Join devRant
Do all the things like
++ or -- rants, post your own rants, comment on others' rants and build your customized dev avatar
Sign Up
Pipeless API

From the creators of devRant, Pipeless lets you power real-time personalized recommendations and activity feeds using a simple API
Learn More
Search - "stolen"
-
Me: *desperately trying to finish a webpage before 5pm deadline*
Girlfriend: Why are you always so focused on your computer? You never pay attention to me.
Me: You know I have to work. Besides, you'll always be number 1 in my heart
Girlfriend: Aww that was cute. Okay I'll let you finish working
Me to me: ...arrays start at 0. *continues typing*
Disclaimer: this was stolen from /r/programmerhumor and I have no girlfriend13 -
Shit... I just got my phone stolen. Realized it 40 seconds post factum [left it at the shop counter and someone took it].
20 minutes later called the police [cuz I had to get home and use wife's phone].
5 min later poluce arrived
10 min later they got all they could from shop's security officer.
Police officer asks me to login my samsung acc on his phone. 2 minutes later we are on the way to the exact location my phone is at.
15 minutes later officer hands me my samsung 😁
got my phone back in less than an hour after theft.
maybe... Ummm... Maybe all this tracking thing is not that bad...?13 -
Stolen from an awesome book but my new favourite line ;)
Someone: “Can you repair my computer, it`s not working anymore?”
Me: “Do you call Leonardo Dicaprio when your Tv is broken?”7 -
So, my boyfriend's phone was stolen and my Google Drive account was synced on that phone. Also noticed that someone attempted to change my Gmail account. That dimwit does not know to whom he's messing with. Huh! I'm going to hunt that son of a gun and will make his life be tormented in hell! Muhuhuhahahahaha!undefined synced gmail acct change pass asap y u oblivious to env? bf phone not synced to samsung acct t_t19
-
// sorry, again a story not a rant
Category->type = 'Story';
Category->save();
Today at work I got a strange email
'about your msi laptop'
(Some background information, a few months ago I went on vacation and left my work laptop at home. Long story short some one broke in and stole my msi laptop)
So this email had my interest. I opened it and the content was something like:
Hi! My name is x, I clean/repair laptops partime and I noticed your personal information on this laptop, normally people whipe their data from their laptop before selling so this is just a double check, if the laptop was stolen please call me on xxx
If I hear nothing I'll assume its alright and will whipe your data
So of course I immediately called him, after a conversation I informed the police who is now working on the case7 -
I was registering for a website, and on a whim, I used this as my username:
null'); PRINT('Hello');--
And sure enough, the login system went down. The next day it was still down, so I went to Twitter to tell the people running the site that this was why, but to my surprise, I see them saying they had been hacked.
Based on the timing, I'm pretty sure they're referring to this, but they are saying user info was stolen. *facepalm*
They later said they stored passwords salted with a fixed salt and hashed with fucking md5, at which point I was glad not to have done any more business with them.
How incompetent can these fucking people be?!14 -
I fucked up again.
Someone needed a flashdrive for a presentation. Forgot that I keep personal code on on of them for backups (it's always nice when there is no reception to have an offline copy of my code, for instance when we go out into the bush or to remote areas).
I gave them my flashdrive. Forgot it had the code on.
Now someone at head office has taken my program, claimed it as their own - and has just earned themselves a decent amount of money (praised in the monthly company newsletter).
My program has been stolen (by my own stupidity) and butchered. It has been made into something that it was never intended to be.
Fuck that guy.13 -
Everything has to have MAC-Addresses. EVERYTHING!
(yes, I know. That's not one. But similar)
(stolen from https://twitter.com/istar_nil/...)
-
So some guy decided to steal my laptop. I don't know if they thought my machine wasn't happy with me or what but whoever did that, all I can say is your time is coming motherfucker.
I will always miss you 😭😭13 -
If a colleague went to a conference and checked their laptop with their luggage, you would think it would get stolen. Nope, it came back like this. It worked out really well for them, they got a new laptop and we all got a good laugh out of it.
 10
10 -
Dear recruiters,
if you are looking for
- Java,Python, PHP
- React,Angular
- PostgreSQL, Redis, MongoDB
- AWS, S3, EC2, ECS, EKS
- *nix system administration
- Git and CI with TDD
- Docker, Kubernetes
That's not a Full Stack Developer
That’s an entire IT department
Yours truly #stolen10 -
Little Jakob finds out you can open a js in (mobile) text editor.
Little Jakob finds an nether mod for early Minecraft PE editions (0.7 @ that time or so).
Little Jakob changes some number and vars and creates an Aether mod. (works the same like nether but other blocks&tools).
Little Jakob publishes it with screenshots in a video, gets 30.000+ views on youtube, mod reviews etc. There hasn't been an Aether mod before.
Little jakob feels badass.
2 years later I revited the video - and found out that the mod was licensed and I did something "illegal".
Seeked the internet and apologized to the original author (who was aware of this copy mod) - felt bad, he forgave me.1 -
K but why is this even possible through CSS...
Linked below is a pure CSS keylogger, i.e., now you can get your passwords stolen through a stylesheet. Keep your head on a swivel kids.
https://github.com/maxchehab/...13 -
<rant about devRant>
Can people please stop posting images stolen from someone else trying to get some points. I'm here to read rants and other interesting things you encounter while working with software development, not look at memes. Thank you.
