually tutoring students by daylight. Having me come in after my TA shift to work on your project instead of letting me go home, get some rest and food, and start working with a fresh head is neither helping you nor very productive. Also, if you want me to be productive and use your fucking tools to get going faster you better not make me fucking debug your fucking tools. For instance, I don't even have the same first name so all your fucking paths are invalid on my fucking machine! Also, I get that your machine is more powerful than mine and I don't really care about it as long as you don't fucking push convoluted messy timing sensitive scripts and make me search for the correct values on my machine. And, if a file your script is trying to delete is not there aborting is not an valid exception handling!
And don't get me started on the scripts that actually do some work besides setting up your fucking toolchain! -
Had anyone experienced with an impatient boss who require you to complete the project in the month you just recently got hired?
Here's the story, I recently got hired by a company, joined on 1st April 2022, the boss expect me to complete the app for Android and iOS by the end of this month. (An e-commerce applications exactly like shopee.com) Without providing me the Backend ApI , that they mentioned. They just gave me a and expect me to know what's happening at the backend.
He require me to give him a specific date that I can launch the app to play store and Apple store. (From my experience, it take days, weeks or months). He need a milestone of what I need , did , and will do (which predictably that they will reject any new ideas proposed) .
I even considering to quit, but I need opinions. Am I just too sensitive or there's something wrong?15 -
Whelp. I started making a very simple website with a single-page design, which I intended to use for managing my own personal knowledge on a particular subject matter, with some basic categorization features and a simple rich text editor for entering data. Partly as an exercise in web development, and partly due to not being happy with existing options out there. All was going well...
...and then feature creep happened. Now I have implemented support for multiple users with different access levels; user profiles; encrypted login system (and encrypted cookies that contain no sensitive data lol) and session handling according to (perceived) best practices; secure password recovery; user-management interface for admins; public, private and group-based sections with multiple categories and posts in each category that can be sorted by sort order value or drag and drop; custom user-created groups where they can give other users access to their sections; notifications; context menus for everything; post & user flagging system, moderation queue and support system; post revisions with comparison between different revisions; support for mobile devices and touch/swipe gestures to open/close menus or navigate between posts; easily extendible css themes with two different dark themes and one ugly as heck light theme; lazy loading of images in posts that won't load until you actually open them; auto-saving of posts in case of browser crash or accidental navigation away from page; plus various other small stuff like syntax highlighting for code, internal post linking, favouriting of posts, free-text filter, no-javascript mode, invitation system, secure (yeah right) image uploading, post-locking...
On my TODO-list: Comment and/or upvote system, spoiler tag, GDPR compliance (if I ever launch it haha), data-limits, a simple user action log for admins/moderators, overall improved security measures, refactor various controllers, clean up the code...
It STILL uses a single-page design, and the amount of feature requests (and bugs) added to my Trello board increases exponentially with every passing week. No other living person has seen the website yet, and at the pace I'm going, humanity will have gone through at least one major extinction event before I consider it "done" enough to show anyone.
help4 -
A good life lesson:
1. DON'T DELETE FILES YOU MAY WANT TO RECOVER
And if you DO delete them and then recover them, then
2. DON'T SEND THE RECOVERED FILES TO A·N·Y·O·N·E
Today I found a lost µSD card in the street. I did what every sane person would do -- plugged it into my laptop :)
There I found a directory with recovered pictures. I figured, some of them may contain the author's info in metadata, so I ran a quick plaintext search for @gmail.com.
Turns out, inside some of the recovered picture files I could find embedded company director's emails in plain-text. I mean, open the picture with a text editor and read through those emails - no problem! And these emails contain some quite sensitive info, e.g. login credentials (lots of them).
Bottom line, if you delete and recover your files, then do your best to keep them close: don't share them, don't lose them. You might be surprised what these recovered files may contain15 -
My grandfather is at age 72 & don't know much about technology. He forward me this message on whatsapp bcz I'm a software engineer. He made my day...
What is the difference between http and https ?
Time to know this with 32 lakh debit cards compromised in India.
Many of you may be aware of this difference, but it is
worth sharing for any that are not.....
The main difference between http:// and https:// is all
about keeping you secure
HTTP stands for Hyper Text Transfer Protocol
The S (big surprise) stands for "Secure".. If you visit a
Website or web page, and look at the address in the web browser, it is likely begin with the following: http:///.
This means that the website is talking to your browser using
the regular unsecured language. In other words, it is possible for someone to "eavesdrop" on your computer's conversation with the Website. If you fill out a form on the website, someone might see the information you send to that site.
This is why you never ever enter your credit card number in an
Http website! But if the web address begins with https://, that means your computer is talking to the website in a
Secure code that no one can eavesdrop on.
You understand why this is so important, right?
If a website ever asks you to enter your Credit/Debit card
Information, you should automatically look to see if the web
address begins with https://.
If it doesn't, You should NEVER enter sensitive
Information....such as a credit/debit card number.
PASS IT ON (You may save someone a lot of grief).
GK:
While checking the name of any website, first look for the domain extension (.com or .org, .co.in, .net etc). The name just before this is the domain name of the website. Eg, in the above example, http://amazon.diwali-festivals.com, the word before .com is "diwali-festivals" (and NOT "amazon"). So, this webpage does not belong to amazon.com but belongs to "diwali-festivals.com", which we all haven't heard before.
You can similarly check for bank frauds.
Before your ebanking logins, make sure that the name just before ".com" is the name of your bank. "Something.icicibank.com" belongs to icici, but icicibank.some1else.com belongs to "some1else".
👆 *Simple but good knowledge to have at times like these* 👆3 -
I need someone to make me a list of things I am not allowed to say and who I’m not allowed to say them to at work. This is getting ridiculous. Every time I turn around someone is making this face at me 😬 and saying “Don’t say that to that team” or “Don’t say that to this person”. I can’t do my work right if I have to keep censoring myself on everything people find organizationally sensitive.19
-
In today's episode of kidding on SystemD, we have a surprise guest star appearance - Apache Foundation HTTPD server, or as we in the Debian ecosystem call it, the Apache webserver!
So, imagine a situation like this - Its friday afternoon, you have just migrated a bunch of web domains under a new, up to date, system. Everything works just fine, until... You try to generate SSL certificates from Lets Encrypt.
Such a mundane task, done more than a thousand times already... Yet... No matter what you do, nothing works. Apache just returns a HTTP status code 403 - Forbidden.
Of course, what many folk would think of first when it came to a 403 error is - Ooooh, a permission issue somewhere in the directory structure!
So you check it... And re-check it to make sure... And even switch over to the user the webserver runs under, yet... You can access the challenge just fine, what the hell!
So you go deeper... And enable the most verbose level of logging apache is capable of - Trace8. That tells you... Not a whole lot more... Apparently, the webserver was unable to find file specified? But... Its right there, you can see it!
So you go another step deeper and start tracing the process' system calls to see exactly where it calls stat/lstat on the file, and you see that it... Calls lstat and... It... Returns -1? What the hell#2!
So, you compile a custom binary that calls lstat on the first argument given and prints out everything it returns... And... It works fine!
Until now, I chose to omit one important detail that might have given away the issue to the more knowledgeable right away. Our webservers have the URL /.well-known/acme-challenge/, used for ACME challenges, aliased somewhere else on the filesystem - To /tmp/challenges.
See the issue already?
Some *bleep* over at the Debian Package Maintainer group decided that Apache could save very sensitive data into /tmp, so, it would be for the best if they changed something that worked for decades, and enabled a SystemD service unit option "PrivateTmp" for the webserver, by default.
What it does is that, anytime a process started with this option enabled writes to /tmp/*, the call gets hijacked or something, and actually makes the write to a private /tmp/something/tmp/ directory, where something... Appeared as a completely random name, with the "apache2.service" glued at the end.
That was also the only reason why I managed fix this issue - On the umpteenth time of checking the directory structure, I noticed a "systemd-private-foobarbas-apache2.service-cookie42" directory there... That contained nothing but a "tmp" directory with 777 as its permission, owned by the process' user and group.
Overriding that unit file option finally fixed the issue completely.
I have just one question - Why? Why change something that worked for decades? I understand that, in case you save something into /tmp, it may be read by 3rd parties or programs, but I am of the opinion that, if you did that, its only and only your fault if you wrote sensitive data into the temporary directory.
And as far as I am aware, by default, Apache does not actually write anything even remotely sensitive into /tmp, so...
Why. WHY!
I wasted 4 hours of my life debugging this! Only to find out its just another SystemD-enabled "feature" now!
And as much as I love kidding on SystemD, this time, I see it more as a fault of the package maintainers, because... I found no default apache2/httpd service file in the apache repo mirror... So...8 -
A while back we had some time sensitive work I was doing in overtime, the work was purely functional and the front end had not yet been done. It went to QA to test the functionality and the only feedback I got was UX oriented.
I tried to explain on 3 occasions that the looks was not important in the slightest at this stage, and just try to break it. I then got a lecture that it wasn't an optimised layout and was shown the AA route finder as an example of how the tester thought it should look.1 -
Let's talk about the cargo cult of N-factor authentication. It's not some magic security dust you can just sprinkle onto your app "for security purposes".
I once had a client who had a client who I did server maintenance for. Every month I was scheduled to go to the site, stick my fingerprint in their scanner, which would then display my recorded face prominently on their screens, have my name and purpose verified by the contact person, and only then would the guards let me in.
HAHA no of course not. On top of all of that, they ask for a company ID and will not let me in without one.
Because after all, I can easily forge my face, fingerprints, on-site client contact, appointment, and approval. But printing out and laminating a company ID is impossible.
---
With apologies to my "first best friend" in High School, I've forgotten which of the dozens of canonicalisations of which of your nicknames I've put in as my answer to your security question. I've also forgotten if I actually listed you as my first best friend, or my dog - which would actually be more accurate - and actually which dog, as there are times in my High School life that there were more tails than humans in the house.
I have not forgotten these out of spite, but simply because I have also forgotten which of the dozen services of this prominent bullshit computer company I actually signed up for way back in college, which itself has been more than a decade ago. That I actually apparently already signed up for the service before actually eludes me, because in fact, I have no love for their myriad products.
What I have NOT forgotten is my "end of the universe"-grade password, or email, or full legal name and the ability to demonstrate a clear line of continuity of my identity from wherever that was to now.
Because of previous security screwups in the past, this prominent bullshit company has forced its users to activate its second, third, and Nth factors. A possibly decade-old security question; a phone number long lost; whatever - before you can use your account.
Note: not "view sensitive data" about the account, like full name, billing address, and contact info. Not "change settings" of the account, such as changing account info, email, etc. Apparently all those are the lowest tier of security meant to be protected by mere "end of the universe"-grade passwords and a second factor such as email, which itself is likely to be sold by a company that also cargo cults N-factor auth. For REAL hard info, let's ask the guy who we just showed the address to "What street he lived in" and a couple others.