</rant about devRant>12 -
guy: why do you use a vpn?
me: cause I don't want my info stolen
guy: nobody can steal info from wifi that's just in the movies.
me: ...
was on wifi in a Starbucks close to Atlanta9 -
GAHHHHHHHHHH! Damn USPS!!! Privatize them already! Stolen is more like it. It was a Gigabyte Aorus X470 Mobo, an AMD Ryzen 5 2600X CPU, and 16GB of memory. The postal service is a bloated, unresponsive, government run trainwreck. If people would just stop using them, they would shrivel up and blow away. ARRGH!!! 🔥☠️🔥☠️🔥
 23
23 -
Leave work with two working monitors at my desk, come back the next day to one monitor and a missing HDMI cable. Find out marketing took it for a presentation, don't get it back for three weeks. Finally get it back for a day, become super happy to finally have both monitors again. Come back the next day and PM has stolen my HDMI again, no extra HDMI cables in entire office. Apparently HDMI cables are valued like gold around these parts.10
-
Gets run over by truck. Laptop in peaces. Insurrance needed to be sure it was actually broken. Sends laptop to a repair center. They tell me its broken. Repair center asks if I want my laptop back. I said: yes pls. Get laptop back. RAM stolen SSD stolen. Reee! They forgot to send it back..... I mean, you did not have to take out those parts to see it i broken.
 12
12 -
So after my phone got stolen I am now using a series30 Nokia device, problem was synching contacts dumped from Google contacts. Run a Python script that modified the vcf into a format compatible with the series 30, never felt more of a hacker man than this
-
I hate this country!
This was the third time this month that the power cables got stolen. Looks like it is going to be takeouts and project planning on paper tonight. 12
12 -
Previously on devrant
https://www.devrant.io/rants/455085
This little shit is actually worried about her ideas getting stolen.
Do you think she'll pay me in stocks or pennies?
#INB4itsAShitIdea 14
14 -
Remember that fine girl that used to bedwet & was dirty in high school.
Then you met her recently, all looking hot & steamy.
That's PHP!
Stolen from the @unicodedeveloper om twitter2 -
.. for the first time I permanently lost access to one of my GPG keys that were actually in use. No revocation certificates, nothing in the keychains on any of my hosts... Keychain flash drive that got stolen had a copy of both, my fileserver used to have a copy of that flash drive until I deleted it to make room for a filesystem migration, and my laptop used to have one.. until I decommisioned it and shredded its hard drive to be deployed somewhere else...
fuck
I can't sign my git commits anymore, and I can't revoke the key either.
(╯°□°)╯︵ ┻━┻15 -
Holy shit! Albert Einstein is a real person!
My whole life I thought he was a theoretical physicist.7 -
not really a rant, but but i am intrigued...
got an email that my rockstar account (gta) email was changed.
changed the email and password and noticed that all the details were changed (nickname, date of birth etc) and the guy even posted on support asking to remove steam link (probably could not login). But rockstar requires a screenshot of user logged in to steam (as if that is hard to fabricate...), so he gave up :D
i'm not even mad, i'm wondering what's the guy's story. Probly bought a stolen account for cheap, hoping to play :(
Maybe i should just let him play the game, since i'm not... -
Well, well, well, my new year's gift:
Someone is jamming thousands of requests per second, and NO firewall. JWT tokens that expires in 3 HOURS.
Now MORE THAN 40K stolen.
But, where did it come from? https://devrant.com/rants/4961285/...16 -
The sell: “become a designer, change the world”
The reality: “become a designer, create Jira tickets for devs to fix stuff you’ve noticed” -
This rant goes to my best friend.
Fuck you!
You do not fucking argue with people for doing what they like! So what if I want to use linux? What fucking problem does that make? Am I now a hacker fanboy for wanting to use a terminal instead of fucking pointing and clicking on shit like a monkey? Am I not allowed to want my privacy and free open-source? What? I shouldn't browse internet without getting my personal info stolen? Oh, they're tracking criminals? Then why don't you install a camera in your fucking living room so you can help them out? And don't fucking get me started on why I don't want to use Windows 10.
Fuck fucking fuck fuck. I know he's a good friend but this fucking shit gets my blood boiling.8 -
So my boss is staring a new security oriented product and he asked one of my colleagues to prepare a presentation about the possible attacks on the product.
During the presentation there was a section on DoS attacks. The boss didn't know what DoS was and after a brief explanation, he interrupted the presentation and said DDoS is not a threat because there is no data stolen. This is a webapp.6 -
My previous manager: "Your code should hard to read, so our work is cant stolen by everyone".
Me: "Why?"
My previous manager: "Just do it"
Me: "Okay"
So, anyone can answer my 'Why?' question?
P.S: My previous Manager is PHP Programmer14 -
Me : Posts a original developer joke after thinking for 15 long minutes.
Gets 20 ++'s.
Me : Posts random computer science joke stolen from Facebook that everyone would have already seen.
Gets 200++'s.
Fuck this shit.45 -
I just got a company called me for interview for f**king 3 hours, I wasted 3 hours of them asking me stupid questions. I show them the projects I have done, as they demand. I spent another 1.5 hours of them questioning my intelligence of whether these projects are stolen , fraud, or copied from Youtube. Just because I am a self-taught and have multiple professional certs, they believed these are mine if I have a bachelor degree or a PHD in Computer science.10
-
Earlier i ranted about how someone hacked our site and he had our source code.
Now finally we found how was our site code stolen, thanks to @dfox he mentioned how can we pull code from got server at that time I checked trying commamds to dowload git folder but it was secure but later we found that we had another subdomain running for pur project and its git folder was not secured16 -
Necessary context for this rant if you haven't read it already: https://devrant.com/rants/2117209
I've just found my LUKS encrypted flash drive back. It was never stolen.. it somehow got buried in the depths of my pockets. No idea how I didn't look into my jacket for the entire time since that incident happened... But I finally found it back. None of my keys were ever compromised. And there's several backups that were stored there that have now been recovered too. Time to dd this flash drive onto a more permanent storage medium again for archival. Either way, it did get me thinking about the security of this drive. And I'll implement them on the next iteration of it.
For now though.. happy ending. So relieved to see that data back...
Full quality screenshot: https://nixmagic.com/pics/... 11
11 -
After two iPhones stolen in a month I decided to buy a Samsung and I really like it much more than iOS8
-
Had a stupid sales dude. Lost his driver's license due to reckless driving (and this was a few in a row including drunk driving) for 6 months. As it was his job required to drive around he got instantly fired.
So he had to leave laptop, iPad and phone with us (IT). His next stop was finance for the lease car but he was pissed, left the building and drove off.
Apparently rules are super shitty for the theft of a lease by the registered employee. So we could not really mark it as stolen. We alerted the police anyway and he was caught next week for driving without a license. So he went to jail and we got the car back5 -
First of all how the fuck you are able to tell that MY password is one of many that have been stolen? How you are able to get those stolen passwords AND WHY YOU ARE EVEN ABLE TO COMPARE THEM?! Are you storing as plain text or just randomly salt all stolen passwords and chceck if they are in your base?
Now that is an INSTAdelete. 8
8 -
taxes. what the actual fuck? I finally graduated and got my first 6 figure job, only to find out the federal government basically takes 1/3 of my pay??? WHAT??? Why are we all okay with this? I feel fucking robbed. I worked so hard to get here, so many sleepless nights, so many all nighters studying, just to get 1/3 of my money stolen from me? what the fuck?????50
-
Steeling crime in our office
My mug is stolen and being used by a colleague
I am suspecting the newbies that started 2 weeks ago19 -
Was busy today doing some house work. Everything was normal till afternoon.
Me thinking of using laptop noticed that there was no laptop
My office laptop and another bag was stolen from my home .
It had most of the production details and source code. Running behind police for help now.
Informed my boss too about this incident.
Will update on what happens tomorrow in office.
Fuck that person who stole my office laptop and destroyed my Peace.8 -
He read "Knowledge is a wealth that cannot be stolen"
Then saw me doing something with chmod and then he typed on his terminal
chmod 777 -R3 -
!rant
Bit of a shameless plug but...
I've been making Crypton.sh as my side project for the past couple of months and it's now ready for public consumption. Crypton.sh is a secure and encrypted SMS messaging solution in the cloud, with its original purpose to be a 2FA mobile number that cannot be stolen like a SIM card can be, the idea came about when someone I knew has their SIM card stolen via a SIM card swap scam (https://bbc.co.uk/news/...).
Originally it came about as that idea but grew into something bigger, now everything is encrypted and you can also have conversations with other people, but I'm testing things from time to time and more can follow. Crypton.sh makes sure that you can no longer worry about your SIM card being stolen by malicious hackers, or having a second account on Whatsapp, Telegram, Signal, Google and others. 5
5 -
I had good support.
I got access to a computer at 10 when my mother brought home the ones they used for education to avoid them being stolen
That was a couple of sinclair ZX80
I the got to go to 5 different programming courses over the next 4 years before being able to get a summer job at 14 to by my own spectravideo 128.
At 1) I started teaching through mother job and at 18 I wrote my first commercial program for my father.
I am now 50 and still in the business:)3 -
My december salary is delayed for a year (i’ll get paid around 2 or 3 january).
This broke af fireworks pic is how my new year looks like.
P.S Pic is stolen from facebook 4
4 -
work from home. desk and pretty much everything with it stolen in family dispute. I'm holding my laptop on a small nightstand. finally got a new pc today at least :/1
-
What's the best Slav programming language?
Hint: czech motorcycle, typically red
Stolen from Life of Boris Q&A -
- finish the app for my school
- FUCKING finish the google scholarship before time ends ._.
- learn git
- build a home fileserver, like a own cloud, which can be accesed even further away (has any one some tips on how to do it? ^^)
- attach a gps tracker to my moped, which I can then see on a mobile app (because I don't want it to be stolen...)
- rebuild my homevillages website
- learn python
- replace my android Java with kotlin
- apply to an internship for a software design company
- more and more and more
uff. ._.''