Explaining this to the company's support hotline is an exercise in...
"It's for your security."
"It's not. You're just locking me out of my account. I can show you a government ID corroborating all the other account info."
"But we can't, for security."
"It's not security. Get me your boss."
...
"It's for security."8 -
I'm trying really hard not to be sensitive, but my manager is making it difficult with their "constructive criticisms" ...
Just finished up a call with them. And I'm so tired. I'm not even angry or upset, I just feel so tired of their bullshit.
I set up a meeting as a courtesy to get them up to date on all the code changes I made. Last night I stayed up late to try and get things in before the deadline and this morning just killed me when they say.
"I don't think I should have given you this."
"I was right, you weren't ready to start doing this."
(Then don't even bother giving me anymore tasks then, I don't fucking care.)
"you clearly don't understand how branches work"
(Absolutely fucking false, I fixed that shit and am very familiar with how to understand the structure of the fucking repo)
"you are rushing and I don't need you messing up the website"
(I'm being proactive you twat, not rushing, making it very difficult for me to do the work and being productive)
Like seriously bro! Don't fucking patronize me for the work I was trying to get out. And trust me this fucking meeting is done in order to get ahead of potential issues, not a time to be condescending of my skills or lack there-of as you seem to so keenly think.
If you had this much doubt about my abilities then why give me the fucking Sr. title? Fucking trust that I'm being honest, and I'm trying to get us to a good spot, not fucking sabotage the company. God fucking damn.6 -
One of our customers wants our mobile app to log out the user after 15 minutes of inactivity because of SeCuRiTy…
Why? The phones protect the apps with their hardware encryption from any malicious access.
And we are not dealing with super sensitive data here like some banking app or so.
Why do some people want to have bad UX for no reason?12 -
When you’re use to dark theme and the lights in your car are too bright, you black electrical tape all the things...
I’m either more sensitive to light, or I’ve adapted to dark theme-ing all the things.20 -
Long time no rant.
Rant::beginRant();
How do people who are, I think, supposed to have a knowledge of what the fuck they're doing, keep their work without knowing what the fuck they're doing?
You're telling me that you have been hired as a "full-stack developer", yet you can't build a motherfucking Vue page over SSH (not even talking about automated deployment, just the most bare bones approach)? You don't know how to deploy a Laravel project? You don't know that Linux server paths are case sensitive? You can't read the log files?!
Rant::commitRant();10 -
Speaking of.. What in your opinion would be an appropriate way to warn someone about security problems, like db passwords in git?
I once came across dozens of extremely sensitive services' infra accesses: alibaba/aliexpress, natuonal observatories, gov institutions, telecomms, etc. I had dozens [if not hundreds] routers' and firewalls' credentials along with addresses. I tried one to confirm validity - it worked. I wanted to warn them but did not want to get in trouble.
If it were servers, I'd set a motd or append some warning messages in .profile. But not sure how to do it for non-server devices
what would you do? How would you warn them?
P.S. Deleting that record was a smart move, buddy ;)
p.P.S. Sorry, wrong category... Can't edit now :(6 -
Do you know what angers me more than anything else ?
Wasted potential. Thats what. That there are people out there that look at their bank account and see a large number and spend large amounts of time finding ways to push people down during sensitive times where they could be learning and growing and have the right attitude and energy to do so, just because it makes their horrible selves feel secure knowing how 'superior' daddy made them, not to mention likely factories filled with half naked Chinese kids sewing shoes and soccer balls and separating out precious metals with blow torches.
I cannot help but think about this again as I'm frustrated that I had to relearn something just now which created more questions which I once everything is dashed to pieces again I won't think to or know to look into, if the information even exists, all so some easily duped younger people can form the next generation of well... us, and fall for the same tricks while I feel like I'm falling behind.4 -
Having to rely on individuals who frequently use the words "thing" or "thingy" to convey important time sensitive information.
Nothing is more infuriating.8 -
Ah transports
Minding my own business in a crowded train, listening to full blast music. As the song changes I sort of heard an announcement but didn't get the subject.
Guy in front of me does a 180° and starts talking to me. I thought he wanted some guidance, so I removed my headset and never did I regret more doing that, that guy just went on and on about his life and stuff that I don't care about, until he got off his stop. Ironically, before he left off he said "you know my mama always told me that you should ignore people you're not interested in" (Forest Gump Swiss edition? He didn't have a box of chocolates though)
I was like "yes, fuck off, not interested in your bullshit", but well, noticed he might be sensitive.
After he left some teens just came and pretended I didn't exist as they invaded my corporal space. Pushed one gently as he was leaning on to me a bit too much.
People must see me as a help point, you know those terminals where you can browse stuff... That's me. The Father of them all.2 -
I've written a rant that was too long to devRant, so I made it into a medium article instead. You can read it here:
https://medium.com/bambuu/...
In short, it's about Apple's weird legal practices when it comes to Apple Developer accounts.
tl;dr
- Apple has "obvious" security reasons that requires a copy of a photo id, and you aren't allowed to conceal sensitive information
- Apple's favorite form of communication is fax and snail mail
- Apple needs multiple signatures and court documents to just change your account name. -
So today I found a file share containing some super super sensitive information accessible to what I think was our entire user base (6,500 users) if you knew the server name and had an interest in nosing around.
I reported it to our head of IT and heard nothing after, although 5 mins after reporting I could no longer access...
I suspect the infrastructure lead is going to be a dick (because his one of them awkward non team player kind of guys) and not thank me for preventing our company from being in national news papers... but try to spin it on why am I nosing around his servers in the first place..
I actually feel 50/50 about if I should of told or not.. but on flip side, I guess the access logs of me listing the files as I flick through to confirm my suspicions would of caused s bigger headache.
Fucking useless infrastructure engineers!9 -
I often read articles describing developer epiphanies, where they realized, that it was not Eclipse at fault for a bad coding experience, but rather their lack of knowledge and lack of IDE optimization.
No. Just NO.
Eclipse is just horrendous garbage, nothing else. Here are some examples, where you can optimize Eclipse and your workflow all you like and still Eclipse demonstrates how bad of an IDE it is:
- There is a compilation error in the codebase. Eclipse knows this, as it marks the error. Yet in the Problems tab there is absolutely nothing. Not even after clean. Sometimes it logs errors in the problems tab, sometimes t doesn't. Why? Only the lord knows.
- Apart from the fact that navigating multiple Eclipse windows is plain laughable - why is it that to this day eclipse cannot properly manage windows on multi-desktop setups, e.g. via workspace settings? Example: Use 3 monitors, maximize Eclipse windows of one Eclipse instance on all three. Minimize. Then maximize. The windows are no longer maximized, but spread somehow over the monitors. After reboot it is even more laughable. Windows will be just randomly scrabled and stacked on top of each other. But the fact alone that you cannot navigate individual windows of one instance.. is this 2003?
- When you use a window with e.g. class code on a second monitor and your primary Eclipse window is on the first monitor, then some shortcuts won't trigger. E.g. attempting to select, then run a specific configuration via ALT+R, N, select via arrows, ALT+R won't work. Eclipse cannot deal with ALT+R, as it won't be able to focus the window, where the context menus are. One may think, this has to do with Eclipse requiring specific perspectives for specific shortcuts, as shortcuts are associated with perspectives - but no. Because the perspective for both windows is the same, namely Java. It is just that even though Shortcuts in Eclipse are perspective-bound, but they are also context-sensitive, meaning they require specific IDE inputs to work, regarldless of their perspective settings. Is that not provided, then the shortcut will do absolutely nothing and Eclipse won't tell you why.
- The fact alone that shortcut-workarounds are required to terminate launches, even though there is a button mapping this very functionality. Yes this is the only aspect in this list, where optimizing and adjusting the IDE solves the problem, because I can bind a shortcut for launch selection and then can reliably select ant trigger CTRL+F2. Despite that, how I need to first customize shortcuts and bind one that was not specified prior, just to achieve this most basic functionality - teminating a launch - is beyond me.
Eclipse is just overengineered and horrendous garbage. One could think it is being developed by people using Windows XP and a single 1024x768 desktop, as there is NO WAY these issues don't become apparent when regularily working with the IDE.9 -
Have you ever had the moment when you were left speechless because a software system was so fucked up and you just sat there and didn't know how to grasp it? I've seen some pretty bad code, products and services but yesterday I got to the next level.
A little background: I live in Europe and we have GDPR so we are required by law to protect our customer data. We need quite a bit to fulfill our services and it is stored in our ERP system which is developed by another company.
My job is to develop services that interact with that system and they provided me with a REST service to achieve that. Since I know how sensitive that data is, I took extra good care of how I processed the data, stored secrets and so on.
Yesterday, when I was developing a new feature, my first WTF moment happened: I was able to see the passwords of every user - in CLEAR TEXT!!
I sat there and was just shocked: We trust you with our most valuable data and you can't even hash our fuckn passwords?
But that was not the end: After I grabbed a coffee and digested what I just saw, I continued to think: OK, I'm logged in with my user and I have pretty massive rights to the system. Since I now knew all the passwords of my colleagues, I could just try it with a different account and see if that works out too.
I found a nice user "test" (guess the password), logged on to the service and tried the same query again. With the same result. You can guess how mad I was - I immediately changed my password to a pretty hard.
And it didn't even end there because obviously user "test" also had full write access to the system and was probably very happy when I made him admin before deleting him on his own credentials.
It never happened to me - I just sat there and didn't know if I should laugh or cry, I even had a small existential crisis because why the fuck do I put any effort in it when the people who are supposed to put a lot of effort in it don't give a shit?
It took them half a day to fix the security issues but now I have 0 trust in the company and the people working for it.
So why - if it only takes you half a day to do the job you are supposed (and requires by law) to do - would you just not do it? Because I was already mildly annoyed of your 2+ months delay at the initial setup (and had to break my own promises to my boss)?
By sharing this story, I want to encourage everyone to have a little thought on the consequences that bad software can have on your company, your customers and your fellow devs who have to use your services.
I'm not a security guy but I guess every developer should have a basic understanding of security, especially in a GDPR area.2 -
TLDR;
How much do you earn for your skill set in your country vs your cost of living?
BONUS;
See how much I & others earn.
Recently I became aware of just how massive the gap in developers earnings are between countries. I'd love to calculate a fixed score for income vs cost of living.
I know this stuff is sensitive to some so if you prefer just post your score (avg income p/m after tax / cost of living).
I'm not shy so I'll go first:
MY RATES
Normal Rate (Long term): $23
Consulting / Short term: $30-$74
Pen Test: $1500 once off.
Pen Test Fixes: consulting rate.
Simple work/websites: min $400+
Family & Friends: Dev friends are usually free (when mutually beneficial). Family and others can fuck off, even if they can pay (I pass their info to dev friends with fair warning).