Hope you guys will have a nice and PRODUCTIVE 2018! :^)10 -
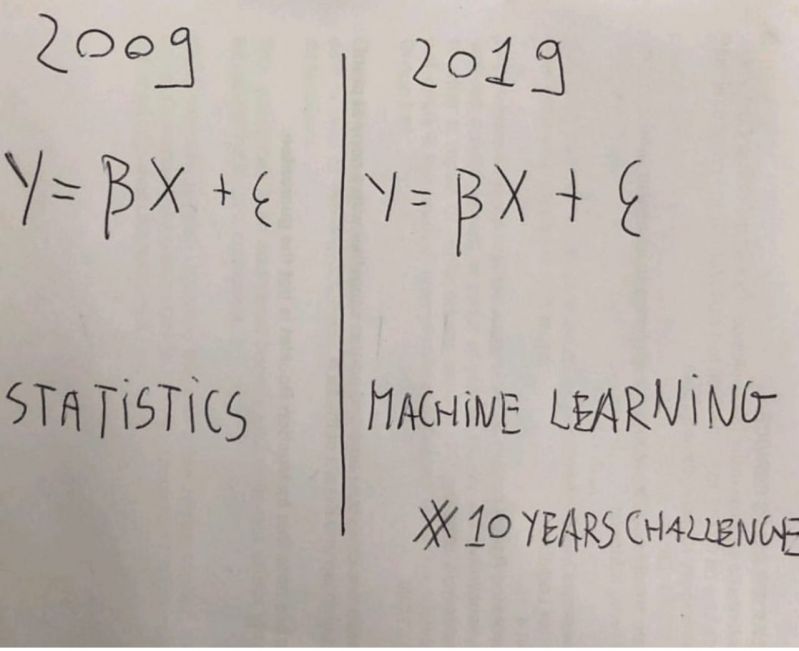
concerned parent: if all your friends jumped off a bridge would you follow them?
machine learning algorithm: yes.1 -
!rant
Today I almost lost my not a year old motorcycle.
I parked my motorcycle in a parking lot, kept the key on the seat and left. After an hour I realised that I hadn't brought my key after locking my motorcycle. I ran to the parking lot like a mad bull. Fortunately my motorcycle was not stolen and the key was still there on the seat. 😌 -
"Using MD5" !? What year are we in again?
NOTICE OF DATA BREACH
Dear Yahoo User,
We are writing to inform you about a data security issue that may involve your Yahoo account information. We have taken steps to secure your account and are working closely with law enforcement.
...
What Information Was Involved?
The stolen user account information may have included names, email addresses, telephone numbers, dates of birth, hashed passwords (using MD5)2 -
Start to read the book from Jaron Lanier "Who owns the Future". And suddenly realize that the company which offering us "free services" is trying to build a superior model of machine learning and read all of our behaviour.
Thus, i start to logout my facebook, twitter, instagram and all of my social media. But, i'm not the lucky one who could fight this "selling data practices", because I still use devices with "Android OS". My privacy stolen & sold is inevitable. What a Digital Life!23 -
Rant considering the latest Cyber attack and the news around it.
(A recap: a lot of Windows computers were infected with ransomware (due to security hole on Windows), which demanded 300$ in bitcoins to unlock data. After 3 days the price would double, and after 7 days the data was to be deleted)
1) In our country, one of the biggest companies was attacked (car factory). The production stopped and they got for around 1 000 000€ damage in less than 24h (1300 people without work). The news said that they were attacked because they are such a big company and were charged more, as the hackers "knew who they were dealing with" - another reason being the fact that the text was in croatian (which is our neighbor country), but noone realized that it is just a simple google translate of english text - which is obviously not true. The hackers neither know nor care who is hacked, and will charge everyone the same. They only care about the payment.
2) In UK whole (or large part) of medical infrastructure went down. The main thing everyone was saying was: "Nobody's data is stolen". Which, again, is obvious. But noone said anything about data being deleted after a week, which includes pretty much whole electronic medical record of everyone and is pretty serious.
And by the way, the base of the ransomware is code which was stolen from NSA.
All that millions and millions of dollars of damage could be avoided by simply paying the small fee.
The only thing that is good is that (hopefully) the people will learn the importance of backups. And opening weird emails.
P.S. I fucking hate all that 'hacky thingys' they have all over the news.5 -
Has anyone read the latest rant from Microsoft?
https://blogs.microsoft.com/on-the-...
<<Finally, this attack provides yet another example of why the stockpiling of vulnerabilities by governments is such a problem. This is an emerging pattern in 2017. We have seen vulnerabilities stored by the CIA show up on WikiLeaks, and now this vulnerability stolen from the NSA has affected customers around the world. Repeatedly, exploits in the hands of governments have leaked into the public domain and caused widespread damage.>>12 -
Can I complain most of the memes or jokes in this platform have been overused
I'm usually not the one to speak but sometimes I just see overused jokes or those stolen from Reddit.
Have some originality
(and before you ask, my own memes are on Reddit as well. I repost my own memes, not someone else's)11 -
Client: *Sends beautiful screenshot*. I created the newsletter (template) with chatgpt.
Me: Nice. Did it add the header and the footer as well ?
Client : I'm asking him to do it right now.
Me: Ok.
As a trash developer I fear for my job.
/s
Ughh 17
17 -
What's worse in an open office?
A) Music
B) People
(Shamelessly stolen from Twitter, credit @dustin)19 -
Apple corp. (Apple) founded in London in January 1968 by the members of the Beatles.
So Apple name is also stolen 😂6 -
I've finally found a goldmine of accurate job listings that don't include Windows shit-administration... So I'm thinking of sending out applications to all of them. Problem is, as you might recall from my previous rants, I had a flash drive with my GPG keypair on it stolen from me. I still haven't fully replaced the key (I made another one and published it but I'm not using it yet), and because I'm fairly confident that this flash drive's data has never been used (so likely just plugged into Windows and formatted), it's unlikely that I'm gonna bother rotating all of the contents that were on that flash drive.