GENERAL INFO
Experience: 9 years
Country: South Africa
Developer rareness in country: Very Rare (+-90 job openings per job seeker).
Middle class wage in country: $1550 p/m (can afford a new car, decent apartment & some luxuries like beer/eating out).
Employment type: Permanent though I can and do freelance occasionally.
Client Locality: Mostly local.
Developer Type: Web Developer (True web dev - I do anything web related from custom HTTP servers to sockets, services, advanced browser api's, apps & more).
STACKS / SKILLSETS
I'M PROFICIENT IN:
python, JavaScript, ASP classic, bash, php, html, css, sql, msql, elastic search, REST, SOAP, DOM, IIS, apache
I DABBLE WITH:
ASP.net, C++, ruby, GO, nginx, tesseract
MY SPECIALTIES:
application architecture, automation, integrations, db's, real time data, advanced browser apps/extensions (webRTC, canvas etc).
SUMMARY
Avg income p/m after tax: $2250
Cost of living (car+rent+food): $1200
Score: 1.85
*Note: For integrity when calculating my cost of living I excluded debt repayments and only kept my necessities which are transport, food & shelter.
I really hope you guy's post your results, it would be great to get an idea of which is really the worst / best country to be a developer in.20 -
I was waiting for my wife in the shopping centre and noticed a shop sellung e-scooters. My my, what monsters can you buy with a few k€ :o I'm genuinely surprised!
The baddest monster: 3k: dual-notor, can carry >150kg of your fat ass. Takes ~12hours to charge, but, read this: with a single charge you can travel 150km! Max speed is 90km/h
i mean... I'm feeling quite confident riding a motorcycle at that speed, because I can bend down, because it weights a few hundred kilos and is not that sensitive to wind and road bumps.
But riding standing at that speed... Without any cover, with a vehicle weighting 50kg,.. Would you?15 -
One of our projects migrated their file-repository to another one during a major release.
Instead of giving this task to an experienced programmer, they gave it to the head of the respective dev department due to the usual release panic.
Soo.... He wrote the migration tool. It was executed during the release. Everything seemed fine so far.
A few days later. Someone from the above project came to my team due to some "strange behaviour on the production database".
They reported that they couldn't download some of the user's documents due to unknown reasons.
After quickly analyzing the current state of the new file-repository, we concluded that the affected documents did not exist in the new repository.
Then we took a look at the so called migration tool...
Well.. After nearly 30 min. we knew the root cause for that.
They only migrated the first 4 levels of the folder structure. Due to the assumption that "we don't use deeper nesting". (Facepalm)
As the head of their department wrote it, no one seems to questioned it either. Nor did they made a code review and ended up with a tool with hard coded urls to the production db, no version control, no build tool, no ci, nothing. Breaking nearly every possible company standard.
However.. That's not it. When analyzing their migration tool we noticed another even more dangerous thing.
They mixed up the id generation of the migrated documents resulting in a random assignment between customers and documents. Which is quite bad as this contains sensitive information. E.g. passports
They offered us quite a nice amount of money to fix this until EOB. We declinded as it was simply not possible in that time, but agreed to support them with the new tool.
After some time I heard that they migrated production again. And they fucked it up again. They never talked to us after we offered them support...
The third and final migration was written by us. Not only migrated it correctly. It was also way faster. By factor 20.
In the end we haven't gained anything from this rushed project as the penalties were piling up due to this fucked up migration.
After all this time I'm not sure who is to blame. In my opinion, partly all of them.
Head of department who can't and shouldn't code.
Seniors who didn't review the code and didn't ask for help.
Release mgmt who put way too much pressure on the devs. -
When Amazon asks if my email address is all lower case... The desire to make it an informative moment that email addresses are not case sensitive is outweighed by my desire to resolve my issue as fast as possible.1
-
A conversation between an offshore developer and his manager at a fortune 500:
I'm a software developer and the company I work for is a vendor for $manager's and $offshore_dev's company. They provide endless hours of entertainment/terror. Recently, we've been trying to convince them that they need to stop sending sensitive information plaintext over HTTP and set up TLS/HTTPS which has led to tons of fun conversations such as this one they had during a conference call:
* $manager: "Did $offshore_dev implement TLS1.2?"
* $offshore_dev: "Yes, we enabled a parameter in the code to enable TLS1.2 in the code but according to $me's email, this requires HTTPS in order to work."
* $manager: "No this works, we're using TLS in $other_application right now."
* $offshore_dev: "Well, $manager, it's implemented but it currently doesn't encrypt anything as such."
* $manager: "Okay, HTTPS is in the roadmap in the next quarter, we can move forward without this for now."4 -
!rant
I was playing with adb logcat some apps and I saw some sensitive info from my bank app. So I decided to go deeper , I saw my entire banking information , WHAT THE FUCK? I feel unsafe now using this bank.
Btw this bank is using react native and forgot to obscured their code in production 6
6 -
Ibwish I had remembered this when the weekly theme was office pranks.
In the first or second year of high school we covered basic internet security. Stuff like don't follow suspicious urls, don't open suspicious emails and such.
Our teacher let us play around with some sort of simulated desktop environment, where we could execute some hacks like ad popups and such on each other's environment, if we fell for the trap.
Anyways, one hack I found interesting was a hack, that lockes a user out of their virual desktop, until he enters a password, that will be displayed on his environment.
Yes, a very interesting hack, because it contains two obvious yet major design flaws, which I could exploit 😈
1. It's case sensitive
In itself not a problem, but combined with #2, it's fatal.
2. "IlIlllIlI"
Depending on your font, you probably have no idea what exactly I just typed.
Let's just say, the font displayed uppercase i and lowercase L completely undifferentiable.
Guess whom I let suffer.
It was our teacher, who had to demonstrate us some things and who was connected to the same network.
I swear, nothing beats that feeling when your tearcher has go come to you and embarrassingly ask you to "unhack" them, because they can't type it 😂1 -
This is my #wk110 about a project from when I was a real n00b. It can also be read as a rant about myself.
So I decided to code my own terminal based password manager. Because, you know, whom can you trust the most; yourself or some random password manager from the internet?
Obviously, encryption plays a major role when storing such sensitive information. So n00b me decided to go with Base64.
Base64.
I developed a password manager that stores your passwords in Base64 format.
What must I have thought?!
Perhaps the gibberish looks of Base64 encoded data made me think that this actually is encryption.
After having realized my stupidity, I quickly replaced Base64 with AES and more recently I completely rewrote the whole project which is now also available on gitlab: https://gitlab.com/bitteruhe/sesame
This act of stupidity still embarrasses me every time whenever I think about it, though. -
Very eventful day, please see enclosed several smaller rants.
===================
My college's systems are shit and not only do they use HTTP for everything, even the stores and financial aid purchase system, they have homebrew JS shit for PGP site encryption (nifty...), but they exchange the PRIVATE KEYS instead of the public keys. Over HTTP. Not even HTTPS. Also if you log in more than 10 times in 24 hours it's supposed to lock you out of your account until you call... except it locks EVERYONE out. Found this out when on campus, trying to get my textbooks, when suddenly everyone had login lockouts because i'm a "paranoid bastard" and "afraid of idiot college students" for not telling a PUBLIC PC to remember the one password (enforced by password auto-sync across all their shit, not ideal, no) guarding my SUPER-SENSITIVE FINANCIAL AND ACADEMIC DATA... among the other hundreds of issues this college has. I now see why this college is the only one I can afford...
===================
Can't pass-through raw DVD drive access to VMs as VM managers crash when I try (yes, even QEMU...) so i've gotta install Windows on a shitty 80GB laptop HDD for literally one quick project. On the bright side, if my theory proves correct, you'll no longer need modchips for PS2s.
===================
Found a couple odd lines in my xscreensaver config:
GetViewPortIsFullOfLies:False
nice: 10
pointerHysteresis: 10
the first 2 I can't seem to figure out what do, and the last taught me a new word. Fun!
===================
that's it, it's over, why are you still here11 -
I just remembered an annoying experience I once had,
Wanted to know cli version asap (due to some bug introduced in a certain version):
-v (output: view --help for command)
--version (output: view --help for command)
FUCK
--help (revealed: -version)
Wanted to know it's dependency version:
-version (output: view --help for command)
FUCK
--help (revealed: version)
You could call me lazy for not always typing --help first but there must be a standard for this time sensitive command.1 -
How it started:
Need to replace in a lot of SQL files certain stuff...
find . -type f -iname '*.sql' -exec sed -i 's|new|old|g' {} \;
12 hours later that find executed a shell script containing roughly 120 lines of text pipelining.
The jolly of inconsistent workflows.
Different SQL format stylings... Makes fun when single line string replace needs to be extended to multiline RegEx handling. Or matching SQL comment configuration..
Different line endings. MacOS, Windows, Unix, Bukkake.
Different charsets / collations. Anyone wants latin1_swedish_ci... utf8... utf16... :/
Realizing some people even left sensitive data inside the SQL files (e.g. API Tokens..... Yayyyyyyy).
...
Ugh. It's never a one liner. It's never easy. -.-
I hate cleaning up messy shit.3 -
Light Shot is the worst app and website ever .... No privacy
So I write a simple PHP script for Windows machine, to randomly generate integer and char for randomly open URL.
By running ```php run.php``` you able to see some sensitive information sometimes.
Refer https://github.com/johnmelodyme/...6 -
So new job started.
Just for context- old company was shit.
Promised the world but.
No benefits.
Terrible project management.
High pressure.
But green field interesting work (except by now it’s a few years in so it’s a ‘browning’ field but I was on it from the start).
New company first impressions..
Seems a fantastic company.
True to their word they have money for tools.
Making time for personal development.
Much bigger development community/department.
Seems like the term are under far less pressure so far at least.
But a MASSIVE amount of tech debt.
People seem to want to do the right thing and they’re making time to try and deal with it.
But one or two are very opinionated as to how to deal with it.
So this could go either way and only time will tell I guess.
Trying not to over analyse every little thing they say but I’m hyper sensitive to it at the minute while in the early days.
As always the real challenge in IT is the people not the tech. I count myself as part of the problem, sure I will form some opinions and sharing them too.3 -
I don't consider myself a guru in JavaScript (hell I studied theoretical chemistry), but I do hate much of the rationalization behind building a Jenga stack of libraries, frameworks, dependencies... for building everything web related.
Many of the problems I see people solving with these giant stacks could be easily solved understanding how websites work (html, css, js and how interact with each other) with no dependencies giving smaller (for end users at least) and more maintainable code (in the sense it would not require updating dependencies that may be discontinued...)
I do imagine situations where these are ideal... Since there are not absolutes and developing is very context sensitive, but man if I have js article fatigue for ridiculous scenarios.2 -
Just found out today via Reddit that Wells Fargo, American Express (not personally confirmed), and Chase login passwords are NOT case sensitive!