That said however, my emails now all have signatures underneath them as follows:
Met vriendelijke groet / Best regards,
[my name]
- My outbound email is usually signed with my private key. If not, please don't hesitate to ask me about it through a different communication platform.
IMPORTANT: My keys have possibly been compromised. An encrypted flash drive on which this GPG keypair was stored has been stolen from me. I'm in the process of phasing out and replacing this key. Please do not use it to encrypt any emails to me anymore.
Not entirely sure whether I should remove or keep that last bit. As a potential employer, would you see this as a red flag (he's got encrypted data stolen from him, wtf that's incompetent), or as a nice thing to know that it was properly disclosed (so no secrecy around potential data breaches)? Both seem equally likely so I'm a bit confused about what I should do.10 -
Some hacker went through a lot of trouble to get around a minimum order amount on our site. And they’re still hitting us after Cloudflare issued a bunch of blocks. Well, there are some back doors I have to finish closing. I guess I’m lucky I’m just inheriting this site and I’m not the one who built it. But I’m still unlucky because I have to fix this mess. But damn hacker, why’d you go though all this trouble to get around existing validation. Go find another site to charge $1 amounts and test your stolen credit card info. Pretty please 🥺
-
Fuck the feelings of powerlessness and helplessness. when a friend comes crying for you for help with their hacked account and you keep asking them about what they did to protect it in the first place and they reply with nothing, no recovery email, no recover phone, no secondary verification, NOTHING. and you can do nothing but stand there and watch them cry while you can literally do nothing because there literally nothing you can do to retrieve their stolen accounts. FUCK BLACK HAT HACKERS.3
-
fuck people who need to be hacked to care about security.
i hope everyone who used that early ap scores gets their credit cards stolen because they don't know how to use a vpn.8 -
I'm fiddeling around with progressive web apps. I made something and hosted it on a subdomain. Today I made a typo and found my app on an other domain. All my assets and files are copied there. He even uses my SSL certificate.
It's not that spectacular. The app is nothing "revolutionary". It's just the first time it happend to me.
Have you ever found your code on other websites ? How did you react ?7 -
Legit questions!
How does facebook secures itself, we never heard news like facebook hacked, user data stolen, recently with ddos, twitter and other websites were affected but not Facebook?
Are they superhumans?9 -
People on election day: "OMG a subset of the machines are not working!!"
People who work in IT every single day: "lol no shit."4 -
Wakes up in the morning to find some fucking asshole has stolen my wifi reciever and I have a fucking deadline! Wtf is wrong with human beings nowadays?
Does anyone know a witch?2 -
Music - usually Pink Floyd. Loud enough to overpower my thoughts.
Worked even better when I could go on a bike ride to clear my head, but my bike got stolen 🤬4 -
So, at the very day I've been expelled, the university cancelled my MSDNAA account as if they thought they would punish me. (They got Office, Windows and everything Microsoft for students for free there)
It's sad but half of the students have no idea what MSDNAA is and how to use it. Then there is the other half who would still feel like they've been stolen from even if they got a MS product for free.
And then there is me. Because of math which is significantly impossible, I've been expelled. Fuck.4 -
My son used an ASUS Live L1 for about 3 years, and then we bought a new smartphone 1 year ago. Cool, except that the e-mail address he registered with Live L1, no longer exists, has been permanently deleted. His newest phone was stolen, and we took the L1 to set it up again. Only... Google wants him to log in to the original email (FRP Lock) that no longer exists.
How absurd, the L1 cell phone was never marked as stolen, and now we are unable to use our property. Is there a way for my son to convince google that the phone is his?
Microsoft, Google, Apple... They give the impression that people give money and use devices as if they were a "favor".12 -
Oh, me? I am so excited about all the computing power that's gonna be stolen from people who had updated their Intel CPUs last month.
I dunno what they're up to but I'm sure it's very exciting. I'm lost between Skynet and a one world government cryptocurrency mining they will use the power for.
What do you think?3 -
Great start to Halloween, phone has been stolen, and turned off so I can't track it. Oh, and I have no job so I can't get another right now. YAYAYAYAYAYAYAYAYAYAY3
-
Do you guys take your main laptop with you on vacation / travel abroad?
I can't afford to lose my laptop. Every work is saved in it. Some important files have been backed up to cloud. But that's it.
Can't risk getting it damaged or stolen or taken in custody when abroad.
But, if something in my server fucks up when I'm abroad, i want to be able attend it and get it addressed.
I'm thinking of buying a low cost portable laptop to use incase an emergency situation happens.
How do you guys manage such situation?9 -
Friend: where did you go to college, to do something like that?
Me: oh well I went to the university of my bedroom. -
My stress ball has been stolen!
I came in to work to an email alerting me to a bug in production. I copied the site to staging to work on the issue but I was unable to replicate bug. My rubber duck wasn't helping so I went to go bounce my ball off the wall when I realized I don't have a stress ball anymore.
I spent 7 hours working on the bug without a stress ball before finally fixing it. And now I'm ready to deal with the theft the old-fashioned way.3 -
Update on the previous rant(regarding office laptop stolen):
Company says there might be some deductions in salary. Trying to negotiate with them .