I would check your bank too!2 -
Never had a truly bad experience with a designer but once one mentioned offhand that the unique keys that we were using to secure access to sensitive information should be only 4 characters long because it looks better that way...
I kept them at 161 -
I love working on legacy products. You just need a good shower and possibly a therapist after.
- Sensitive data sent over the internet encrypted with DES (not even 3DES). Guess it doesn't matter that the key (singular, for the last decade) is basically 0123456789ABCDEF.
- Client databases with open default port, admin/admin superuser.
- Critical applications (potential for substantial property damage, maybe loss of life) with a single point of failure and without backup.
Suggestions, to slow down a bit with sales, so we have time to rewrite this steaming pile of crap are met with the excuse: be more pragmatist, this is standard industry practice.
Some of this shit can be fixed on my own time if my conscience nags too much, but others would require significant investment of time from multiple developers, which would slow down new business.
Guess the pay is ok, so that's something... -
I had to do a double take... Needless to say I can't sign in for shit, fucknows what mental finger dance I did on the shift key when signing up to these guys...
Also: forgotten password is "please type your email, if there's an account associated to this email address we'll fucking email it with password reset instructions"...
Fucking arsehole fucks, I just wanna pay my fucking energy bill.
-
when TS does its job and team mates complaining that TS is too sensitive!
it does its job you douche, now you do yours!4 -
I haven't said anything yet, but an AltRant notification server exists. Support for it will arrive very very soon on the AltRant app. It will run locally on the end user's personal computer, and it does not require a constant connection to the phone. Both devices need to be connected to the same local network on first connection, but after that you can wander out of your house or disconnect from the local network and still receive notifications.
DISCLAIMER: ALL SENSITIVE USER CREDENTIALS ARE NOT STORED *ANYWHERE* EXCEPT ON THE LOCAL USER'S MACHINE. NO DATA IS SENT TO ME. THE SERVER IS OPEN-SOURCE, HAS NO RELEASE BINARIES AND RUNS ON PYTHON.
Note to @dfox: if you want this to not exist or not be supported inside AltRant, please tell me or send me an email about it.2 -
”We’re not going to shuffle you (devs) around from project to project and definitely not taking on any new time-sensitive projects with the limited resources we have, seriously understaffed as we are atm” - that was the promise.
So today I got assigned to a time-sensitive project (unconditional deadline by the end of the year) on a product I am not at all familiar with... I almost believed 2 projects underway was enough so that it would not get assigned to me. Oh well, there’s always room for a 3rd.
At least I get to pick my tools so I get to try out Fable... a silver lining there, and not really a thin one.3 -
Worst part of coding lang I love?
C# being case-sensitive.
Not a C# language thing, but I hate the vilification and anti-coding standard of not 'allowing' prefixes. Interfaces are allowed (ex. IUpdateCustomer), why not classes? Why can't I have a DTO and declare it a TCustomer and the zealots not scream "HE'S USING HUNGARIAN NOTATION!!! TAKE HIM TO THE STAKE!!"?24 -
Has any of the women in here dealt with "too politically correct" in the office that it's awkward? My boss refuses to just say guys even though I told him I feel singled out when he adds "gal". Or that I can't be better at social skills bc that tends to be stressed more if you're a female; nope i need to find a different reason now. Or telling me how I need to be involved in women's rights movements, those women are actually doing something to make a difference. I mean I'm glad that he's trying to fight for equality, and I know it can be so much worse, but I feel like I'm being corrected on how I should be as a female. Any suggestions? Or am I just being sensitive?9
-
Print("Hello World")
When people design a brand new Postgresql schema (case sensitive) using a mix of upper and lower case letters.
Only to then proceed and escape every single table and column name in every single query.1 -
Open office plans are a GREAT idea. Nothing says productivity like hearing a pin drop from across the building. Who needs good acoustics anyways? And you bet your ass the moment anything sensitive to background noise is going on you're no longer allowed to communicate at all, because even a potato plugged into an audio jack can hear you whisper from 50 feet away. Good thing we don't do that often - only on days that end in Y, I assume.2
-
Coolest bug is less of a bug and more of a feature. I've been working on a medical app and I used an open source backend which had almost everything I needed. To be hipaa compliant you have to encrypt all sensitive data - full db encryption was not something this backend was capable of.
So my solution was to encrypt the data on the client side and create a secondary server - that can only be accessed on my app server - to store and retrieve the keys.
If anyone's thinking of working on a HIPAA project - you're welcome -
sAleSfoRce aPEx is a hot wet garbage fire. How can I make this actually make this work right when I need to compare case sensitive strings?
 10
10 -
It seems like sensitive websites that need more priority to work fine are the ones that do not. I'm talking about government, school, bank, & service provider sites. Or it's just my retarded country.9
-
This happens more often than I'd like to admit...
(repost since the other one contained sensitive information) 6
6 -
I can't come to terms with people's terrible reasonings.
You read a news about something. Let's assume it has to do with a sensitive topic, like race, gender, culture, religion, something polarizing, that makes you pick 1 of 2 sides.
So what do some people do? They ask themselves "ok what group do I adhere? How do I label myself?".
Then they ask "what do other people in said group/label think about the matter?", sometimes it's people in the media, friends,
sometimes people even create a mental construct of a stereotypical person of said group, a hypothetical one, and use the opinion of said construct as representative.
And final step is a knee jerk reaction of "I believe that too!!!!!!".
Obviously, all of this can't bring no one closer to the theorical truth or the least flawed conclusion.
What does? Case by case basis.
You judge every case as if every case was its own thing.
But why does some people have a hard time doing that? Just general ignorance maybe?
Maybe this tends to occur in families where parents don't teach their kids to challenge their beliefs, or teach them that doing so could result in lack of parental acceptance.
People also have peer pressure, the need to belong and feel accepted. That means sharing the same points of view with close people and considering the opposite taboo.
There's also the very ignorant people that have conspiracies for lunch.
In any case, I feel some people don't even fucking try to be neutral.4 -
document.getelementbyid("myid");
Runtime error !
must be "ById"
:/
also same problem with elem.innerHtml
(Correct: elem.innerHTML )2 -
So today i had to visit this banks site to do updation on a document but for some reason the modal dialogue that was supposed to open was not working and i couldn't continue to next step.
On an attempt to contact customer support, i browsed the site for relevant details. As i do that, i observed this site is so shitty that it can't even properly render on Google Chrome! It was an horrific experience finding info in that site.
Finally found the customer support form and as I clicked the "submit" it didn't give any feedback whether it was processing or not. After like over a minute of uncertainty, it got redirected to a 404 page.
Frustrated, I went on to their twitter and I almost tweeted calling out their terrible web developer team.
But, my instinct told me to calm my titties and i tweeted a regular confused user tweet.
Got their attention and few hrs later i got a phone call from someone working there. He didn't sound like a customer service representative from the way he spoke. He told it was an issue with their website and had fixed it. I tried again as he was on the line but it was not working for me. And then i shared screenshot of the issue. He tested it again and said it was working for them. Still not working for me. ( Probably cache issue on my end ). Thought he would suggest to clear cache and try. But he asked me to try on another computer since it was working for him.
As i searched for a another system, i got a call from customer support guy and he said he will do the update on their end and told me to tell details. Since the info was not that sensitive in nature, I went with it.
Pretty sure the other guy i talked to was a developer.
This made me think - had i tweeted out a mean tweet calling out their shitty website it would have been probably awkward talking to him - I'd have to be mean again. It could've ruined his day, maybe he was under pressure from his pm that he had to make the phone call. He probably hates his job already managing that shitty legacy code..
I don't know - either way, I'm glad i was able to keep myself calm and not be a source of negative energy. -
Pm orders me to integrate data from several closed systems into a new CRM, problem is... corporate security won't allow me to push data between these networks as there are extremely sensitive data on these systems. So I disobey PM or corporate if I do it and ive told both the issues. 4th round with this exact issue now.4
-
Been a mobile developer since April, liking the experience and the amount of projects that I've been a part of.
And one of the things that I've learned about this is that sometimes the client doesn't even know what he really wants. I mean for fucksakes, we implement everything, and new functionalities and there's always something that works on every other app (and is basically a standard) and he thinks is not suppose to be like that...
And another thing. Fuck Apple Store. At the company we've developed an app that practically shows information that only users should see (in our logic is sensitive information from our clients) and they DECLINED 4 FUCKING TIMES THE APP. Reason? Since the app's purpose "isn't correlated" with the basical information we show, the user can navigate through the app without going through login.
We basically added an "explore option" that shows basically nothing and they've accepted. FUCK APPLE FOR WAISTING OUR TIME AND THE CLIENTS TIME1 -
Sometimes when I drink water out of a glass bottle I knock the edge of it against my overly sensitive front teeth just to feel something once again.9
-
Trying to implement a dynamic data masking solution for our databases, to filter out sensitive data.
This seems like a problem which should've been solved decades ago. But it isn't. All DDMs, proxies, seeders, maskers... they all suck balls.
Which makes me wonder, how many devs walk around with MacBooks with half a million credit card numbers on them... -
Dear programming languages,
If you had to be case sensitive, then why the fuck can't you settle on whether to use an S or an s for a
S/string declaration.4 -
Imagine an online, public service, that allows you to communicate with others (for example a simple chat, game, whatever ).
The users connect to each others via p2p. Based on this, you can easily get the ip address of any user directly connected to you. P2p is used to reduce server load, but information is still verified (for example using RACS), so let's assume the data is always safe.
(please remember, this is just a imagined Szenario)
Now the question: AFAIK, the IP address is a sensitive information. Would p2p in this scenario still be 'legal' in the EU given the latest changes in the laws?7 -
Why do we rant here? Why can’t companies allow a safe space for their employees to vent out their woes? Or does that just add tension/make the workplace heated coz managers or co-workers could be sensitive to criticism? Or we’re just too stressed and overwhelmed that our woes don’t make sense(and we know it) but we gotta let it out some times? Lol16
-
Me: uses MS Edge with Strict tracking prevention
Every website: "Please disable AdBlock"
Why are you so fricken sensitive?
I need to get an anti-anti-adblock.3 -
21:37
Manager: Hi
Manager: Do you know anything about this? <screenshot.jpg>
Me: Hi
Manager: Oh, I didn't mean to disturb you this late
Me: *what....? Then what DID you mean by writing to me at my bedtime....?*
(Though it's good he pinged me - it was a valid and time-sensitive concern. But saying "I didn't mean to" - that's just not true. Call a spade a spade and spit out what you need)10 -
Bought an Arduino and is finally able to learn how to make my software interact with custom hardware projects. Just wiring up a led and controlling it with software is amazing fun! Really looking forward to learning servos, motors etc.
Planning to make velocity sensitive midi drums with piezos in the future.4 -
Sometimes, I feel like tearing my hair out from the way Bash works.
Like... Where other languages have two operators for case-sensitive and insensitive regex matching, bash? It doesn't. It only matches case-sensitively.