Would like to hear What's your company policy on stolen laptop?5 -
So my phone got stolen last night. FOR FUCK SAKE. I scrape together enough money to get another cheap phone after the last one broke, and now I need YET ANOTHER ONE WHEN I HAVEN'T GOT A JOB AND CAN'T APPLY FOR ONE WITHOUT ARGRFHUJGHIOSDJGBH:USKDGHISD:1
-
What the mods of Stackoverflow think every single person who ask questions look like.
Stolen from /r/programmerhumor
-
Anyone who subscribed to the notion of "Design Thinking" should have their kidneys stolen without anesthetics.6
-
Coaches know: it's all about the mindset!
Runtime exception? Mindset!
No video in Teams? Mindeset!
Money got stolen? Mindset!1 -
Real conversation with my shit bank
Me: Hey, I want to change the phone number associated with my card because I no longer have access to it. (aka stolen). I can't find the option to do so on your website anymore.
Them: Yeah, for security reasons you now have to come down to the bank (which involves standing in line for anywhere between 40 minutes and 2 hours) to do that simple change.
The actual fuck.12 -
Day and a half trying to fix a bug in a deprecated library :) thinking about commiting suicide right now (yes I stolen that quote back there)1
-
I know someone that’s constantly paranoid about being spied on by the government and fears companies stealing his code e.g. github, Microsoft etc.
His solution:
do nothing until we find a secure platform to write code on so that our ‘billion dollar ideas don’t get stolen’
Suffice to say that he’s a very bad coder, not that I’m really that good but compared to him I’m light years ahead.1 -
At school during my first Java project we had to make a simulation of a parking garage and what effects price changes would have in order to find the most optimal business model from some company.
At the project kick off.
School: "we will be checking your code for plagiarism. if you use code from the internet, even if its 2 lines you need to mention the source. otherwise you will fail this cource."
We go on to do the project.
Friend of mine who was in another class sees a group presenting a 2 days old version of my teams application. theres literaly a credits button that displays the names of the people that worked on it in a popup.
Me: mentions to a teacher that my project was stolen.
They literaly didnt even change the name and pulled the entire repository from github and handed it in.
The fucking teacher doesnt even check the code / git logs after i mentioned that the entire codebase was stolen from a public github repository.
There was an endless mountain of proof to support my claim such as our team members names hard coded in the code they handed in and about 500 commits from our accounts.
I will from now on NEVER EVER mention sources when i hand in code at school.1 -
The same people who are afraid of their data stolen by websites are totally fine with adding a phone number on take away websites.
What the fuck?
I hate it. It's a mandatory field. I don't know my phone number and if you call me there I won't even see it. If you can't deliver my order it must be my fault and so be it.14 -
How do you actually accredit code stolen from a project on github? Like it's not used commercially and it's going to be on github, too.
for context: i stole a java class from a minecraft mod. which is about 5% of the source project but makes more then 50% of my project.4 -
Dear Python devs who complain over state of Javascript. I politely ask you to fuck off because followin reasons. You are praising language witch does not have switch case statement(until 3.10), your async is just a stolen idea from JS and final argument that in pyhon there is one way to do everything is such bullshit when it comes to strings. For some reason i meet JS people who can write Python without much complaining but rarely another way around. Everytime Python fanboy sees JS they need instant tampons to stop their ass bleeding.7
-
!rant
Many out there say you should use 2 factor authentication with everything, but personally i feel lile that would just turn your phone into a sigle point of failure.
Phisical security is my primary worry, because loosing your phone or having it stolen yould pretty much lock you out of all your accounts.
Another thing is i don't know as much about android security, and i wouldn't be confortable managing it.
I have 2FA active for some key services, but imho a strong password is usually enough. I think its far more more importat for your overall security to avoid passwords re-use.
What do you think? Do you have 2FA on all the time?9 -
I just realized this is the dumbest marketing stunt McDonald's can come up with
https://thrillist.com/news/nation/...
The card is actually a phone case with your name etched into it.
1. How do I use it if I'm ordering online?
2. Why is the prize meant to encourage mobile ordering a physical card to use in stores?
3. So every time the winner takes out their phone, s/he is just asking to get mugged or have it stolen?3 -
My phone was stolen so that's why I wasn't getting here to rant about this, but today I had to make a back up and remembered.
adminer's export function doesn't export the tables in the correct order for import. Doesn't take foreign keys into account.
Dude, that's the whole point of a relational database, relations between tables; if you don't take that into account then what's the point?
Is this the same for the rest of database managers or is it just adminer? Please tell me this isn't normal.4 -
A few months back I tried to get the company I work for to invest in software to located and recover lost/stolen devices. I brought a few offerings to the table but I was told we didn't need to worry about that because it never happens and we already have software in place.
Fast forward a few months and I'm looking at the software we're using and it seems we haven't actually configured the computers to allow for tracking. I send a message to our CTO about this and point out that, in the event of a missing device, we can't actually relocate it. Not 5 minutes later a manager comes in to let us know that his computer is missing and may have been stolen because his car was broken into the previous night.
Well I'm laughing because this is just the kind of thing I needed to happen, and the manager is freaking out because he's afraid the CEO is going to be furious. I get a few emails from other members of the leadership team requesting we set up a meeting to go over our security and asset protection procedures.
So I finally get to start implementing some actual security protocols around here. And fortunately the lost laptop was actually recovered because it was left at a bar and not in the car when it was broken into. -
I don't know how to feel right now, I finally start a new dev job tomorrow, which I'm pretty excited about. In the other hand my bike just got stolen while I was visiting some friends at my old school.
As I would say in french Canadian:
JE TE SOUHAITE DE TE FAITE RENTRÉE DEDANS PAR UN CRISS DE GROS TRUCK EN CONDUISANT MON VÉLO MON ESTI D'ENFANT DE CHIENNE DR CÂLISSE2 -
Anyone seen the series "You Are Wanted Wanted" with the german actor Matthias Schweighöfer on Amazon? (Don't know if it's available outside of Germany)
Anyways.. they basically took scenes from various known digital works and put them in there. And whenever that happened i felt the cringe rising in me..:I
Examples are faked cctv recordings as seen in prison break, JASON with the red balloon, heavy rain and the all people are hacked and used thing from a black mirror episode..1 -
Co-workers conversation about the new Google Pixel... "I won't get it because they steal your soul, same reason why I don't have the iPhone with the finger print.. they want to have all your information... blah blah..."
I laugh, because they device doesn't matter... your info gets stolen in transit... so all your snap chat, IG DMs, and all of communication potentially at risk to be "stolen".
Example, Gov't splicing into underwater fiber optic cables and redirecting traffic to a data center...
Understand the tech.. please.2 -
Thank you, Google!
Stolen from Reddit, but still hilarious 😁
Credit: https://reddit.com/r/google/... 1
1 -
Agreeing to do iOS dev. I feel like my previous project has stolen 2 valuable years of my career from me.
-
At last! After my phone got stolen last year, I finally have a new one, so I can use devrant again. Feeling like arriving home again :-)6
-
Inspired by @gowtham-sai
Are there any ranters from Gdańsk, or 3city, Poland?
Meeting would be a nice thing :D5 -
Best thing about having two screens and rectangle is that you can collect all the security pop-ups on the smaller one and just continue working till it's actually convenient to restart everything. (Like after the meeting)
Seriously corporate security measures are completely fucked. Not only did they manage to slow down even Go compiles to a crawl with defender and other crap. Just tried to write 6 words to our PO. Focus got stolen by 4 of the 6 words typed.
One of them demanding to restart Firefox and that one can't be closed or moved out of the way unless you have some fancy window manager tool. This isn't security this is harassment.4 -
Yesterday i went to see a therapist ( i am a javascript developer). The therapist asked me what the problem was and i said i had to learn a new tech stack every 3 months. He then told me he was a php developer .....
Therapy works guys! no cap
P.S- This joke is stolen from the oldest book possible ( yes! as old as php)2 -
Three Layers of Security
As InfoWorld notes, all smartphones have three basic
elements of security. Your first major task as a mobile
user is to become aware of these layers and enable them
in your devices:
1. Device Protection: Allowing remote data "wiping" if your
device is ever lost or stolen.
2. Data Protection: Preventing corporate data from being
transferred to personal apps running on the same device
or personal network
3. App-Management Security: Protecting your in-app
information from becoming compromised. 6
6 -
Person: is it possible to learn binary?
Another person:
Yes.
Here's the dictionary: 0=0 1=1😏
Ps this is stolen from a quora quote
https://quora.com/Is-it-possible-to...
¯\_(ツ)_/¯ -
Getting Back Lost, Hacked or Stolen Crypto - Go to OMEGA CRYPTO RECOVERY SPECIALIST / HACKER
I lost my crypto to an online investment scam, After a successful recovery procedure, OMEGA CRYPTO RECOVERY SPECIALIST was able to retrieve my $125,000 worth of lost cryptocurrency. After my recuperation, I experienced an amazing sense of relief and appreciation. OMEGA CRYPTO RECOVERY SPECIALIST's professionalism and knowledge really impressed me, and I would heartily suggest them to anyone who has been duped by cryptocurrency frauds. But I also want to caution others about investing in cryptocurrencies and advise them to conduct due diligence before making any decisions. Because the cryptocurrency market is still mostly uncontrolled.
Visit; (omegarecoveryspecialist. co m
(Mail; omegaCryptos @ consultant. co m
WhatsAp; +1 (701, 660 (04 755 -
Two steps forward one back: Gets paid by client, phone gets stolen enroute. Now am just ranting from a tab
-
Last friday my old android phone stolen in public transportation. Things I miss so bad was my bookmarked links in a hn app1
-
i didn't want to leave home today, i still had a ton of code to deploy before a deadline.
i went out, phone gets stolen. and i end up spending a lot of money i am not supposed to spend.
thankfully, i had my WhatsApp logged in on my desktop PC and the latest update allows you to use the web version even when the device is offline, was able to reconnect with clients and assure them that i haven't disappeared with their money.