And if one wants the insensitive matching? Gotta set a shell option... And if a script wouldn't change it back, who knows what else could break, so of course it has to save its initial state, change it, do its case-insensitive matching, and return it back to its original value.
10/10 experience.14 -
I just got a project that is already developed by a team. It is already in the production and guess what!! They are storing customer’s credit card details in the database 🥸🥸12
-
Dude that convinced me to come to company became the most toxic person ever after I got fed up of his lies and lame attempts to get me to do his job (so he could just get the merits). We don’t work on the same project but closely related. Every time we speak he tries to hurt me by trying to put me down/raising sensitive topics. But he gets rid of the history all the time, so I have nothing to handle to HR or manager. Time to jump the ship? Job is fine otherwise.6
-
To all websites requiring at least one upper case, one lower case, one number, one special character, 25 emoji and 49 unicorns in the password when signing up.
If you say something is required, then your regex BETTER be checking ONLY for those things. You should not have hidden requirements for passwords that users are supposed to dream about and know. Especially if it's a super time-sensitive thing that they should have opened 2 Fridays ago.
I had to pull my hair out for 20 minutes (that felt like an hour) before looking at their code and reading their regex. The regex was different from what the page said the requirements actually were. What were they even thinking? 😑
The rest of everything related to this organization uses an SSO system, why can't they just use it? Isn't the whole point of SSO to avoid a different login for every tiny part of the system?
I wonder what the other less technically inclined people using the system are doing right now. Sadly, I have no way of letting them know.
I sincerely hope the dev that made that website faces the same thing while picking a password for creating an account somewhere else and realizes what he/she did.
I really needed to let it out.
I feel much better now.
Time to take out the stress ball :)1 -
Reading "duh... that link looks sketchy" time after time when attempting to nudge people in the direction of good resources, e.g., on-line manual pages, becomes rather irritating. Is typing the URL into VirusTotal or something really such a fucking hassle? Are you sufficiently special to warrant the creation of an IP grabber which is dedicated to targeting you... AFTER you posted your exact location on Instagram last week?
Similarly, some pants-shitting, worm-eating troglodytes who have the gall to claim to know anything about cybersecurity STILL think that for all Web sites k, that k's URL begins with "https" implies that k is secure. NO! Unencrypted Web sites are FINE unless sensitive information is being transferred. Are publicly available manual pages sensitive information now?
Grabbing the campaign hat and writing death threats and very personal insults is sometimes slightly tempting.5 -
Talking about stupidity, my friend on whatsapp even share his bank online transaction on his stories, I told him to be careful with those sensitive information, but he's ignoring it.
I think he more care to show off his "bulge-wallet" than protect his own money.
Find anything stupid than that?9 -
In today's episode of "how i got almost to the point of insanity for hours and the sudden realization and relief"
When you have ssh error saying your private key is an invalid format in your CI, you probably just missed an EOL.
MCP says EOL.
Fucking EOL
That is the realization i made after half a day wasting on debugging this.4 -
Wouldn't call it a feature. More like worst practice. Data manager (and my boss at the time) kept using our website as a way to host large files 3rd party vendors/partners could download instead of using one of the many secure transfer methods out there to send them data. This was sometimes extremely sensitive data. No authentication or security that I could find. I went ballistic on him after seeing that.
-
Why fucking windows explorer's search is fucking case-sensitive? I could not find any fucking option for it.
Edit : actually it's not but sometimes it couldnot find files2 -
Hey folks!
! Do not read further or open this rant if you are likely to be offended!
I always wanted to know but had no nice way to ask so I'm just gonna shoot.
Most of you must have worked/be working with foreign people: canadians, french, chinese, etc. How would you describe those people as colleagues [e.g. lazy, stubborn, chatty, etc.]? The goods and the bads would be perfect.
The topic is sensitive. Please be polite but sincere. This question nor its answers are not meant to offend anyone. We all have our cultural differences, we all have been taught different. I'm just wondering what could I or anyone else expect from each foreign teammate.15 -
Sticks and stones may break your bones but I sometimes have that feeling of breaking every bone of those who push changes with sensitive information to the repo. Stop it.1
-
Maybe I am just sensitive.. but sometimes I feel that my new manager is being a little harsh on me.
Again, he might behave the same with everyone and I am assuming that it's just me.
1.5 months in the new job and not a single good comment/feedback I recieved from him. It's not that he criticises me or my work, or calls me a dumbass.
But whenever I submit anything for review, I get a ton of feedback where he expects everything to extreme precision.
He guides me, explains me post my failure, and has specific pointers of what he wants/how he wants things.
But all I am given is a set of documents to read initially with an expectation that I have to figure things out. When I am not upto the mark, he then guides me.
Why I worry?
1. I am on probation and this place is a start-up, don't want to get fired.
2. They got me as a Sr PM (which was also my previous role where I excelled), so I fear that expectations would be high from me. Failing to deliver those might get me in trouble.
3. He isn't a micro manager and quite supportive, but his communication style isn't working for me (so far).
Somehow, as always, I am getting along well with everyone in the org and everyone is talking good about me.
But with my immediate boss, the imposter syndrome kicks in real hard and I am super insecure. Every time I have to interact with him, I get super stressed and anxious.
I know things take time, but given that I am a Sr PM (and my boss expects me to be a lead PM, a position higher than current), I feel if the expectations are not delivered then I might get fucked.5 -
Nothing much here, keep scrolling...
I think my manager does not like me. I might sound like a broken record because I keep asking feedback at the end of every call (which is every other day).
I genuinely want to make her proud of the decision to hire me and want to learn for which I am willing to work smarter/harder.
What I feel is that they find me annoying. They seem to be happy with my work but guess my Indian roots of typical behaviour are showing up.
My co-worker evidently isn't confident to lead on her own and keeps me looped in to all her tasks which I am fine with. Though, I feel that I might be overstepping in her zone and manager doesn't want me to do that.
I may not be perfect and also a very sensitive guy, but I am trying hard.
Maybe they have plans to get someone else to lead and just keep me as a pawn on the board.
I don't think it is the imposter syndrome this time and surely the teams in this org are working in silos with very little communication within or outside their direct teams which kind of makes it even more difficult for me to operate.
However, as always, I have enough free time in here to resume my side project, learn another hobby, or learn new skills. Or is it just that I am assigned less task or underperforming?
Sometimes things are very confusing and one can never find an answer.
What's the best thing to do in such a situation?7 -
Does anybody use Freelancer.com? I'm currently in an argument with their support chat minion about how private or not-private the project's contents are AFTER the project is awarded. She's telling me that both awarded and unawarded projects are completely exposed to the public Internet, sensitive file attachments, chats, everything, unless one upgrades to Private status. If one doesn't like that, she says, one can always delete one's project for only $5. Does anyone else have experience to share in this regard? I find this incredible.2
-
Currently wondering why we use RGB when the "red" cones in the human eye are most sensitive to yellow light
 3
3 -
So my computer is doing ok after becoming spastic over viruses. I did hardware and software cleaning. First time I did removing hardware parts but it worked it way better than expected with the static sensitive parts (I used a anti static wrist band). Congrats to myself I guess :)3
-
Since day 0, I have been fond of computers. One of my first plush was called "DataDog" and looked like a CRT screen with dog ears around. According to my mum I was "addicted" to it.
At year 2, my dad was arranging some music on some software while I was watching him on his lap. Quick jump to the present: nowadays and since 10 years I run my own home studio with three guitars, two keyboards, one bass, three monitors, a microphone, an amp and a cabinet... coincidence? I think not!
Fast forward 5 years later (so I'm 6-7 years old), and I was playing with the legendary pinball game on Win95, as well as Flight Simulator. Then I was hogging mum's laptop to play settlers II (<3 that game), I eventually got my computer, and got into Quake III Arena being aged 10 (and had to tell my mum that game was safe for my age haha - I eventually removed the blood effects).
The Quake 3 Arena chapter is interesting: it got me into router configuration as I wanted to open a port through the router to host my own dedicated games with friends, it got me into DNS configuration (I was running a no-DNS client that allowed friends to join me through a DNS while having a dynamic IP) and eventually... to modifying .cfg files to tune my server as I wanted it. No programming here but a nice intro into :)
Then I hated the fact everybody would point their finger at me and say "geek" - I was only 13, fragile, sensitive, and I wanted everything but a bad image on me.
Meanwhile I continued on getting interested in hardware and configure my own computers, and investing myself into music production.
Then, university. "What do you want to study?" I thought of everything but IT, fleeing the image of a "geek". Turns out it was a waste of time, and at 21 yo I got into web development (well, just html and css), then learned a bit of PHP, finally got a specialized 2-year training and now here I am!
I was bound to be in IT either way since day 0, and funny fact, I've used every windows edition since Win95. -
Can someone example to me why do people use a VPN when not on public wifi? Like you are already at home with your own private network.
Like the moment you log into Facebook or Twitter or medium or to check your Gmail/outlook whatever, all you are doing is making is making it very clear to the host companies that you are inconsistently paranoid. Because all the sudden the person who's home address is in Seattle, work and home phone are in Seattle and all of their communication is done with people in Seattle. Has their web traffic location encrypted unknown.
Yeah your packets might be encrypted, but you are still spreading enough self identifying information by merely existing on the web.
At the end of day it seems more like a illusion of safety that these VPN sell. At the cost of a good dollar and slower internet speeds.
Unless you got some actual trade secrets and sensitive information, the f is the point for you to use one?17 -
Anybody else really annoyed at all these people getting mad at zuckerburg? Like, I've always questioned privacy of the internet in general. If you're dumb enough to put sensitive info on the internet (especially on social media) then you shouldn't have the right to complain about privacy. It's your responsibility to protect your information.4
-
Fun fact: if your tweet contains the word “Mastodon”, it will be automatically marked as sensitive content.
https://mas.to/@TimH/...13 -
Adding a couple functions to free software, rebranding, then selling to customers.
I know that there are other companies that do this, but still feels like stealing from the authors and ripping off customers at the same time.
Maybe I am too sensitive, but I'm deeply disturbed by this and I'm having a really hard time getting work done.5 -
Google researchers have exposed details of multiple security flaws in Safari web browser that allowed user's browsing behavior to be tracked.
According to a report : The flaws which were found in an anti-tracking feature known as Intelligent Tracking Prevention, were first disclosed by Google to Apple in August last year. In a published paper, researchers in Google's cloud team have identified five different types of attacks that could have resulted from the vulnerabilities, allowing third parties to obtain "sensitive private information about the user's browsing habits."
Apple rolled out Intelligent Tracking Prevention in 2017, with the specific aim of protecting Safari browser users from being tracked around the web by advertisers and other third-party cookies.2 -
Once I found out an unprotected folder in my school which is used to store sensitive data.
It was open to any administrator there.
We copied the Question Papers, Edited the attendance, and Even changed the Marks.