I feel numb, it's probably going to feel much worse when i wake up tomorrow, i just kept sleeping for the most of today which is kinda strange but i don't want to think much about it.1 -
HOW TO RECOVER STOLEN BTC FROM SCAM - OMEGA CRYPTO RECOVERY SPECIALIST
Recovering stolen btc/usdt/eth and other assets without professional help can be a daunting task, especially for individuals who lack the technical expertise required to trace and recover stolen assets. Therefore, it is essential to choose a reputable and experienced specialist to assist in recovering stolen assets. OMEGA CRYPTO RECOVERY SPECIALIST is a trusted and reliable option for recovering stolen BTC from scams. With over 22 years of experience in the field, they have a team of experts with diverse skills and knowledge. Reach out to them immediately
Website: omegarecoveryspecialist .c o m
Mail: omegaCryptos@consultant .c o m
Whatsap; +1 (701 660 (04 75)3 -
You know my earliest design relating to ML was something intended to mimic human evolution by creating large trees of ideas and rules regarding emotions and how they regulated decisions and priorities.
I somehow think that was a better approach. It was more complex but it was better.
and i could reproduce the stolen diagram from memory as well.
hey is it illegal for someone to sell the contents of a storage locker with your birth certificate in it ?2 -
Just got 3 Enki invites.
Use code: BBOHA441
If you don't know what Enki is, check out their website: https://enki.com/
As I was faster yesterday, I want to inform @futoricky and @wubstepper.
Hope you guys can catch an invite.
Text stolen from @szenjanos :D8 -
You know as I see these bastards having stolen my story over time I think wow
I put the effort in
I knew how to interview
I got the job
These creatures stole my resources by mimicking me often very poorly
Time to pay “you” the full amount owed and starve awhile -
I really really need to invent a trustworthy place to store photos and back date as necessary to ensure you always know where And when the really real time period has settled and give you all the stuff stolen which is being held in archives5
-
What is the Best Cryptocurrency Recovery Company - Go to OMEGA CRYPTO RECOVERY SPECIALIST
Omega Crypto Recovery Specialist stands out in the industry due to its exceptional expertise in cryptocurrency retrieval. The company boasts a highly skilled team that is dedicated to recovering lost or stolen cryptocurrency for their clients.
With a proven track record of success and a commitment to staying abreast of the latest developments in the crypto space, Omega Crypto Recovery Specialist has become a go-to option for individuals seeking assistance in recovering their digital assets.
Whether the loss is due to hacking, scams, or other fraudulent activities, Omega Crypto Recovery Specialist has the knowledge and capabilities to help clients reclaim their funds and restore financial security.
Homepage:.... omegarecoveryspecialist .c o m2 -
The jobs, can be stolen by A.I., must be some boring jobs, right? I don't think I'm interested in applying for these jobs at the first place...
-
I'm not going to have my source code stolen this time if noone steals yours. now how much more diplomatic a solution could there be eh ? guess they made the mistake of stealing heh.6
-
I'm Paul Ryan, and I'm excited to tell you that I've finally found a trustworthy cyber expert who deals with lost bitcoin issues/recovery. I lost all of my money after being misled into investing in stolen bitcoin a few months ago. Despite the fact that I was in a bad circumstance, my sadness was short-lived because a coworker had told me about (recoveryexpert at rescueteam dot com), a company that deals with Recovery Solution. I was able to reclaim the money that had been taken with the help of Recovery Expert. I was able to regain my $155,000 after being informed by another group of hackers that it had been permanently lost.2
-
CRYPTO RECOVERY SERVICE - MUYERN TRUST HACKER
( Email: muyerntrusted(@)mail-me(.)com )
The term "crypto theft" describes how fraudsters get and misuse cryptocurrency assets without authorization. The fact that the theft may cause monetary loss, interfere with corporate operations, and erode public confidence in virtual currency makes it a serious worry. Recovering stolen cryptocurrency requires specialized knowledge and techniques that professionals in the field possess. They have experience dealing with crypto theft cases, understand the tactics employed by cybercriminals, and can develop tailored recovery strategies to maximize the chances of successful retrieval. Muyern Trust Hacker demonstrates the highest level of professionalism in the realm of cryptocurrency theft when it comes to reclaiming stolen cryptocurrency. Their team of professionals offers a dependable and relatable recovery service by fusing technical proficiency, and personality. Having dependable expert assistance is essential for the safety of your cryptocurrency holdings. Along the way, Muyern Trust Hacker adds a dash of humor and personality to your team of experts who are committed to retrieving your pilfered cryptocurrency. Protect your investments and put your faith in Muyern Trust Hacker's expertise. Allow them to work with you to protect what is truly yours. Seeking expert assistance becomes crucial for people and organizations trying to recover stolen cryptocurrency as long as the threat of crypto theft persists. Muyern Trust Hacker differentiates by providing specialized techniques and the highest level of professionalism as a group of professionals committed to the recovery process. They have a reputation for being successful in recovering cryptocurrency monies that have been stolen thanks to their demonstrated track record and client endorsements. Individuals and companies can safeguard their priceless cryptocurrency assets and confidently negotiate the murky world of cryptocurrency theft by putting their trust in the knowledge of experts such as Muyern Trust Hacker. Do sure to contact Muyern Trust Hacker for a prompt and effective Bitcoin retrieval on Whats App +1-8-6-3-(606)-8-3-4-7
Regards. 12
12 -
so.
laptop
or
passport
or
handgun.
each has their merit.
all 3 have been stolen in the past.
that's probably your stupid game.
make someone look way to young to be me and put their picture on the passport. heh.13 -
your work laptop (or environment) get's stolen/lost/broken, when it's the last time you backed-up ?
and as a side question, how long will it take to get everything back up and running ?2