We were able to extract photos of students from the database and retrieve stored passwords -
I was pissed off beyond all reason yesterday when I realised that the reason my code didnt work for 2 days was because i spelled eForm with an uppercase F in my data model, and a lowercase f in my object classes. There was no way for the compiler to warn me so everything compiled fine but crashed at runtime when I tried to access that property. When I saw it, my head hit the desk....
-
yahoo is now alleged to give away bulk mail content to intel agencies. such a dead investment, who uses yahoo for sensitive communications anyway?
http://thehackernews.com/2016/10/...1 -
How do you share some feedback about certain things to your peers?
A little context.
Within our team, me and another person are two senior folks and we are the ones who are answering all the queries to external teams, product, issues, incidents. Obviously we are seniors so we tend to lead by example and try to handle as much as we can. But this is giving the junior folks a nice getaway to not pitch in and scale and handle things as well. They are happy to sit back and when me or the other senior person is not available, their response to all the queries is that we dont know because we havent worked on it and then when we come back, we respond to those.
Also for the work, what usually should take 1-2 days, takes 3-5 days for these guys. 3-5 days of work gets delivered by them in 2-3 weeks. And the reason again, this is new, i didnt not get this and i have facing this issue. In all of this, our lead is quite laid back as well and doesnt inquire more about why things are constant getting delayed from their side.
The side effect of this has been that more critical and time sensitive things gets pushed to us senior folks even more and we are seriously getting bogged down by the amount of work.
We want to question and point out to these junior folks that they need to scale up, but we feel a little helpless since it might make them more hostile and retaliate. Why are we saying these when our lead is not saying anything. That will be their argument. Plus it will create an unpleasant working environment which we dont want either.
We think of talking to our lead, but again, I am not sure if that would be considered as bitching about them.4 -
Remember how I was - against all that was promised - assigned to a time-sensitive front-end (so definitely not my forté) project about a month ago? Remember how I struggled with the choices of how to go about it - switching from F# (Fable) to Rust (Yew) to eventually settling in with Vue and TS?
Yeah, I’m glad I went that way, even though there could’ve probably been better choices out there: my part is done now, even though it’s not quite prod ready yet (close tho), the team who’ll maintain it takes it over now, after I finish dealing with my current minor issue. And damn their front-end guy is GOOD. Makes me feel very inferior in that department. Well, I am. Back to back-end, thank you very much...
But I have an issue here, that bothers me. I’ve produced a codebase that’s obviously written on a tight schedule: no tests, no documentation, a few embarrassing hacks/workarounds and so forth. I actually feel bad for leaving it out of my hands to them in such a state...1 -
HELP!!
I am starting a new contract to create a full stack web application with a medical company that will contain some sensitive data about their clients/patients.
I have been working as a salaried full-time employee for a medical software company, but I have been shielded from any sort of lawsuits from the client (worst case scenario, I'd get fired).
Do any of you have any advice on what I should do to protect myself in terms of LLC's, Insurances, etc?2 -
I need someone as a partner on this idea that I have. Preferably someone with UI/UX front-end experience along with security measures for secure file transfer and storage (involves sensitive documents). Comment if interested.1
-
My coworkers and I work in close quarters in a laboratory all day. We all get along well, and since we don’t have “offices” and often work together on things, we are a pretty close team.
We recently got a new member, Jill, who is 22, and this is her first job out of college. She lives at home with her parents, who are incredibly well-off, and has lived at home all through college. The rest of us are late 20’s to late 30’s. Jill is very nice but also very sensitive and somewhat immature, and I’m not sure if she’s just not 100% sure how to deal with people in professional settings yet or what’s going on, but almost everything that comes out of her mouth has to do with money, mainly how much money her family has. If it might offer some context, Jill and her family are not from the U.S., but have been here since Jill was a teenager.
I usually just kind of inwardly roll my eyes and change the subject, but with the holidays it’s gotten considerably worse and Jill is driving my team and me crazy. Some examples of things she has said just in the past week are: “My dad’s buying my mom a new car for Christmas!” “I’m going to buy my mom a Gucci Keychain for Christmas. It’s $225 dollars!” “I’m so excited, my mom is buying my puppy a Tiffany collar for Christmas!”
The thing that sent me over the edge was when a male coworker asked for ladies’ opinions on a very nice coat he was considering buying for his girlfriend. My opinion was something along the lines of “I like it, but I would go with the gray because white coats get dirty very easily, in my experience,” whereas Jill’s opinion was “It’s not even a name brand, you should go with either a North Face or a Michael Kors.”
I am honestly not sure if Jill knows there are people in the world who are not as well-off as her family is, and that people who aren’t as “fortunate” don’t want to hear these kinds of things every day. We are not paupers, but we are definitely not buying our dogs Tiffany collars. Is there a way that I can tell her to please stop talking about how rich her family is, without sounding jealous or mean, or causing a lot of friction on my team? Like I said, she’s a nice person, but money is a touchy subject in any capacity and I think this might hinder her professionally in the future, not to mention that we’re all sick of hearing about it!3 -
Alright so I'm in need of a little advice.
So I recently decided to go back and practice basic problem solving and from what I can tell now it's just me not used to JS like I am with python but I want to move on to bigger projects and other basic concepts (like manipulation of the DOM) and move away from basic problems.
But my concern is that I'll look at that list and only pick the ones that I feel I understand I can solve instead of the ones I cant. And theres a large list of them and I see that people are doing a lot of them while I'm just doing a few per page. And I'm afraid I'm just not good enough or stupid if I just ignore the basics and move on because the basics are there for you to figure out the easy stuff.
But I really just want to move on and I dont know when I need to. And last time I asked for advice I mentioned I have been programming for a few years, left out the normal accomplishments I've posted on here but I was just told since it's taking me this long I should just quit I tried to rebuttle but they kept telling me no that literally broke me and my confidence so now I'm sensitive to asking questions also fuck whoever that was.4 -
Either I am too sensitive with my name or I just can't stop laughing when someone keep misspelled my English name, "Michael" into "Micheal".
I know it doesn't sound like a big deal but... *eye-roll*
Anyway, I am still wondering that what wording or how does it take for them to accidentally typed from 'ae' into 'ea'..?
Super curious here.3 -
So with all this new political correct bullshit pandering to the extra sensitive snowflakes, what do we call a “blackout” from now on?9
-
The more years go by, the more people get sensitive and butthutt by everything around them. Can't swear in public nowadays because someone will get offended lmao.1
-
When someone calls me VincentNwonah and expects me to answer. but I'm a programmer and VincentNwonah is a different object from NwonahVincent. ;p
-
my oh my, its my bad, .. dont worry its my bad. you dont have to look at me like that. im sorry cos im asking you about wtf was wrong with code and asking you to fix it.. #case sensitive.
-
Working with external teams on this new project involving pretty sensitive stuff like bank transactions.
Talking about user flow and how to handle authentication, like 2-factor and stuff.
Newish guy on external team (though experienced) says they have a proposal.
Security Questions.
... like "What was you first car" security questions...
awkward silence in room...8 -
Currently the only 3rd party tokenization VSCode supports is a massive pile of RegEx. There's a whole discussion about how procedural tokenization could be supported without running extension code in the UI thread. The central argument against delegating this to an external worker is that if the reply doesn't arrive fast enough it might interfere with characters typed later.
1. Any computer that can run VSCode can execute somewhere in the order of a _billion_ instructions per second. To a program, the delay between keystrokes is an eternity. The only way to run out of time here is if either the dev isn't aware that the request is time sensitive, or the framework communicates to the OS that the task isn't urgent and an arbitrary amount of work is scheduled before it.
2. Chromium is the pinnacle of cybersecurity and its primary job is to sandbox untrusted user code. You don't need another thread to do it.
3. This use case fits squarely in the original design objectives of Webassembly.2 -
HFS, MacBooks standard file system is the answer to that every question asking "what if you don't design well/ how bad can it get."
How can a bloody file system not be case sensitive.
I know you want to be different from *nix
But there would have been better ways1 -
I sometimes forget all the other “console.log()”s and I log API responses and other sensitive junk, :/
-
Security issues I encountered:
- Passwords stored as plain text until last year.
- Sensitive data over http until last year.
- Webservice without user/pass authentication. -
Security experts have discovered hundreds of fake websites which are being used to spread dangerous malware for Android and Windows devices. A "vast" network of over 200 internet pages, which impersonate 27 brands such as household names like TikTok, PayPal and Snapchat, are being used to spread a vicious bug which can empty out bank accounts. These bogus websites feature the notorious ERMAC banking trojan which is capable of stealing sensitive login details for 467 online banking and cryptocurrency apps.9
-
Holy shit. Do NOT open a Wells Fargo banking account. On top of their ridiculous password limitations, your password is NOT CASE SENSITIVE. I tested. Caps lock, no caps, a mix, it doesn't matter.
More info on the password limitations at my other rant https://devrant.io/rants/905148/...3 -
nothing new, just another rant about php...
php, PHP, Php, whatever is written, wherever is piled, I hate this thing, in every stack.
stuff that works only according how php itself is compiled, globals superglobals and turbo-globals everywhere, == is not transitive, comparisons are non-deterministic, ?: is freaking left associative, utility functions that returns sometimes -1, sometimes null, sometimes are void, each with different style of usage and naming, lowercase/under_score/camelCase/PascalCase, numbers are 32bit on 32bit cpus and 64bit on 64bit cpus, a ton of silent failing stuff that doesn't warn you, references are actually aliases, nothing has a determined type except references, abuse of mega-global static vars and funcs, you can cast to int in a language where int doesn't even exists, 25236 ways to import/require/include for every different subcase, @ operator, :: parsed to T_PAAMAYIM_NEKUDOTAYIM for no reason in stack traces, you don't know who can throw stuff, fatal errors are sometimes catchable according to nobody knows, closed-over vars are passed as functions unless you use &, functions calls that don't match args signature don't fail, classes are not object and you can refer them only by string name, builtin underlying types cannot be wrapped, subclasses can't override parents' private methods, no overload for equality or ordering, -1 is a valid index for array and doesn't fail, funcs are not data nor objects when clojures instead are objects, there's no way to distinguish between a random string and a function 'reference', php.ini, documentation with comments and flame wars on the side, becomes case sensitive/insensitive according to the filesystem when line break instead is determined according to php.ini, it's freaking sloooooow...
enough. i'm tired of this crap.
it's almost weekend! 🍻1 -
CREA DDF (Canada Real state listings API) is what you get when government fucks with technology.
Holy shit! So f*cking inefficient to use it, test it and get data.
I get the protection behind sensitive data but fuck me if there is not a lot of waiting behind their fucking application process just to fetch some testing data.1 -
Part I think 3 of Mathematica fails.
So, I'm doing a plot. Initially, I hit the following error: "Value of option PlotRange -> {{3,19},{0,1.1}} is not All, Full, Automatic, a positive machine number, or an appropriate list of range specifications."
Me:Okay, let's change it to PlotRange -> Automatic, maybe I don't know what I'm doing.
Mathematica:"Value of option PlotRange -> Automatic is not All, Full, Automatic, a positive machine number, or an appropriate list of range specifications."
Me:Uh, what? Well then... Oh, please don't tell me it's because of a space in between.
Mathematica:"Value of option PlotRange -> Automatic is not All, Full, Automatic, a positive machine number, or an appropriate list of range specifications."
Me:Oooookay then, what's the problem?... oh wait, there's another space. Why is it that sensitive to whitespace though?
--------------------------------------------------------------------------
That fixed it. Then, when I tried to reproduce it, suddenly adding a space and reevaluating did not raise the error.6 -
Update 2: https://devrant.com/rants/5446637/...
Not saying that my boss is wrong, but the way he gives feedback and teach me is just awful. Just today, a new colleague told me that one of the ex-team member quit because of our boss.
Anyway, the activity I was working on, I nailed it.
In morning connect, boss specifically told what he was looking for and made me do a live task and gave feedback. That made me realised what he was looking for.
I spent the day completing the activity. When I showed him, his jaw dropped.
He tried to pick on few things, but failed to do so.
He loved the output. Praised me and my persistence. Finally, the history repeated itself, and I learnt more about communication.
Possibly my weakest point out of all, where I was failing in interviews and had to fix that. Now, I got some pointers and will work on it to excel futher.
Yes, things were stressful, but I came out to be stronger.4 -
does anyone have any experience with e-solutions recruitment company ? theyre asking for sensitive information about a position so it seems shady.3
-
Gah, I just received this Ubuntu 18.04 VM with 8 cores and 8 gigs of ram, and since it'll be a production server both serving public and "private" networks (yes, shout at me, but projects won't be about hosting sensitive information, I wouldn't put all that on one server), and I'm struggling between my options.
Docker, or not docker?
The server's main use is to host our growing blog and install Varnish, which will hog some ram after a while. I use Laradock for my dev projets, it's really easy to develop with it, but I am unsure if it fits a production environment with performance, security and traffic load in mind :(
I read Docker has stability issues (in 2016-2017), and can bring the machine down with it, I don't know if I should just install the software (nginx, apache, percona/mysql/maria) without "containerizing" it and go for it
I'm lost xD7 -
This is a repost of an original rant posted on a request for "Community Feedback" from Atlassian. You know, Atlassian? Those beloved people behind such products as :
• Thing I Love™
• Other Thing You Used One Time™
• Platform Often Mentioned in Suicide Notes, Probably™*
Now this rant was written in early 2022 while I was working in an Azure Cloud Engineer role that transformed into me being the company's main Sysadmin/Project Manager/Hiring Manager/Network Admin/Graphic Designer.
While trying to simultaneously put out over 9000 fires with one hand, and jangling keys in the face of the Owner/Arsonist with the other, I was also desperately implementing Jira Service Desk. Normally this wouldn't have been as much of a priority as it was, but the software our support team was using had gone past 15 years old, then past extended support, then the lone developer died, then it didn't work on Windows 10, then only functioned thanks to a dev cohort long past creating a keygen....which was now broken. So we needed a solution *now*.
The previous solution was shit of a different tier. The sight of it would make a walking talking anthropomorphised sentient puddle of dogshit (who both eats and produces further dookie derivatives) blush with embarrassment. The CD-ROM/Cereal Box this software came in probably listed features like "Stores Your Customer's First AND (or) Last Name!" or "Windows ME Downgrade Disk Included!" and "NEW: Less(-ish) Genocide(s)"!
Despite this, our brain/fearless leader decided this would be a great time to have me test, implement, deploy, and train everyone up on a new solution that would suck your toes, sound your shaft, and that he hadn't reminded me that I was a lazy sack enough lately.
One day, during preliminary user testing I received an email letting me know that the support team was having issues with a Customer's profile on our new support desk. Thanks to our Owner/Firestarter/Real World Micheal Scott being deep in his latest project (fixing our "All 5 devs quit in the last 12 months and I can't seem to hire any new ones" issue (by buying a ping pong table)), I had a bit of fortuitous time on my hands to investigate this issue. I had spent many hours of overtime working on this project, writing custom integrations and automations, so what I found out was crushing.
Below is the (digitally) physical manifestation of my rage after realising I would have to create / find / deal with a whole new method for support to manage customer contacts.
I'm linking to the original forum thread because you kind of need to have the pictures embedded in said reply to get really inhale the "Jira-Rant" ambiance. The part where I use several consecutive words as anchor links to tickets with other people screaming into the void gets a bit sweet n' savoury too - having those hyperlinks does improve the je ne say what of it all.
bit.ly/JIRANT (Case Sensitive)
--------------------------
There is some good news at the end of this brown n' squirty rainbow though!
Nice try silly little Jira button, you can't ruin *my* 2022!
• I was able to forget all about Jira a month later when I received a surprise vacation home! (To be there while my Mom passed away).
• Eventually work stress did catch up to me - but my boss thoughtfully gave me a nice long vacation! (By assaulting *while* firing me (for emailing in a vacation request while he was a having a bad (see:normal) day))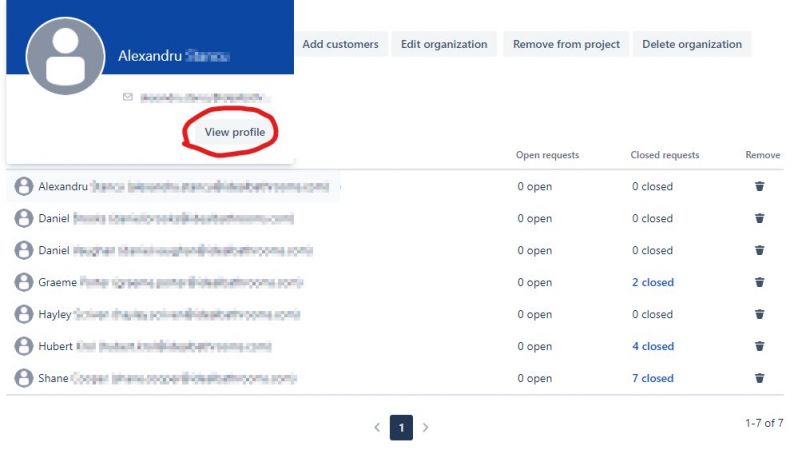 5
5 -
devRant ain't the same anymore. Too many sensitive snowflakes around. You bully them once or twice, they end up leaving the platform.
I'm running out of victims here32 -
Guys, long story short we found an investor for our app idea. What's the best route to go for us to get the people we need. Essentially we need a mobile app, but it may also need to be a kiosk, so should we look specifically for React Native developers to make a cross platform app or should we focus on ios, android, and kiosk apps natively? It involves access of sensitive information.
-
My new boss has such a sensitive ego. The latest is he asked me not to make big changes to 'his' code so whilst attempting to fix a bug in 'his' code I realised a big change was needed. I tell him at standup that he might want to take a look first and he agrees. A few days later he emails me to ask why I haven't finished work on the bug. When I reply he ccs other members of management to ensure he is deflecting any blame from himself (I dont even play the blame game to begin with).
The next day I email him that some tests are broken (he broke them but I just emailed him to bring his attention to it since he doesn't want me touching his code. And because it means he isn't testing properly - not that I would say that).
His reply - "are you going to fix them?"
Me - "ok"
The next morning be brings me into a meeting to ensure I agreed he wasn't to blame and that it was my fault and that he didn't understand my email response as it just said "ok".
I really can't stand such petty bs...2 -
What kind of tasks would you guys trust an intern with? Asking because I see a lot of people giving admin login for everything, access to production and sensitive info6
-
So I took this ocd sensitivity test 😂😂 . Apparently, I'm a perfectionist & need to take it easy lol.
Here's the link to play :
http://playbuzz.com/monicawoods10/... 8
8 -
Maybe not specifically "dev" but certainly a relatable rant to anyone here:
Moms small business gets "hacked," or standard spyware phone call from India let us save you for only $149 kind of crap. She obviously gets upset had a panic attack and thinks about all the sensitive shit on their network. Then, ONLY THEN, does she call me and the rest of the cavalry i.e. over payed and undermotivated IT guy to ask what's up why it happened and whose fault is it.
All is well, no ransom paid, no data lost or tangible damage done, but I am positive it will happen again, because it is impossible for people to internalize that they're the problem that money can't fix.
You clicked the unsolicited link. No amount of antivirus bloatware will ever be able to stop the monkey from trying to see what's in the box.
TheBut keep not paying me or people more qualified than me, and then scream and yell and pout when your shits gone and we can honestly say with a grin and a clean conscience that there is nothing we can do. -
I recently came across this article with some basic security advices, like use 2fa security key, encrypt your USB keys, don't use untrusted USB chargers / cables / ports (or use a data blocker cable if you need to charge your device). It made me think, how relevant are the USB-related threats and risks today? Do people really still use and carry so many wired USB devices, and just drop or plug them wherever?
The last time I used an USB device to transfer some important data was probably over 10 years ago, and for the love of god I don't know anyone who still carries an USB key with sensitive data with them on a daily basis, much less actively uses it. Besides, whoever still does that probably puts their USB key on the same keychain as their ID / access tag and a bunch of other keys (including a 2fa device if they use one) - they're not going to lose just some sensitive data, they're going to lose authentication and physical access devices as well, and that could turn a small data leak into a full-scale incident, with or without an encrypted USB device.
I'm also not sure about untrusted USB cables and ports, from what I've seen the USB outlets and cables are pretty much non-existent in public places, most places offer wireless charging pads instead (usually built into a hand rest or table surface).3 -
Anyone familiar with js bxSlider? Anyone have time and willing to slack chat or email with me to provide some assistance? Yes I looked and am trying to get some help on stackedoverflow as well but this is time sensitive for work :(7
-
Vivaldi browser is shit.
Simple isntructions on how to make most shitty browser ever:
1. Force users to use "really-fucking-long" password that will not match to any of their existing ones.
2. Invent some useless stupid "encryption password" (why does any normal browser work fine without that shit) and most ridiculous - automatically set it to be the same as the main password.
3. Of course you forget the pass you set because you dont remember what symbol you added 5 times in the end of your normal pass to fit their stupid rules.
4. You have to reset it
5. "Encryption password" does not reset with it, so you still dont remember it
6. Sync is not working!
7. If you think this is shitty enought, you are not right - they went futher. To reset that fucking "encryption password" you have to... ERASE ALL YOUR CLOUD DATA.
Fucking retarded piece of shit - never, never trust those morons who made this shit browser to sync any of your sensitive information.17 -
Does anyone from here working by GMX? I am specially looking for a sysadmin.
The story is the following. We can't send emails to GMX addresses in general. I've contacted my provider, and they said, that they've contacted GMX several times but no solution has been made so far. This was almost a month ago and the problem still persists.
If anyone from here willing to help me clear this mess, or just give some explanation, I would be grateful. We are loosing reputation as a company having to answer from a different email address.
If it is a sensitive info please give me a channel where we can speak about the details.
Please note I am not a sysadmin by the hosting company, i am simply a customer of theirs.14 -
What is the point of kubernetes "secrets" if it encodes the sensitive information as a base64 string if anyone can decode and read raw data using any base64 decoder tool?5
-
In Alpro soy milk range, the original one is often overlooked. There are ridiculously tasty soy vanilla, soy almond and professional coconut. But being THAT sensitive I can always distinguish like yea, here’s the soy and here’s the coconut purée. This always prevented me from focusing on just soy and how complex it really is.
So I tried the original soy milk and yes, the purest form was hidden in plain sight all this time. It’s just soy, pure soy, like a pokimane subreddit meetup. I love it.
It’s a moment of a purist finding a pure thing. This is the IDEA of soy milk, like Prolog is the idea of a declarative language. 6
6 -
I was once 'fraped' by a former (non technical) manager. I decided to retaliate by returning the favour while he was out of the office, but instead of the basic toilet humour I had been subjected to, I took it one step further and posted a status on his behalf, a sensitive cry for help, full of sadness, regret, alluding to betrayal and broken friendships. The texts, calls, concerned replies and messages on Facebook started flashing up his phone. He called me demanding I delete the status now as he couldn't figure out how to do so from his phone. Needless to say he was not happy. Highly recommended.1
-
So...im having a lot of issues with people messing with my emotions because of how sensitive I am.
I lost a lot of confidence in myself a while back and grew sensitive. I don't know what to do and I don't understand why people have to be so mean :(
A girl today was laughing at me cause I couldn't figure out something in class and I feel useless.
Two guys have already messed with my emotions and led me on.
A lot of people don't hang out with me like before and no one wants to hang out with me. Another girl said I was clingy and annoying and I don't understand what I'm doing wrong. I just want to be loved :((14 -
🐟💩The image i fetch from s3 is of type byte array
I return it to angular as an ArrayBuffer
Which then needs to be somehow converted to an image so i can fucking show it
Then after research i had to convert ArrayBuffer to Blob
And from Blob to URL encoded object which returns a string that now shows the full image in img tag
Somehow, by a sheer of trials and error i have just accidentally made a very secure way of fetching a very sensitive piece of document (verification document with user's personal data on it) and now in browser this is shown as blob:shit-image/random-hash. Not even the file extension. This means nobody can download this image. You fucking cant. Its a Blob motherfucker! Like a Blob Fish. It saves either a .txt when you try to save it (no idea how) and if you try to open the image in new tab it shows gibberish text. This means you can read-only this highly sensitive document image and not manipulate it, not even download it. Perfect. I have just made a very secure software by accident.
(this blob fish looks like my shit) 3
3 -
Looking for iOS and Android app developers to join startup in Rutherford, NJ area. Must be able to show portfolio of apps and have some published. Must be able to pull and compare data with sensitive databases (social security number, passport, birth certificate, etc) to verify user. You will be compensated hourly. Must sign NDA.
-
App idea: Platform for ongoing entrepreneurs
I just come from a start-up weekend. I really enjoyed the support we got from 17 different mentors (most of them founded in the past on their own).
Back home start-up funders don't have the access to that mentoring. My idea is to create a platform specialized for founders, where you can share your idea, believes and ask question all around your business.
I think especially in the early founding stages entrepreneurs are full of questions. Helping and discussing with other selfminded people is probably very enjoyable for us founder folks. A difference to the f.e. reddit concept: Users can create "diaries", a place where all storys, questions and posts about your project are stored. Reading a diary from beginning to end shall be a fun experience, reviewing your or others history of their "babys" and following the entrepreneurs thoughts through all stages of founding. Users of course can create multiple diaries.
Functionality will be suited for the listed usecase, for example a "Post as Anonymous" function will be added, if you have to deal with company sensitive data and more stuff like that.
What do you think about the idea? Do you like it? Would you use it? If not, tell me why?
Cheers -
Cybersecurity threats are a constant storm brewing on the horizon. Don't let your business become a sitting duck!
Qcom Ltd is your trusted partner for comprehensive network and IT security solutions. We go beyond basic antivirus software, employing a layered defense strategy that safeguards your valuable data and systems. Our expert team continuously monitors your network for suspicious activity, implements robust firewalls and access controls, and encrypts sensitive information to ensure it remains protected at all times.
With Qcom Ltd by your side, you can navigate the ever-changing cybersecurity landscape with confidence, focusing on running your business while we keep your network secure.
For More Info.
Tel:+44 (0) 203 150 1401
-
In the dynamic realm of software development, where the user interface meets the complex machinery behind the scenes, Back-End Expertise https://sombrainc.com/expertise/... emerges as the unsung hero. As businesses increasingly rely on digital platforms to connect, engage, and transact with their audience, the prowess of back-end development becomes paramount.
At its core, Back-End Expertise refers to the specialized knowledge and skills required to architect, build, and maintain the server-side of applications. While the front end dazzles users with intuitive interfaces and captivating designs, the back end silently weaves the intricate tapestry that ensures seamless functionality, robust security, and optimal performance.
The Back-End Symphony: Orchestrating Digital Harmony
Imagine a symphony where each instrument plays its part to perfection, creating a harmonious melody. Similarly, in the world of software, the back end orchestrates a symphony of databases, servers, and frameworks, ensuring that data flows smoothly, operations execute seamlessly, and applications respond promptly to user commands.
Back-End Experts are the virtuosos who write the code that makes applications tick. They delve into the intricacies of databases, crafting queries that retrieve and store data efficiently. They architect server-side logic, meticulously designing algorithms that power functionalities ranging from user authentication to complex business processes.
Security as the Forte: Safeguarding the Digital Fortress
In an era where data breaches loom as potential threats, Back-End Expertise becomes a formidable fortress. These experts implement robust security measures, safeguarding sensitive information and ensuring the integrity of digital ecosystems. Encryption, authentication protocols, and secure API integrations are the tools of their trade as they create digital bastions against cyber threats.
Optimizing Performance: The Need for Speed
User experience hinges on speed, and Back-End Experts understand the importance of optimizing performance. Through efficient coding practices, load balancing, and server-side optimizations, they strive to minimize latency and ensure that applications respond swiftly, even under heavy user loads.
Future Trends: Back-End Evolution
As technology evolves, so does the landscape of back-end development. Cloud computing, serverless architectures, and microservices are shaping the future of back-end expertise. Back-End Experts must adapt to these trends, embracing new tools and methodologies to stay at the forefront of innovation.
In conclusion, Back-End Expertise is the backbone of digital experiences. While users interact with the front end, the magic unfolds behind the scenes, where Back-End Experts craft the architecture that defines the reliability, security, and performance of applications. Their alchemy transforms lines of code into seamless digital experiences, leaving an indelible mark on the ever-evolving landscape of software development.1 -
A news/article/blog site and forum revolving around social issues where in addition to reading articles people can ask questions that are sensitive judgment free and get answers.
The aim is to slowly make the world a better more tolerant place8 -
Microsoft Teams login says password is incorrect then and for a captcha
I type it again but fails...
I'm like wtf... Could it be the captcha...
Which I entered in all lowercase
It doesn't say the captcha is case sensitive though..
Next few times it gives me captchas with k... Teehee me like 5 tries to login
Are we trying to verify passwords/humanness or whether I can somehow tell the difference between K and k?1 -
Android 13 will Unlock Certain Device Controls even when Locked
Android 13 is the newest operating system that will be available soon. The OS comes with a range of new features, one of which is unlocking certain device controls even when the device is locked. This is a game-changer that will significantly enhance the user experience.
Introduction
The Android operating system has undergone numerous changes since its inception. With every new release, users are treated to new features that enhance the overall user experience. Android 13 is no different, and it promises to revolutionize the way we interact with our devices. One of the most exciting features of Android 13 is unlocking certain device controls even when the device is locked. In this article, we'll take a closer look at this feature and explore its implications for users.
What is Android 13?
Before we delve into the details of Android 13, let's take a moment to understand what it is. Android is an operating system designed primarily for mobile devices such as smartphones and tablets. It was developed by Google and is currently the most widely used mobile operating system in the world. Android 13 is the latest version of this operating system, and it comes with a range of new features that will make it even more user-friendly.
Device Control Access
One of the most exciting features of Android 13 is the ability to access certain device controls even when the device is locked. This means that users will be able to control various functions of their device without having to unlock it. Some of the controls that will be accessible include the flashlight, camera, and voice assistant.
How will it work?
The process of accessing device controls when the device is locked will be straightforward. Users will only need to swipe left on the lock screen to access a new panel that will display the controls. The controls will be easy to use, and users will be able to activate or deactivate them with a single tap. This feature will make it easier for users to perform certain tasks without having to unlock their device.
Implications for Users
The ability to access certain device controls when the device is locked will have several implications for users. Firstly, it will make it easier for users to perform certain tasks quickly. For example, if you need to use the flashlight, you won't have to go through the process of unlocking your device and navigating to the flashlight app. Instead, you can simply access the flashlight control from the lock screen.
Secondly, this feature will enhance the security of the device. By limiting access to certain controls, users can ensure that their device remains secure even when it is locked. For example, the camera control will only be accessible when the device is unlocked, which will prevent unauthorized users from taking pictures or videos.
Other Features of Android 13
Apart from the device control access feature, Android 13 comes with several other exciting features. These include:
Improved Privacy Controls
Android 13 comes with improved privacy controls that give users more control over their data. Users will be able to decide which apps have access to their location, contacts, and other sensitive data.
Enhanced Multitasking
Multitasking has always been a key feature of Android, and Android 13 takes it to the next level. Users will be able to view multiple apps at the same time, making it easier to switch between them.
New Messaging Features
Android 13 comes with new messaging features that will make it easier for users to communicate with their friends and family. These include the ability to react to messages with emojis and the ability to schedule messages. 2
2 -
EY and ConsenSys announced the formation of the Baseline Protocol with Microsoft which is an open source initiative that combines cryptography, messaging and blockchain to deliver secure and private business processes at low cost via the public Ethereum Mainnet. The protocol will enable confidential and complex collaboration between enterprises without leaving any sensitive data on-chain. The work will be governed by the Ethereum-Oasis Project.
Past approaches to blockchain technology have had difficulty meeting the highest standards of privacy, security and performance required by corporate IT departments. Overcoming these issues is the goal of the Baseline Protocol.
John Wolpert, ConsenSys’ Group Executive for Enterprise Mainnet added, “A lot of people think of blockchains as the place to record transactions. But what if we thought of the Mainnet as middleware? This approach takes advantage of what the Mainnet is good at while avoiding what it’s not good at.”
Source : ConsenSys